Digital identity verification uses biometrics, document authentication, and liveness detection to confirm identity during hiring and onboarding. While it addresses remote hiring challenges and fraud risks, it does not replace background checks and requires careful evaluation of state biometric privacy laws, operational necessity, and vendor claims.
Key Takeaways
- Digital identity verification confirms identity in real time but does not assess criminal history, employment records, or other background check components.
- Technologies include biometric matching, AI document authentication, liveness detection, and digital credential validation.
- State biometric privacy laws, including Illinois BIPA and Texas CUBI, impose strict consent, retention, and disclosure requirements.
- Justified use cases include remote hiring workflows, high-fraud-risk roles, and contractor onboarding where identity assurance is operationally necessary.
- Synthetic identity fraud, credential forgery, and deepfake presentation attacks are the primary fraud vectors this technology addresses.
- Vendor evaluation requires scrutiny of accuracy claims, false positive and false negative rates, data storage architecture, and auditability features.
- Implementation demands workflow integration with applicant tracking systems, consideration of candidate experience, and staff training on compliance protocols.
- This technology is not universally necessary and may introduce cost, complexity, and privacy concerns that outweigh benefits in low-risk scenarios.
What Digital Identity Verification Means in Hiring
Digital identity verification is a process that confirms an individual is who they claim to be at a specific moment, typically during hiring or onboarding. It relies on technology to validate identity documents, match biometric data, and detect fraudulent presentation attempts. This process differs fundamentally from background checks, which assess an individual's history, qualifications, and records over time. Organizations should confirm whether their identity verification vendor is subject to FCRA requirements, as some services that maintain and furnish identity verification reports for employment purposes may qualify as consumer reporting agencies.
Identity Verification vs. Background Checks
Identity verification establishes that the person applying for a role or completing onboarding is the legitimate holder of the credentials and documents they present. Background checks evaluate whether that person has a criminal record, verifiable employment history, educational credentials, or other attributes relevant to job suitability.
| Function | Identity Verification | Background Check |
| Purpose | Confirms who the individual is at the moment | Assesses what the individual has done historically |
| Data Sources | Identity documents, biometrics, real-time validation | Criminal records, employment history, education, credit |
| Timing | Pre-offer, onboarding, or ongoing access control | Post-offer, pre-employment |
| Compliance Focus | I-9, biometric privacy laws, data protection | FCRA, state Ban-the-Box laws, industry regulations |
Conflating the two creates operational confusion. An identity verification system may confirm that a passport belongs to the applicant presenting it but will not reveal whether that applicant has a history that disqualifies them from the role.
Workflow Positioning
Digital identity verification typically occurs at three stages:

- Pre-offer identity proofing may be used to screen out fraudulent applications before investing screening resources.
- Onboarding identity verification supports compliance with Form I-9 requirements, particularly in remote or distributed hiring models.
- Ongoing access control may require periodic re-verification for contractors, temporary workers, or employees accessing sensitive systems.
Problems Addressed and Not Addressed
This technology solves identity assurance problems. It confirms the person completing a Form I-9 is the authorized worker, prevents impersonation fraud during remote interviews or assessments, and detects synthetic identities constructed from fabricated or stolen information.
However, it does not solve suitability problems, such as verifying prior employment, confirming educational credentials through institutional records, or identifying criminal convictions.
"Knowing who you are hiring is just the starting point, not the full picture.” As I read through this, it made me think about how easy it is for us to think that technology can fix everything in the hiring space. While digital identity verification certainly puts us in a position of confidence, especially in a remote work world, it does not replace the work of really understanding the background and experience of a person. What matters is how we thoughtfully combine tools and human judgment to build a process that is both secure and fair
Core Technologies Explained
Understanding how digital identity verification systems operate is necessary for evaluating vendor claims and assessing whether a given solution meets operational requirements.
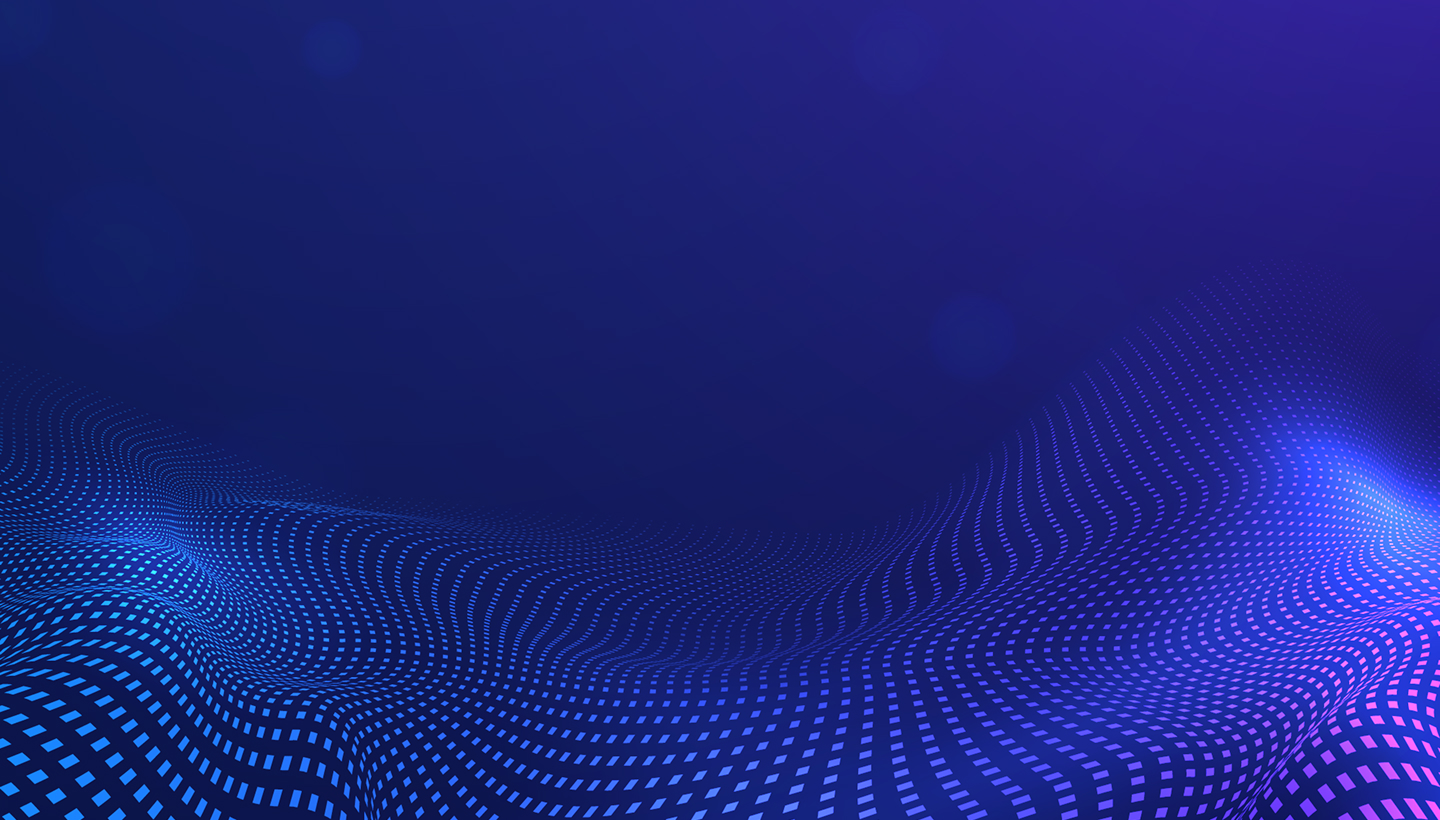
Biometric Verification
Biometric verification compares physical or behavioral characteristics to confirm identity. Common methods include the following:
- Fingerprint scanning matches ridge patterns captured during enrollment to subsequent authentication attempts.
- Facial recognition analyzes geometric relationships between facial features to create a template for matching.
- Iris scanning evaluates unique patterns in the colored portion of the eye.
Biometric systems operate on a matching threshold. Setting the threshold lower increases the likelihood of accepting legitimate users but also increases false positives. Setting it higher reduces false positives but increases false rejections. There is no setting that eliminates both risks simultaneously, and vendors who claim otherwise should be questioned.
AI-Powered Document Authentication
AI-driven document authentication analyzes identity documents such as passports, driver's licenses, and state IDs to detect alterations, forgeries, or fabricated credentials. Machine learning models are trained on legitimate documents to recognize security features, including watermarks, holograms, microprinting, and embedded chips.
Systems may flag inconsistencies in fonts, spacing, or layout that suggest tampering. They may also cross-reference barcode or MRZ data against the visual content to identify mismatches. However, sophisticated forgeries that replicate security features or use genuine blanks obtained through document theft can evade detection. No system achieves perfect accuracy, and manual review may still be necessary for flagged cases.
Liveness Detection
Liveness detection distinguishes live individuals from spoofing attempts, including photographs, videos, masks, or deepfake presentations.
- Passive liveness detection analyzes images or video without requiring user action, looking for signs of digital manipulation or presentation attacks.
- Active liveness detection requires the user to perform actions such as blinking, turning their head, or following prompts to prove physical presence.
Detection capabilities vary widely across systems. Organizations evaluating passive liveness detection should request evidence of testing against current deepfake and synthetic media techniques, as detection accuracy depends on the sophistication of the attack and the system's underlying algorithms. Active methods reduce this risk but introduce friction in the candidate experience. Organizations must balance security requirements against usability constraints.
Digital Credential Validation
Some systems validate digital credentials, including blockchain-based diplomas, professional licenses, or government-issued digital IDs. These credentials contain cryptographic signatures that allow verification without contacting the issuing institution.
Adoption of digital credentials remains uneven. Some institutions issue blockchain-based or cryptographically signed credentials, but acceptance for compliance purposes varies by jurisdiction and context. Organizations should verify whether digital credentials satisfy their specific regulatory or policy requirements and consult current guidance from relevant authorities before relying on them for employment verification.
Legal and Compliance Landscape
Digital identity verification intersects with multiple legal frameworks, and noncompliance can result in penalties, litigation, or reputational harm.
Federal Context for I-9 Compliance
Form I-9 requires employers to verify identity and work authorization for all new hires. Traditionally, this required in-person inspection of original documents. The COVID-19 pandemic prompted temporary flexibility allowing remote inspection, which has since been modified or replaced by updated guidance. Organizations must confirm current I-9 rules and determine whether remote identity verification workflows satisfy federal requirements, as regulations and acceptable methods continue to evolve. Employers should consult U.S. Citizenship and Immigration Services guidance or legal counsel before implementing remote verification processes.
E-Verify allows employers to electronically confirm work authorization by comparing I-9 information against Social Security Administration and Department of Homeland Security records. Participation is mandatory for certain employers, including federal contractors, and voluntary for others. Some digital identity verification systems integrate with E-Verify, but integration alone does not satisfy I-9 requirements if the identity verification process itself is noncompliant. Employers should confirm whether they are required to use E-Verify and ensure their verification process meets all applicable I-9 obligations.
State Biometric Privacy Laws
State biometric privacy laws impose requirements on the collection, storage, and use of biometric data, and penalties for noncompliance can be substantial.
| State | Law | Key Requirements |
| Illinois | Biometric Information Privacy Act (BIPA) | Written consent before collection; disclosure of retention schedules; private right of action with statutory damages |
| Texas | Capture or Use of Biometric Identifier (CUBI) | Consent and disclosure requirements; no private right of action |
| California | Consumer Privacy Act (CPRA) | Biometric data classified as personal information; rights to access, deletion, and opt-out |
Organizations operating in multiple states may choose to apply the most restrictive standard to simplify compliance, though this is a risk management decision rather than a legal requirement. Alternatively, organizations may apply jurisdiction-specific rules based on factors such as where the individual is located, where biometric data is collected, or where processing occurs. Legal counsel can help determine the appropriate compliance approach based on the organization's operational footprint and risk tolerance. Vendor contracts should specify who is responsible for obtaining consent, where data is stored, and how long it is retained.
Data Retention and Storage Requirements
Biometric data is considered sensitive, and some regulations require specific retention and destruction protocols. Organizations should verify whether vendor systems store raw biometric data, encrypted templates, or hash representations. On-device processing that does not transmit biometric data to external servers reduces regulatory risk but may limit functionality.
Retention periods should align with business necessity and legal requirements. Retaining biometric data longer than necessary increases liability in the event of a breach or regulatory investigation and may trigger state breach notification obligations. Organizations should establish data retention and destruction schedules that minimize risk and comply with applicable privacy laws.
International Considerations
Organizations hiring employees in the European Union must comply with General Data Protection Regulation requirements, which classify biometric data as a special category requiring explicit consent and heightened protection. Cross-border data transfers from the EU to the U.S. may require standard contractual clauses, adequacy determinations, participation in frameworks such as the EU-U.S. Data Privacy Framework, or other approved mechanisms. Organizations should consult legal counsel with expertise in international data privacy to ensure compliant data transfer practices.
When Digital Identity Verification Is Operationally Necessary
Not every organization or hiring scenario requires digital identity verification, and unnecessary implementation introduces cost, complexity, and privacy risk.
Justified Use Cases
Remote hiring workflows where in-person document inspection is impractical may justify identity verification technology. Organizations with distributed teams or locations far from central HR offices face logistical challenges in conducting compliant I-9 verification, and digital solutions may reduce administrative burden while maintaining compliance.
Additional scenarios include the following:
- High-fraud-risk roles, including positions with access to financial systems, customer data, or proprietary information, may warrant stronger identity assurance than standard processes provide.
- Contractor onboarding, particularly for short-term or project-based engagements, may require rapid identity verification without the infrastructure available for full-time employees.
Scenarios Where Traditional Methods Suffice
Small organizations with in-office hiring and onboarding processes may find traditional document inspection adequate. Low-turnover environments where hiring is infrequent may not justify the fixed costs of implementing and maintaining a digital verification system. Roles without access to sensitive systems or data may not present sufficient fraud risk to warrant additional verification layers.
Risk-Based Decision Framework
Organizations should assess identity fraud risk based on several factors:
- The sensitivity of data or systems the role accesses
- The geographic distribution of applicants and employees
- The volume and frequency of hiring
- The regulatory environment governing their industry
A structured risk assessment can determine whether identity verification is a compliance necessity, a risk mitigation measure, or an unnecessary expense.
Fraud Vectors This Technology Addresses
Understanding the specific threats digital identity verification mitigates helps organizations evaluate whether these threats are material to their operations.
Synthetic Identity Fraud
Synthetic identity fraud involves creating fictitious identities using combinations of real and fabricated information. An individual may use a valid Social Security number paired with a false name and date of birth. These identities can pass initial screening because some components are legitimate, but they do not correspond to real individuals.
Digital identity verification can detect inconsistencies between documents and databases, flag identities with limited or suspicious credit histories, and identify mismatches between biometric data and claimed identity. However, sophisticated synthetic identities constructed over time with established credit and document trails may still evade detection.
Credential Forgery
Forged or altered identity documents, including driver's licenses, passports, and diplomas, can misrepresent an individual's identity or qualifications. AI-powered document authentication systems analyze security features and detect tampering, but high-quality forgeries using genuine document blanks or advanced printing techniques may pass automated checks.
Organizations should understand that no detection system is infallible and consider whether additional manual review or institutional verification is appropriate for high-stakes roles.
Impersonation Fraud
Impersonation fraud occurs when one individual poses as another during the hiring or onboarding process. This may involve the following:
- Proxy test-taking for assessments
- Ghost employees where one person completes onboarding but another performs the work
- Identity theft where stolen credentials are used to gain employment
Biometric verification and liveness detection reduce impersonation risk by requiring the individual presenting credentials to match enrolled biometric data in real time. However, organizations must ensure enrollment processes themselves are secure and that biometric data cannot be replayed or spoofed.
Deepfake and Presentation Attacks
Advances in deepfake technology allow creation of synthetic video that convincingly impersonates real individuals. Presentation attacks may involve displaying photographs, pre-recorded video, or masks to bypass facial recognition systems.
Active liveness detection requiring real-time responses to unpredictable prompts reduces this risk, but passive systems relying solely on image analysis may be vulnerable. Organizations should verify whether vendor systems have been tested against current deepfake techniques and presentation attack methods.
Evaluating Technology Claims
Vendor marketing often emphasizes accuracy and capability without disclosing trade-offs or limitations. Informed evaluation requires understanding what claims mean and what questions to ask.
Accuracy Rates and What They Conceal
Vendors may advertise high accuracy rates without specifying whether this refers to false acceptance rate, false rejection rate, or a composite metric. Marketing claims that omit material information about accuracy trade-offs or testing conditions may be misleading.
- False acceptance rate measures how often the system incorrectly accepts an unauthorized individual.
- False rejection rate measures how often it incorrectly rejects a legitimate user.
These rates are inversely related, and improving one typically worsens the other. Organizations should request separate false acceptance and false rejection rates, ask how thresholds can be adjusted to prioritize security or usability, understand the demographic performance of the system, as some biometric technologies exhibit disparities across age, gender, or skin tone, and verify whether claims have been independently tested.
Liveness Detection Methods
Passive liveness detection is less intrusive but may be less secure. Active liveness detection is more secure but introduces friction that may degrade candidate experience.
Organizations should evaluate whether the level of security justifies the user experience impact and confirm that the system has been tested against current attack vectors, including deepfakes and 3D masks.
Data Storage and Encryption
Organizations should clarify whether biometric data is stored on-device, in vendor-controlled cloud infrastructure, or in organization-controlled systems.
| Storage Model | Privacy Risk | Functionality | Compliance Considerations |
| On-device | Low | Limited cross-device verification | Minimal data residency concerns |
| Vendor cloud | Medium to High | Full feature access | Requires strong encryption, access controls, and data residency compliance |
| Organization-controlled | Medium | Full control over security | Requires internal IT resources and security protocols |
Vendors should specify encryption standards for data at rest and in transit, access logging and audit capabilities, and data deletion processes when an individual's relationship with the organization ends.
Integration Complexity
Digital identity verification systems must integrate with existing workflows, including applicant tracking systems, human resources information systems, and onboarding platforms. Organizations should assess whether integration requires custom development or if pre-built connectors are available, how identity verification results are communicated to downstream systems, and whether the system supports single sign-on or requires separate authentication.
User experience matters. Systems that require candidates to download apps, create accounts, or complete lengthy processes may reduce application completion rates.
Auditability and Compliance Demonstration
Regulators and auditors may require documentation of identity verification processes. Organizations should confirm whether the system logs verification attempts, outcomes, and timestamps, stores evidence such as document images or biometric match scores, and provides reporting capabilities that support compliance audits.
Systems that do not retain sufficient documentation may satisfy operational needs but fail regulatory scrutiny.
Implementation Considerations
Deciding to implement digital identity verification is only the first step. Execution requires planning, resource allocation, and change management.
Workflow Integration
Identity verification must fit into existing hiring and onboarding workflows without creating bottlenecks. Organizations should map current processes to identify where verification occurs, determine whether verification will be synchronous or asynchronous, and establish escalation procedures for flagged or failed verification attempts.
Integration with applicant tracking systems should trigger verification at the appropriate stage, communicate results back to the system, and maintain a record for audit purposes. Poor integration creates manual workarounds that introduce errors and inefficiencies.
Candidate and Employee Experience
Verification processes that are confusing, time-consuming, or technically demanding increase abandonment rates and degrade the candidate experience. Organizations should test the process with representative users, provide clear instructions and support resources, and ensure accessibility for individuals with disabilities or limited technology access.
Candidates may have concerns about biometric data collection. Transparent communication about what data is collected, how it is used, who has access, and how long it is retained can reduce resistance and build trust.
Training Requirements
Human resources staff and hiring managers must understand the following:
- When and how to use the verification system
- How to interpret results and handle exceptions
- What compliance obligations apply
Training should cover consent requirements, data handling procedures, and escalation protocols for suspected fraud or system errors. Failure to train staff adequately increases the risk of noncompliance and operational errors.
Cost Structure
Digital identity verification systems may charge per verification, subscription fees, or implementation costs. Organizations should evaluate total cost of ownership, including licensing, integration, training, and ongoing support, and compare cost against the risk reduction or operational efficiency gained.
Pilot programs can help assess cost-effectiveness before committing to enterprise-wide deployment.
Common Misconceptions and Pitfalls
Misunderstanding what digital identity verification can and cannot do leads to poor decisions and unmet expectations.
AI Verification Eliminates All Identity Fraud
No technology eliminates all fraud. Sophisticated attackers adapt to detection methods, and new fraud techniques emerge continuously. Organizations should view identity verification as one layer in a multi-layered risk management strategy, not a complete solution.
This Replaces Background Checks
Identity verification confirms who someone is. Background checks confirm what someone has done. These are complementary, not interchangeable. Organizations that skip background checks in favor of identity verification alone fail to assess suitability and expose themselves to negligent hiring risk. If an employer takes adverse action based on information from an identity verification service that qualifies as a consumer reporting agency under FCRA, the employer must follow pre-adverse action and adverse action notice requirements, including providing the applicant with a copy of the report and a summary of rights.
Biometric Data Is Always Stored
Some systems process biometric data on-device and generate a one-time match score without storing the raw data. Others store encrypted templates or hash representations. Organizations should verify storage practices and ensure they align with legal and policy requirements.
It Is Only for Large Enterprises
Small and mid-sized organizations use digital identity verification for remote I-9 compliance, contractor onboarding, and fraud prevention. Scalable, per-verification pricing models make the technology accessible to organizations of various sizes.
Decision Framework: Is This Right for Your Organization?
A structured approach helps organizations determine whether digital identity verification addresses a real operational need.
Risk Assessment Checklist
Organizations should evaluate the following:
- Whether they hire remotely or have distributed teams
- Whether they have experienced identity fraud or credential forgery incidents
- Whether they operate in industries with high fraud risk or regulatory scrutiny
- Whether they onboard contractors, temporary workers, or high-turnover roles
Compliance Requirements Matrix
Organizations must determine whether they are subject to state biometric privacy laws, whether they need remote I-9 compliance capabilities, whether their industry has specific identity verification mandates, and whether they handle data subject to GDPR or other international privacy regulations.
Cost-Benefit Considerations
Costs include technology licensing, integration and implementation, training and change management, and ongoing support and maintenance. Benefits include reduced identity fraud losses, improved compliance with I-9 and biometric privacy laws, operational efficiency in remote hiring workflows, and risk mitigation for sensitive roles.
If costs exceed benefits, or if simpler solutions address the same risks, implementation may not be justified.
Pilot Program Approach
Organizations uncertain about value can implement a pilot program for a specific role category, geography, or hiring volume. Pilots should define success metrics, establish a timeline for evaluation, and gather feedback from candidates, hiring managers, and HR staff. Lessons learned inform whether to expand, modify, or abandon the initiative.
Conclusion
Digital identity verification serves a specific function in employment screening by confirming identity in real time, particularly in remote or high-fraud contexts. It does not replace background checks, and implementation requires careful evaluation of legal requirements, operational necessity, and vendor capabilities. Organizations should assess whether the technology addresses material risks and whether benefits justify costs and complexity.
Frequently Asked Questions
What is the difference between identity verification and a background check?
Identity verification confirms that an individual is who they claim to be at the time of verification, typically using biometrics or document authentication. A background check examines an individual's history, including criminal records, employment, and education. Identity verification is a prerequisite for ensuring the background check is conducted on the correct individual, but it does not assess suitability or qualifications.
Are employers required to use digital identity verification?
No federal law requires digital identity verification for employment. However, some states and industries have specific identity proofing requirements, and organizations using biometric verification must comply with state biometric privacy laws. Employers hiring remotely may find digital verification necessary to meet Form I-9 compliance obligations when in-person document inspection is not feasible.
What are state biometric privacy laws, and how do they affect identity verification?
Under state biometric privacy laws such as Illinois BIPA and Texas CUBI, employers must obtain written consent before collecting biometric data, disclose how data will be used and stored, and establish data destruction schedules. Consent and disclosure requirements vary by jurisdiction, and organizations should verify applicable state and local laws based on where employees and applicants are located.
Can digital identity verification detect synthetic identity fraud?
Digital identity verification can detect some synthetic identity fraud by flagging inconsistencies between documents and databases or identifying fabricated credentials. However, sophisticated synthetic identities built over time with established credit histories and genuine documents may evade detection. Organizations should use identity verification as one tool within a broader fraud prevention strategy.
What should I ask vendors about liveness detection?
Ask whether the system uses passive or active liveness detection, whether it has been tested against deepfake and presentation attacks, what the false acceptance and false rejection rates are, and whether it has demonstrated consistent performance across demographic groups. Request documentation of third-party testing or certifications if available.
Does digital identity verification replace Form I-9?
No. Form I-9 is a federal requirement for verifying identity and work authorization. Digital identity verification can support I-9 compliance by enabling remote document inspection, but it must be implemented in accordance with current regulations. Employers should confirm that their process satisfies both document inspection and retention requirements.
How long should biometric data be retained?
Retention periods depend on legal requirements and business necessity. Some state laws require destruction when the reason for collection no longer exists. Organizations should establish retention schedules that comply with applicable laws, minimize liability, and support operational needs. Vendor contracts should specify data retention and destruction responsibilities.
Is digital identity verification suitable for small businesses?
Small businesses with remote hiring, contractor onboarding, or fraud concerns may benefit from digital identity verification. Per-verification pricing models reduce upfront costs, and some vendors offer solutions tailored to small and mid-sized organizations. However, businesses with in-office hiring and low fraud risk may find traditional methods sufficient.
Additional Resources
- Form I-9, Employment Eligibility Verification
https://www.uscis.gov/i-9 - E-Verify Overview
https://www.e-verify.gov/ - Illinois Biometric Information Privacy Act (BIPA)
https://www.ilga.gov/legislation/ilcs/ilcs3.asp?ActID=3004 - Texas Capture or Use of Biometric Identifier Act
https://capitol.texas.gov/tlodocs/86R/billtext/html/HB00004F.htm - Federal Trade Commission: Fair Credit Reporting Act
https://www.ftc.gov/enforcement/statutes/fair-credit-reporting-act - NIST Digital Identity Guidelines
https://pages.nist.gov/800-63-3/ - California Consumer Privacy Act (CCPA) Overview
https://oag.ca.gov/privacy/ccp

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications through the Professional Background Screening Association (PBSA) and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.