Active and passive liveness detection represent distinct approaches to verifying that identity verification participants are physically present rather than using photos, videos, or synthetic media. Active methods require users to perform deliberate actions like blinking or turning their head, while passive methods analyze biometric patterns without explicit user interaction, creating tradeoffs between security rigor and candidate experience friction.
Key Takeaways
- Active liveness detection requires user actions such as blinking, smiling, or head movements to confirm physical presence, providing stronger spoof resistance at the cost of increased interaction time and potential candidate dropout.
- Passive liveness detection analyzes depth, texture, and biometric markers without requiring deliberate user actions, offering faster processing and better candidate experience but potentially lower resistance to sophisticated attacks.
- Neither approach eliminates all identity fraud risk, and effectiveness varies significantly based on implementation quality, attack sophistication, and operational context.
- Candidate experience implications differ substantially, with passive methods showing lower abandonment rates and better accessibility for users with mobility limitations or assistive technology needs.
- Regulatory frameworks generally do not mandate specific liveness detection methods, though biometric privacy laws impose consent, disclosure, and data handling requirements regardless of technical approach.
- Cost structures vary between per-transaction pricing and subscription models, with total cost of ownership including integration complexity, support burden, and failure retry rates.
- Use case suitability depends on role risk profile, hiring volume, candidate demographics, regulatory environment, and organizational risk tolerance rather than technical superiority of either method.
- Hybrid approaches combining both methods may prove appropriate for organizations with diverse hiring needs across different role categories and risk levels.
Understanding Liveness Detection in Identity Verification
Liveness detection serves as a critical component of remote identity verification systems. It addresses the fundamental challenge of confirming that a person presenting credentials during digital onboarding is physically present rather than using a photograph, pre-recorded video, or digitally manipulated media. As remote hiring has become standard practice, organizations face increased exposure to presentation attacks where fraudulent actors attempt to impersonate legitimate candidates using various spoofing techniques.
The rise of sophisticated image manipulation tools and deepfake technology has elevated liveness detection from a technical nicety to an operational necessity for many hiring scenarios. However, the market presents two distinct technical approaches with different operational characteristics. Understanding these differences proves essential for organizations making verification technology decisions. The choice between active and passive methods involves evaluating tradeoffs across security effectiveness, candidate experience, implementation complexity, cost, and regulatory compliance requirements.
This assessment matters because organizations often receive conflicting guidance from vendors with financial incentives to promote specific technical approaches. Some providers position active liveness as categorically superior due to its explicit challenge-response mechanism, while others emphasize passive detection's user experience advantages and equivalent security for most threat scenarios. Reality proves more nuanced, with optimal selection depending on an organization's specific risk profile, hiring volume, candidate populations, and operational constraints.
Defining Active and Passive Liveness Detection
Active Liveness Detection
Active liveness detection operates through explicit challenge-response mechanisms that require users to perform deliberate, random actions during verification. The system presents instructions such as:
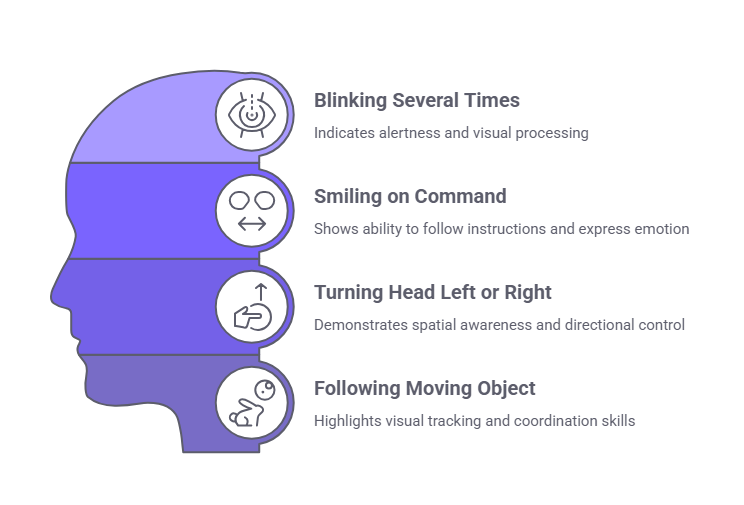
- Blinking several times
- Smiling on command
- Turning the head left or right
- Following a moving object with eye movement
These challenges aim to confirm the presented biometric comes from a living person rather than a static photo, pre-recorded video, or static mask. They require real-time, unpredictable responses that spoofing attempts cannot easily replicate.
The technical foundation involves motion analysis, temporal consistency verification, and behavioral pattern recognition. Systems evaluate whether movements exhibit characteristics consistent with genuine human physiology, including natural motion acceleration and deceleration, appropriate anatomical constraints, and coordinated facial feature movement. The unpredictability of randomly selected challenges aims to prevent attackers from pre-recording responses to anticipated prompts.
Passive Liveness Detection
Passive liveness detection analyzes biometric samples for indicators of liveness without requiring explicit user actions. These systems examine:
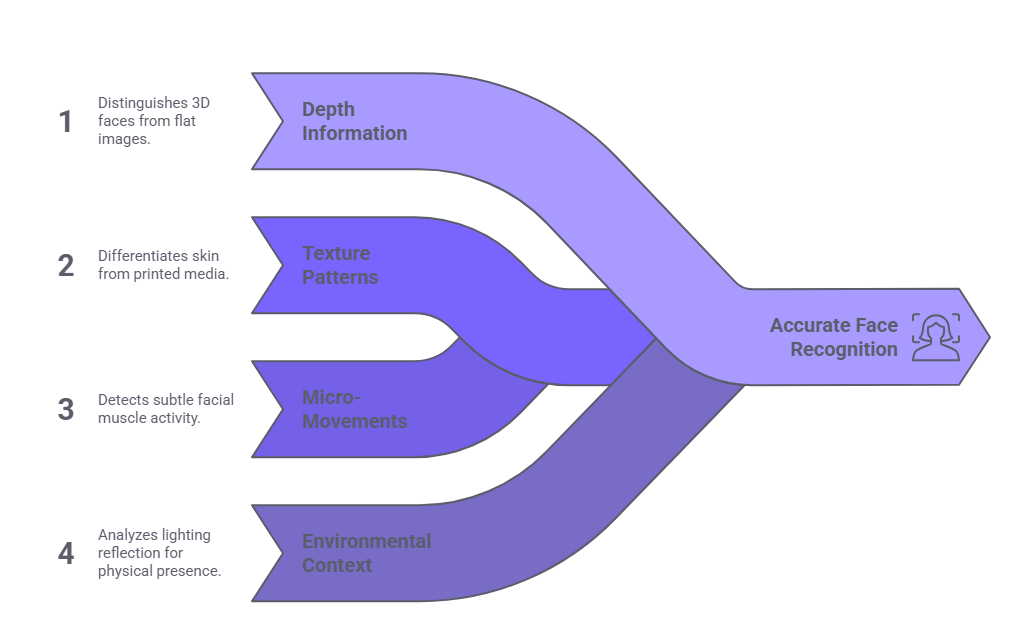
- Depth information to distinguish three-dimensional faces from flat images
- Texture patterns that differentiate skin from printed media or screen displays
- Micro-movements such as subtle involuntary facial muscle activity or blood flow patterns
- Environmental context like lighting reflection patterns consistent with physical presence
The technical approach relies on machine learning models trained on large datasets of genuine and spoofed samples to identify patterns distinguishing live subjects from presentation attacks. Processing occurs in the background during normal biometric capture, making the liveness check transparent to users. Advanced passive systems incorporate multiple detection signals, combining depth sensing, texture analysis, and behavioral biometrics to increase reliability.
Both methods share the common goal of presentation attack detection but differ fundamentally in how they gather evidence. Active detection explicitly tests responsiveness, while passive detection infers liveness from observed characteristics. This distinction drives the operational tradeoffs organizations must evaluate when selecting appropriate technology.
Technical Comparison Across Key Dimensions
Organizations evaluating liveness detection technologies benefit from understanding how active and passive approaches differ across critical performance and operational dimensions. Processing times, detection capabilities, and device requirements vary significantly by vendor implementation, network conditions, device capabilities, and user factors.
| Dimension | Active Liveness Detection | Passive Liveness Detection |
| Detection Mechanism | Challenge-response requiring deliberate user actions (blink, smile, head turn) | Background analysis of depth, texture, micro-movements without explicit interaction |
| User Interaction Required | High: users must follow on-screen instructions and perform specific actions | Minimal: users simply position face within frame |
| Typical Processing Time | Vendors report ranges of 15 to 45 seconds including instruction reading and action performance | Vendors report ranges of 2 to 8 seconds for capture and analysis |
| Spoof Resistance Level | High for printed photos and simple video replay; variable for deepfakes and sophisticated masks | Moderate to high depending on implementation; relies on multi-signal analysis |
| False Rejection Rate | Variable by implementation; user action requirements may increase legitimate user failure in some scenarios | Variable by implementation; passive analysis typically presents fewer user-error opportunities |
| Device Requirements | Standard camera; some implementations require specific frame rates or resolution | May require depth sensors for optimal performance; RGB camera sufficient for basic implementations |
| Accessibility Considerations | User action requirements may create barriers for some individuals with mobility limitations, neurological conditions, or who use assistive technology | Generally presents fewer interaction barriers, though organizations remain obligated to provide reasonable accommodations regardless of method selected |
This comparison reveals no absolute winner across all dimensions. Active detection provides stronger assurance against certain attack types but imposes greater candidate friction and accessibility challenges. Passive detection offers superior user experience and faster processing but may require more sophisticated hardware or implementation to achieve equivalent security levels. Organizations must weigh these tradeoffs against their specific operational requirements.
Security Effectiveness and Attack Resistance
Active Liveness Detection Capabilities
Active liveness detection reliably defeats printed photographs and simple video replay attacks. The requirement to perform unpredictable actions in real-time prevents static image presentation and pre-recorded video from succeeding. This provides robust protection against the most common, low-sophistication presentation attacks that represent the majority of fraud attempts in employment verification contexts.
However, active methods face challenges against more sophisticated attacks:
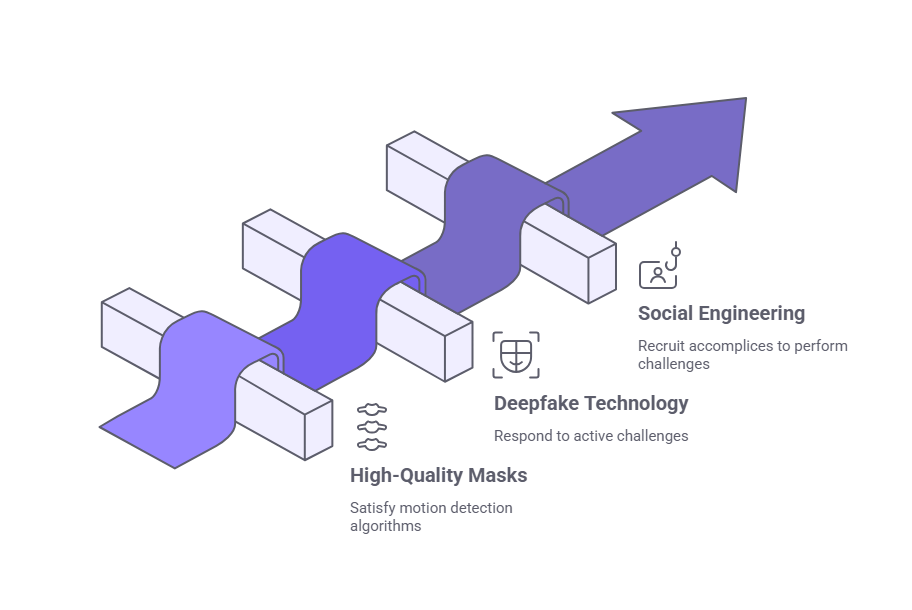
- High-quality three-dimensional masks can perform movements that satisfy motion detection algorithms, particularly when attackers invest resources in creating masks with flexible facial features.
- Deepfake technology capable of real-time facial manipulation can potentially respond to active challenges, though this requires significant technical capability and resources beyond typical employment fraud scenarios.
- Social engineering attacks where fraudulent actors recruit accomplices to perform verification challenges bypass liveness detection entirely, as the system correctly identifies a live person despite that person not being the claimed identity.
Passive Liveness Detection Capabilities
Passive liveness detection excels at detecting flat image presentations through depth analysis and texture evaluation. Systems analyzing multiple signals, including infrared patterns, blood flow detection, and micro-expression analysis, achieve high reliability against photographs and basic video replay. Advanced implementations incorporating depth sensors or specialized imaging demonstrate strong resistance to printed media and screen-based attacks.
Passive methods may struggle more than active approaches against sophisticated three-dimensional masks and certain deepfake presentations, particularly when implementations rely primarily on RGB camera analysis without supplementary sensors. However, multi-modal passive systems combining depth sensing, texture analysis, and behavioral biometrics can achieve security effectiveness comparable to active methods for most practical threat scenarios.
Shared Vulnerabilities
Both approaches share vulnerability to certain attack vectors:
- Neither method addresses identity document fraud
- Neither prevents synthetic identity creation
- Neither guards against insider threats where authorized individuals assist fraudulent actors
Liveness detection forms one component of comprehensive identity verification but cannot substitute for document authentication, database cross-referencing, and procedural controls. Organizations should view liveness detection as reducing presentation attack risk rather than eliminating identity fraud comprehensively.
Many organizations determine that for employment verification scenarios where anticipated threats primarily involve opportunistic actors using photographs or basic impersonation, well-implemented passive systems offer appropriate fraud risk mitigation aligned with their risk tolerance. Security sufficiency determinations should be based on organization-specific risk assessments rather than general industry characterizations. Roles with extraordinary security requirements, or organizations operating in demonstrably high-fraud environments, may justify active detection's additional security margin despite user experience costs.
Candidate Experience and Hiring Funnel Impact
Active Liveness Detection Experience Challenges
Active liveness detection introduces notable friction into the verification process. Candidates must complete multiple steps:
- Read and understand instructions
- Position themselves appropriately
- Perform required actions within specified timeframes
- Potentially retry if initial attempts fail
This multi-step interaction increases total verification time and creates failure points where legitimate candidates abandon the process. Industry data suggests active liveness verification exhibits higher abandonment rates than passive approaches, with dropout increasing among certain demographic groups. Older candidates, users with limited technical proficiency, individuals using mobile devices in suboptimal lighting conditions, and people with mobility limitations or neurological conditions affecting voluntary facial movement face elevated failure risk.
The candidate perception impact extends beyond immediate abandonment. Applicants who successfully complete active liveness checks sometimes report the experience as invasive, awkward, or unnecessarily complicated. In competitive talent markets, particularly for specialized roles where candidates evaluate employer brands critically, verification friction may influence acceptance decisions.
Passive Liveness Detection Experience Advantages
Passive liveness detection minimizes user burden. Candidates simply position their face within a frame, and analysis occurs transparently in the background. The interaction feels similar to taking a standard photo, requiring minimal instruction comprehension or deliberate action performance. Processing completes in seconds rather than the extended duration active methods require.
Lower friction translates to measurably lower abandonment rates. Organizations implementing passive liveness detection report:
- Higher completion rates
- Fewer support inquiries related to verification difficulties
- Improved candidate satisfaction scores
Passive methods may present fewer interaction barriers for some users with disabilities, though organizations remain obligated to provide reasonable accommodations under the Americans with Disabilities Act regardless of which liveness detection approach they implement. Organizations should ensure their identity verification processes include accommodation procedures for candidates who cannot complete standard verification methods.
Mobile device performance differences between active and passive approaches warrant consideration. Active liveness detection relies heavily on consistent frame rates, clear real-time video processing, and stable connections to receive and execute challenges. Mobile devices with varying processing power, camera quality, and network conditions introduce inconsistency. Passive methods, particularly those analyzing single high-quality images rather than video streams, demonstrate more consistent cross-device performance.
Use Case Suitability Framework
When Active Liveness Detection Is Most Appropriate
Active liveness detection proves most suitable for specific high-risk scenarios:

- Fiduciary roles where employees handle financial transactions, manage organizational assets, or maintain accounts with disbursement authority
- Sensitive system access including network administrators, database managers, and roles with privileged system access
- Safety-sensitive positions where identity fraud could enable individuals with disqualifying backgrounds to access roles affecting public safety
- High-fraud environments such as certain financial services sectors or cryptocurrency operations
- Regulatory compliance scenarios including government contracting, financial institution hiring subject to Bank Secrecy Act provisions, or healthcare roles with controlled substance access
- Security clearance roles requiring background investigations by government agencies
Over the course of time, I came to appreciate the fact that hiring in today's era cannot be based solely upon skills since it involves establishing trust in a world of simulations. The choice of either an active or a passive system of detection of liveness in the interview process involves weighing different pros and cons of how we are going to balance our priorities and protect ourselves while also maintaining our empathic side. When we design hiring processes with both protection and empathy in mind, we do more than prevent fraud, we create a space where real people can show up confidently. That, to me, is what modern HR should stand for.
When Passive Liveness Detection May Be Appropriate
Many organizations use passive liveness detection for high-volume hiring scenarios such as customer service, retail, hospitality, or entry-level positions after conducting role-specific risk assessments. Organizations should evaluate their specific fraud risk profile, regulatory environment, and operational requirements rather than relying solely on general industry practices when determining appropriate identity verification rigor.
Passive liveness detection may be appropriate for:
- Roles with limited system access, close supervision, and minimal authority over organizational resources
- Organizations hiring in competitive talent markets where candidate experience significantly influences acceptance rates
- Seasonal or temporary hiring scenarios where large applicant volumes and compressed timelines create operational constraints
- Positions where risk assessments indicate lower fraud impact potential
Hybrid Approaches
Hybrid approaches merit consideration for organizations with diverse role portfolios. Many vendors support configurable verification rigor, allowing organizations to:
- Apply active liveness detection selectively to high-risk roles
- Use passive methods for general population hiring
- Optimize the security-experience tradeoff across different use cases
This segmentation prevents both over-engineering low-risk verifications and under-protecting sensitive positions.
Decision criteria should include explicit consideration of candidate demographics. If target populations include significant representation of older workers, individuals in regions with variable mobile device quality, or persons with potential accessibility needs, passive detection's lower barrier to completion reduces discrimination risk and improves hiring process equity.
Implementation and Cost Considerations
Pricing Structures
Pricing models vary significantly across vendors:
- Per-transaction fees with rates influenced by monthly volume tiers and contract term commitments
- Subscription-based pricing with included transaction allotments and overage fees beyond specified volumes
- Active liveness detection typically carries modestly higher per-transaction costs than passive methods
Organizations should calculate total cost of ownership including factors beyond direct verification fees:
- Integration complexity affecting implementation costs
- Support burden, with active methods generating more candidate assistance requests
- Failure retry rates impacting effective cost per successful verification
Vendor Landscape Considerations
The vendor landscape includes:
- Specialized identity verification providers
- Background screening companies incorporating liveness detection into comprehensive offerings
- Platform providers bundling verification with applicant tracking or onboarding systems
Vendor selection should consider not only liveness detection capabilities but also broader service quality, compliance support, audit documentation, customer service responsiveness, and financial stability.
Technical Integration Requirements
| Deployment Model | Characteristics | Best For |
| Cloud-based SaaS | Minimal infrastructure investment; vendor-hosted processing | Most organizations seeking quick deployment |
| On-premises | Greater data control; higher implementation complexity | Organizations with data residency requirements |
| Hybrid architecture | Flexible data handling; balanced control and convenience | Enterprises with heightened security protocols |
| Mobile SDK integration | Embedded in proprietary applications; seamless experience | Organizations with custom candidate portals |
Device and browser compatibility affect operational smoothness. Passive liveness systems relying primarily on RGB camera analysis demonstrate broad compatibility across devices and browsers. Active systems requiring specific frame rates or video processing capabilities may encounter compatibility issues with older devices, certain browsers, or corporate networks with restrictive firewall policies.
Data Retention and Privacy Requirements
Organizations should establish clear biometric data retention and deletion policies aligned with applicable privacy laws. Vendor contracts should specify data storage duration, deletion obligations upon contract termination or candidate request, and whether the vendor retains biometric data for its own purposes. Many privacy frameworks require organizations to retain biometric data only as long as necessary for the specified purpose.
Data Processing Location Requirements
Data residency and processing location requirements are critical compliance considerations for organizations subject to data localization regulations or hiring internationally. GDPR restricts transfers of biometric data outside the European Economic Area absent adequacy decisions or appropriate safeguards such as standard contractual clauses. China's Personal Information Protection Law requires security assessments for certain cross-border data transfers. Organizations must verify that vendor data processing locations and transfer mechanisms comply with applicable data protection laws in all hiring jurisdictions.
Contract Considerations
Contract terms warrant careful evaluation:
- Minimum volume commitments
- Termination provisions
- Price increase caps
- Service level agreements for uptime and processing speed
- Data deletion obligations upon contract termination
- Audit rights allowing review of vendor security practices
Organizations should negotiate these terms carefully, particularly given the sensitive nature of biometric data processing.
Regulatory and Compliance Context
Federal Regulatory Framework
The Fair Credit Reporting Act may apply when organizations use third-party consumer reporting agencies to conduct background checks that include identity verification. Organizations should determine whether their vendor relationship and the nature of information provided constitute a consumer report under FCRA, as this determination affects compliance obligations including authorization, disclosure, and adverse action procedures.
When FCRA applies, compliance requires written authorization from candidates before obtaining consumer reports. If information from such reports contributes to adverse employment decisions, employers must provide pre-adverse action notices that include a copy of the consumer report and a summary of FCRA rights, followed by final adverse action notices after a reasonable period.
State Biometric Privacy Laws
Several states and localities have enacted biometric privacy laws with varying requirements. Illinois' Biometric Information Privacy Act (BIPA) is among the most comprehensive, requiring written informed consent, disclosure of collection purpose and retention duration, written retention and destruction schedules, and prohibiting selling or profiting from biometric data. BIPA also provides a private right of action, making Illinois a particularly litigious jurisdiction for biometric privacy claims.
Texas, Washington, Arkansas, California, Montana, New York City, Oregon, and Vermont have enacted biometric privacy provisions with varying scope and requirements. Organizations should consult legal counsel to ensure compliance with applicable state and local biometric privacy laws in jurisdictions where they hire.
| Jurisdiction | Key Requirements |
| Illinois (BIPA) | Written informed consent; disclosure of collection purpose and retention duration; written retention and destruction schedules; prohibition on selling biometric data; private right of action |
| Texas | Informed consent; retention policy disclosure; security safeguards |
| Washington | Notice and consent requirements; purpose limitation |
| California (CPRA) | Enhanced protections for biometric information; disclosure and consent requirements |
| Other jurisdictions | Arkansas, Montana, New York City, Oregon, and Vermont maintain varying biometric privacy requirements |
Biometric privacy laws typically require separate, explicit consent for biometric data collection, distinct from general employment application authorizations. Consent mechanisms should clearly identify what biometric data will be collected, the specific purpose, and how long it will be retained. Bundling biometric consent into general terms of service may not satisfy legal requirements in jurisdictions with specific biometric privacy laws.
State Data Security Laws
State data security laws may impose specific requirements for protecting biometric data collected during liveness detection. Organizations should assess whether state data breach notification laws, data security statutes, or consumer privacy frameworks apply to their liveness detection implementations and hiring jurisdictions.
International Data Protection
The General Data Protection Regulation classifies biometric data as a special category requiring enhanced protection. Organizations subject to GDPR must:
- Establish lawful processing bases
- Implement appropriate technical and organizational security measures
- Maintain processing records
- Honor data subject rights including access, rectification, and deletion
State consumer privacy laws including the California Privacy Rights Act, Virginia Consumer Data Protection Act, and similar frameworks in Colorado, Connecticut, and Utah grant consumers rights regarding personal information processing. While general privacy laws typically apply less stringent requirements to employment contexts than to consumer transactions, organizations should verify that liveness detection implementations support data subject access requests and deletion obligations where applicable.
Documentation and Audit Trails
Documentation requirements may differ between active and passive approaches primarily in what evidence each method produces. Active liveness detection generates explicit records of challenges presented and candidate responses, creating detailed audit trails demonstrating verification rigor. Passive systems document analysis results but produce less granular evidence of the detection process.
No regulatory framework currently mandates active over passive liveness detection or vice versa. Compliance focuses on whether organizations implement reasonable identity verification appropriate to role risk, maintain required documentation, obtain proper consent for biometric processing, and protect collected data adequately.
Organizations should consult legal counsel when implementing biometric verification systems to ensure alignment with applicable federal, state, and international regulations. Vendor contracts should specify compliance responsibility allocation, particularly regarding data protection obligations and regulatory change adaptation.
Addressing Common Misconceptions
Organizations evaluating liveness detection technologies frequently encounter persistent misconceptions that create confusion during vendor evaluation and technology selection processes.
Misconception: Passive Detection Is Less Secure
The belief that passive liveness detection is categorically less secure than active methods oversimplifies technical reality. While active detection's explicit challenge-response mechanism provides strong protection against certain attack types, well-implemented passive systems incorporating multiple detection signals achieve comparable security for most practical threat scenarios. Security effectiveness depends more on implementation quality, sensor sophistication, and machine learning model training than on the active versus passive distinction.
Misconception: Active Detection Is Always Superior
The assumption that active liveness is always the superior choice ignores legitimate operational tradeoffs. Maximum security against theoretical threats may not be justified when an organization's actual threat environment consists primarily of opportunistic attacks that passive detection defeats reliably, particularly when balanced against candidate experience costs, accessibility barriers, and completion rate reductions.
Misconception: Liveness Detection Eliminates All Fraud
The misconception that liveness detection eliminates all identity fraud creates false security confidence. Liveness detection addresses presentation attacks specifically, confirming physical presence during verification. It does not validate that the presented individual matches claimed identity documents, prevent synthetic identity fraud, detect document forgery, or address insider threats.
Misconception: Most Advanced Technology Equals Due Diligence
Some organizations believe they must implement the most advanced liveness detection technology available to demonstrate due diligence. In reality, reasonable identity verification involves selecting controls appropriate to role-specific risks and regulatory requirements. Implementing enterprise-grade active liveness detection for low-risk, high-volume hiring may constitute over-engineering that wastes resources without commensurate risk reduction.
Misconception: Technology Selection Is Permanent
The assumption that liveness detection technology remains static overlooks rapid evolution in both detection methods and attack techniques. Both active and passive approaches continue advancing, with vendors incorporating improved algorithms, additional sensor modalities, and enhanced machine learning models. Organizations should evaluate vendor research investment and update cadence rather than viewing technology selection as permanent.
Decision Framework for Organizations
Organizations can structure liveness detection selection through systematic evaluation of key decision factors.
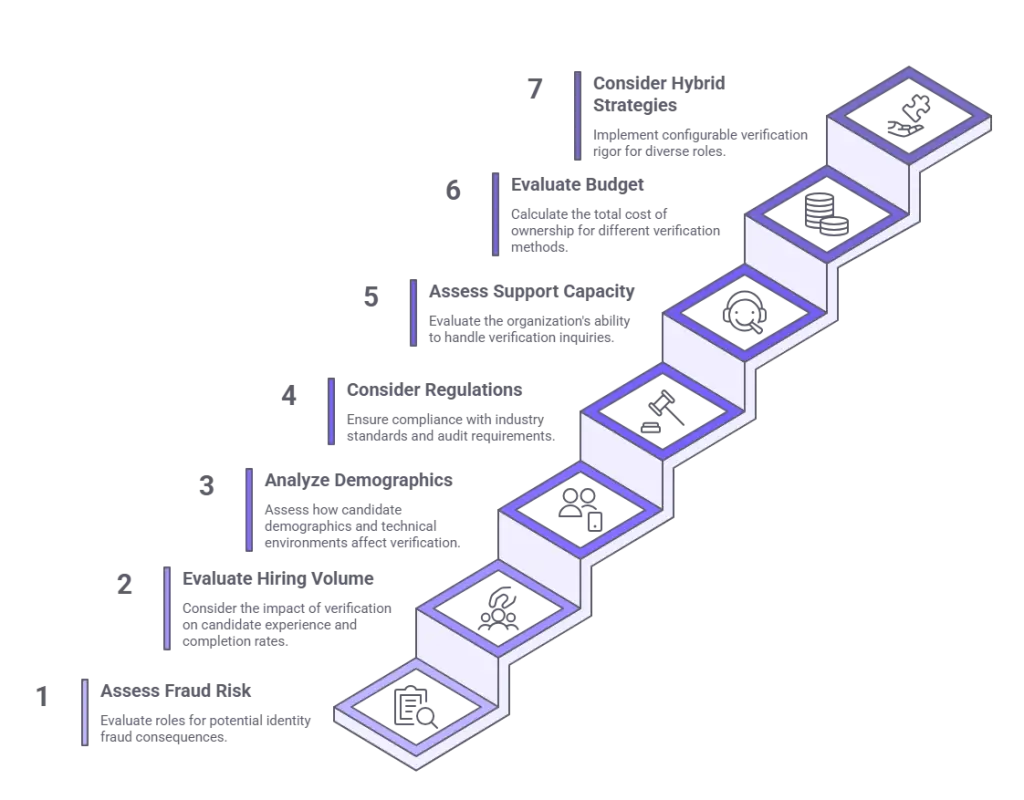
Step 1: Assess Role-Specific Fraud Risk
Consider whether positions involve:
- Fiduciary responsibilities
- Access to sensitive systems
- Safety-sensitive duties
- Other characteristics elevating identity fraud consequences
Document this risk assessment to support technology selection rationale and demonstrate due diligence. High-risk roles justify more rigorous verification, potentially including active liveness detection, while lower-risk positions may reasonably use passive methods based on specific risk evaluations.
Step 2: Evaluate Hiring Volume and Candidate Pool Dynamics
Organizations hiring thousands of candidates annually in competitive markets should carefully weigh:
- Candidate experience implications
- Completion rate differentials
- Applicant pool impact of potential percentage point differences in verification completion rates
High-volume scenarios where small completion rate improvements yield significant applicant gains favor passive detection's lower friction.
Step 3: Analyze Candidate Demographics and Technical Environment
Consider whether target populations include:
- Demographics that may struggle with active liveness challenges
- Users commonly applying via mobile devices in variable conditions
- Significant representation requiring accessibility accommodations
Organizations committed to hiring process equity should weigh these factors carefully.
Step 4: Consider Regulatory Environment and Audit Requirements
Verify that selected technology satisfies:
- Roles subject to heightened regulatory scrutiny
- Industries facing examiner review of identity verification procedures
- Entities with contractual obligations to implement specific security controls
Document how the chosen approach meets applicable standards.
Step 5: Assess Organizational Support Capacity
If candidate support infrastructure cannot easily absorb increased verification-related inquiries, passive detection's lower support burden may prove operationally preferable. Organizations with robust support capabilities can more readily accommodate active detection's interaction complexity.
Step 6: Evaluate Budget Constraints Realistically
Calculate total cost of ownership including:
- Transaction fees
- Integration costs
- Support burden
- Failure retry expenses
Determine whether modest cost differentials between active and passive approaches represent material budget concerns or negligible differences.
Step 7: Consider Hybrid Strategies
For organizations with diverse role portfolios, implementing configurable verification rigor allows optimization across different use cases, applying appropriate security levels without uniform over-engineering or under-protection.
Organizations should document decision rationale clearly, including risk assessment, operational requirements, regulatory considerations, and cost-benefit analysis. This documentation supports audit defensibility, facilitates future technology reassessment, and demonstrates thoughtful procurement decision-making.
Conclusion
Active and passive liveness detection represent distinct technical approaches with different operational characteristics rather than a simple superior-inferior relationship. Organizations should evaluate security effectiveness, candidate experience impact, implementation requirements, cost structures, and regulatory compliance needs within their specific operational context. Optimal selection depends on role risk profiles, hiring volumes, candidate demographics, and organizational priorities, with many organizations benefiting from hybrid approaches applying appropriate rigor across different use cases.
Frequently Asked Questions
What is the main difference between active and passive liveness detection?
Active liveness detection requires users to perform deliberate actions such as blinking, smiling, or turning their head to prove physical presence. Passive liveness detection analyzes depth, texture, and biometric patterns without requiring explicit user interaction. Active methods provide explicit challenge-response verification, whereas passive approaches infer liveness from observed characteristics during normal biometric capture.
Is active liveness detection more secure than passive methods?
Active liveness detection provides strong protection against printed photos and video replay through its explicit challenge mechanism. However, well-implemented passive systems incorporating multiple detection signals achieve comparable security for most practical employment fraud scenarios. Security effectiveness depends more on implementation quality and sensor sophistication than the active versus passive distinction. Organizations should evaluate specific vendor capabilities and conduct role-specific risk assessments rather than assuming categorical superiority.
How does liveness detection affect candidate experience and hiring completion rates?
Active liveness detection introduces greater friction through instruction reading, action performance requirements, and longer processing time, resulting in higher abandonment rates. This particularly affects older candidates, users with mobility limitations, and those on mobile devices. Passive detection minimizes interaction requirements and completes verification faster, demonstrating lower dropout rates. Organizations should balance security requirements against candidate experience impacts based on their specific hiring contexts.
Do regulations require specific liveness detection methods?
Current regulations do not mandate active versus passive liveness detection approaches. Compliance focuses on obtaining proper consent for biometric processing, implementing reasonable identity verification appropriate to role risk, maintaining required documentation, and protecting collected data adequately. Both technical approaches can satisfy regulatory requirements including FCRA when applicable, state biometric privacy laws, and GDPR when implemented within compliant workflows. Organizations should consult legal counsel regarding specific regulatory obligations in their hiring jurisdictions.
When should organizations use active liveness detection?
Active liveness detection proves most appropriate for roles with fiduciary responsibilities, access to sensitive systems, safety-sensitive duties, or positions subject to heightened regulatory scrutiny. Organizations operating in demonstrably high-fraud environments or hiring for positions where identity fraud could enable serious harm may justify active detection's additional security assurance. Role-specific risk assessment should drive technology selection rather than applying uniform approaches across all positions.
Can passive liveness detection defeat sophisticated deepfakes?
Advanced passive liveness systems incorporating depth sensing, texture analysis, and multiple biometric signals can detect many deepfake presentations. However, effectiveness varies with attack sophistication and implementation quality. Sophisticated real-time deepfakes represent high-resource attacks uncommon in typical employment fraud scenarios. Organizations facing elevated threat environments should evaluate vendor-specific detection capabilities against relevant attack vectors and conduct risk assessments specific to their operational contexts.
What cost differences exist between active and passive liveness detection?
Active liveness detection typically carries modestly higher per-transaction costs than passive methods, though pricing varies significantly by vendor, volume, and contract terms. Total cost of ownership includes integration expenses, support burden for verification-related inquiries, and costs associated with failure retry rates. Organizations should calculate comprehensive costs rather than focusing solely on per-transaction fees, as passive detection's lower failure rates and support requirements may offset per-check price differences.
Should organizations implement both active and passive liveness detection?
Hybrid approaches merit consideration for organizations with diverse role portfolios spanning different risk levels. Many vendors support configurable verification rigor, allowing selective application of active detection to high-risk positions while using passive methods for general population hiring after appropriate risk assessment. Organizations with homogeneous hiring needs may find single-method implementation operationally simpler. Technology selection should align with documented risk assessments and operational requirements.
Additional Resources
- National Institute of Standards and Technology: Face Recognition Vendor Test (FRVT) - Liveness Detection
https://www.nist.gov/programs-projects/face-recognition-vendor-test-frvt - Federal Trade Commission: Biometric Information and the FTC Act
https://www.ftc.gov/business-guidance/blog/2023/05/biometric-information-ftc-act - Illinois Attorney General: Biometric Information Privacy Act Overview
https://www.illinoisattorneygeneral.gov/rights/bipa.html - EEOC: The Americans with Disabilities Act and the Use of Software, Algorithms, and Artificial Intelligence
https://www.eeoc.gov/laws/guidance/americans-disabilities-act-and-use-software-algorithms-and-artificial-intelligence

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR professional at GCheck, specializing in background screening, fair hiring, and regulatory compliance. She holds from the Professional Background Screening Association (PBSA) and helps organizations navigate employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology, she translates policy into practice to build ethical, compliant, human-centered hiring systems that strengthen decision-making over time.