Organizations placing contractors in client homes bear a duty of reasonable care in contractor selection, but the verification infrastructure most have in place was not designed for the access level those contractors actually have. The gap between what was verified and what access was granted is where negligent hiring liability lives. This article covers what the legal duty of care requires, how verification depth should map to physical access level, what a documented program includes at each tier, and where FCRA compliance obligations apply.
Key Takeaways
- Negligent hiring doctrine applies to independent contractors in many U.S. jurisdictions, though application varies. Worker classification does not automatically protect an engaging party from liability when the hirer knew or should have known the risk.
- The standard of care scales with physical access level and vulnerable population contact. A contractor doing exterior work and a contractor with unsupervised interior access require materially different verification.
- The at-hire check is a starting point, not a complete solution. Recurring in-home engagements require continuous monitoring. A single onboarding check covers the moment of hire, not the months or years of access that follow.
- If you use a consumer reporting agency to screen contractors, FCRA obligations apply regardless of worker classification. Disclosure, authorization, and adverse action requirements attach to CRA use, not employment status.
- Documentation of due diligence is as important as the check itself for liability defense. A well-documented program that ran proportionate checks stands in a substantially stronger position than one that relied on informal verification without records.
The Legal Duty of Care in Contractor Selection
The negligent hiring doctrine holds that the hirer of an independent contractor may bear liability for harm resulting from that contractor's conduct if the hirer knew, or reasonably should have known, that the contractor posed a foreseeable risk. The application of this doctrine to independent contractor engagements varies by jurisdiction. Some states have extended it to contractor relationships, while others have not. Organizations should therefore confirm the applicable standard in each jurisdiction where they place contractors with qualified legal counsel.
Courts examining negligent hiring claims frequently consider factors such as:
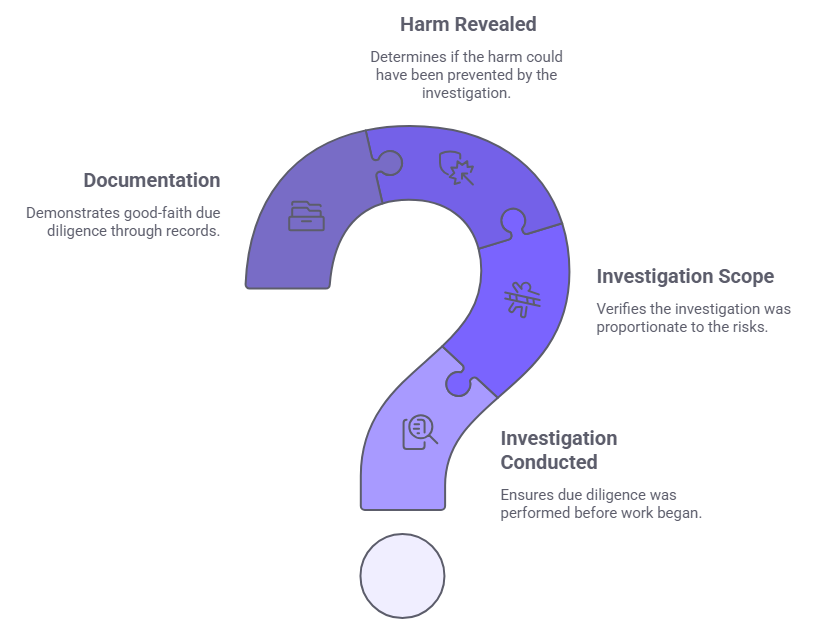
- Whether the engaging party conducted any investigation before the contractor began work.
- Whether the scope of that investigation was proportionate to the nature of access and the risk profile of the role.
- Whether the harm that resulted was of a type that a reasonably scoped check could have revealed.
- Whether the engaging party documented its selection process in a way that demonstrates good-faith due diligence.
The specific factors and their weight vary by jurisdiction. This framework is a general guide, not a universal legal standard. The standard of care is highest when contractors have unsupervised access to private residences, when they have contact with vulnerable populations, and when they hold access credentials for repeat engagements. Consequently, documentation matters independently of outcome. An engaging party that conducted proportionate verification and kept records stands in a substantially different legal position than one that conducted no verification at all.
Why a Single At-Hire Check Is Not Enough for Recurring Contractor Programs
Most contractor screening programs are designed around the hiring event. A check runs before engagement begins, a result comes back, and if the result is acceptable, the contractor is approved. For a one-time engagement, this model is structurally adequate. For recurring in-home contractor programs, however, it is not. Three structural gaps emerge when a single at-hire check is applied to contractors who return weekly, monthly, or seasonally over extended periods.
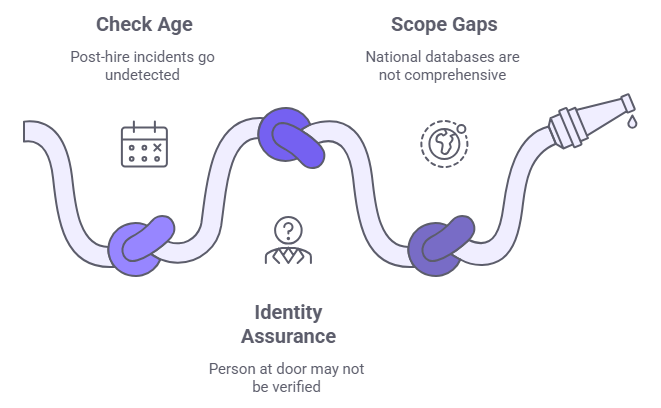
- Check age and post-hire incidents. Arrests, convictions, protective orders, and sex offender registry additions that occur after the initial check never surface without re-screening or continuous monitoring. As a result, a contractor who cleared an onboarding check two years ago and has since accumulated a criminal record looks identical, under an onboarding-only program, to a contractor with a clean record today.
- Identity assurance at point of service. An at-hire check confirms that a named individual does not have a disqualifying record. It does not confirm that the person arriving at the client's door is that individual. Credential sharing and account transfer, where a verified contractor allows a different person to perform work under their credentials, exploits this gap directly.
- Scope gaps in national criminal database searches. National criminal databases pull records from participating jurisdictions but are not comprehensive. County-level records are inconsistently included, and reporting lags mean that recent arrests or convictions may not appear in a national database search even when a county-level check would reveal them.
These gaps are structural, not operational. They cannot be resolved by running the same check more carefully. Instead, they require a different program structure, one that includes continuous monitoring, point-of-service identity confirmation, and multi-jurisdiction criminal coverage for higher-access tiers.
Access-Based Verification: Why Role Title Is the Wrong Variable
Most contractor screening programs tier verification by job title or trade category. This approach produces an inaccurate risk assessment and a less defensible program. The actual risk variable is not the trade. It is the physical access the engagement grants.
A licensed electrician doing exterior work at a vacant property presents a materially different access profile than the same electrician completing a multi-day interior renovation in an occupied residence with children present. The credential is the same, but the access level is not. Tiering by access level concentrates verification investment where risk is highest and produces a framework that holds up under legal scrutiny. The framework in the next section organizes verification requirements around three access tiers defined by physical access level and population contact, rather than job title or license category.
A Tiered Verification Framework for Home Services Operators: Matching Background Checks to Access Level
The table below maps verification requirements to three access tiers. Organizations should assign each contractor role to the appropriate tier before screening begins and run the corresponding verification stack through a FCRA-compliant consumer reporting agency where applicable.
| Verification Component | Tier 1: Exterior or Supervised | Tier 2: Interior, Client Present | Tier 3: Unsupervised or Vulnerable Population |
| Government-issued ID verification | Required | Required | Required |
| SSN trace and address history | Required | Required | Required |
| National criminal database check | Required | Required | Required |
| County and state criminal records (multi-jurisdiction) | Not required | Required | Required |
| Federal criminal search | Not required | Required | Required |
| Sex offender registry check | Required | Required | Required |
| Document authentication | Not required | Required | Required |
| Biometric identity matching | Not required | Not required | Required |
| Professional license verification | Where trade requires | Trade-specific | Required |
| Continuous criminal monitoring | Not required | Recommended for recurring | Required |
| Point-of-service identity confirmation | Not required | Photo ID confirmation | Biometric confirmation each visit |
Tier assignment should be reviewed whenever a contractor's scope or access level changes, not only at initial engagement.
Tier 1: Exterior or Supervised Access
This tier applies to contractors whose work occurs outside the residence or in the presence of the client or a designated supervisor throughout the engagement. Examples include landscaping, exterior painting, driveway and roof work, supervised delivery, and metered utility work at an exterior panel. The verification stack at this level establishes identity and screens for disqualifying criminal history at the national level. The supervision layer or exterior-only access reduces the risk profile sufficiently that county-level records and biometric matching are not required.
Tier 2: Interior Access With Client Present
Tier 2 applies to contractors who enter the residence and perform work inside, but where a client or responsible adult stays on the premises throughout the engagement. Examples include appliance repair, HVAC service, plumbing, furniture assembly, and general cleaning with the client present. At this tier, national database coverage alone is not enough. County-level records provide more detail and more current data than national databases. Document authentication confirms that the identity presented at onboarding matches a genuine, unaltered document. Federal criminal search adds coverage for offenses prosecuted at the federal level that may not appear in state or county records.
Tier 3: Unsupervised Interior Access or Vulnerable Population Contact
Tier 3 applies to contractors who enter the residence without the client present, hold access credentials for repeat use, or have direct unsupervised contact with vulnerable household members. Examples include cleaning when the client is away, in-home elder or disability care, childcare, private tutoring, and long-term renovation with key or code access. At this tier, full identity proofing including biometric matching is required. Continuous criminal monitoring is also required for all recurring engagements. Point-of-service biometric confirmation for each visit closes the identity assurance gap at the point of highest risk. Organizations implementing point-of-service biometric confirmation should know that several states, including Illinois, Texas, and Washington, impose consent, storage, and destruction obligations under biometric privacy statutes. Legal review of biometric data practices is therefore recommended before implementation.
FCRA Compliance for Contractor Screening Programs
The most common FCRA compliance gap in contractor screening programs is the assumption that FCRA applies only to employee background checks. In practice, if an organization uses a consumer reporting agency to conduct background checks on independent contractors, FCRA obligations apply regardless of how the worker is classified. The moment a CRA is involved, the full FCRA framework applies.
Disclosure and Authorization
Disclosure and authorization must occur before any check is ordered through a CRA. Specifically, FCRA requires a standalone written disclosure and written authorization from the contractor before the engaging party contacts the CRA. The disclosure document must consist solely of the disclosure. The written authorization may appear on the same document as the disclosure, but no other content may be present. Including additional terms, acknowledgments, or agreements on the same form violates the standalone requirement regardless of where in the document the disclosure language appears.
Pre-Adverse and Adverse Action Process
The two-step adverse action process applies when background check results obtained through a CRA will inform a decision to deny engagement or restrict access. Before any adverse decision is final, the engaging party must provide the contractor with a pre-adverse action notice. That notice must include a copy of the consumer report and the Summary of Rights Under the FCRA, and must inform the contractor of their right to dispute the accuracy or completeness of the report. The engaging party must then allow a waiting period of generally at least five business days per CFPB and FTC guidance. If proceeding after that period, the final adverse action notice must identify the consumer reporting agency, state that the CRA did not make the adverse action decision and cannot provide specific reasons for it, and inform the contractor of their right to obtain a free copy of the report within 60 days and to dispute its accuracy or completeness.
State Law Supplements
State law adds requirements in several key jurisdictions that exceed the federal FCRA floor. For example, California's ICRAA imposes a seven-year lookback limit regardless of salary threshold, which differs materially from the federal rule. Similarly, New York's Fair Chance Act requires a specific individualized assessment process and written notice before adverse action based on criminal history. In addition, Illinois's Job Opportunities for Qualified Applicants Act imposes ban-the-box timing requirements for private employers. These examples are illustrative, not exhaustive. Organizations operating in any of these states should therefore obtain state-specific legal review before implementing a contractor screening program.
Building a Documented Contractor Screening Program
A defensible contractor screening program operates across four stages. Each stage addresses a distinct component of the verification gap that single-check, onboarding-only programs leave open.
Pre-Engagement
Before any contractor begins work, the engaging party should complete the following steps in order.
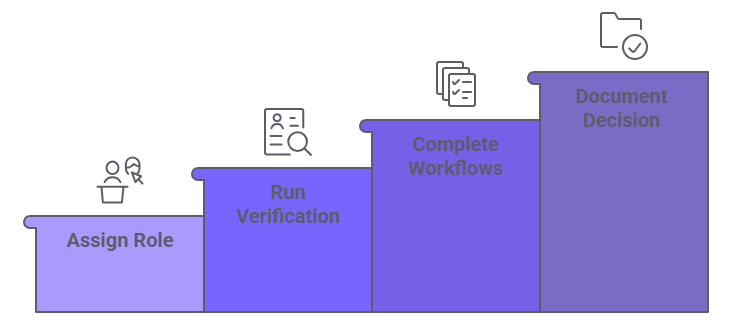
- Assign the contractor's role to the appropriate access tier.
- Run the verification stack for that tier through a FCRA-compliant consumer reporting agency.
- Complete the disclosure, authorization, and adverse action workflows for every contractor screened through a CRA.
- Document both the results and the basis for any access decision.
The tier assignment and verification scope should go into the engagement file as a formal record, not treated as an informal step.
At First Service
Verification conducted before engagement does not confirm that the person arriving at the first appointment is the person whose credentials were checked. Accordingly, Tier 2 engagements require photo ID confirmation at the time of first service, matched against the identity verified at onboarding. Tier 3 engagements require biometric confirmation at each visit for contractors holding key or code access. This step directly addresses the credential sharing gap that onboarding-only programs cannot close.
Ongoing
All Tier 3 contractors and Tier 2 contractors with recurring engagements should be enrolled in continuous criminal monitoring. Organizations not using continuous monitoring should set an annual re-screen cadence for all active contractors and update tier assignments when contractor scope changes. Furthermore, when conducting re-screens or enrolling contractors in continuous monitoring through a CRA, the engaging party must obtain a fresh standalone disclosure and written authorization. FCRA requires a new disclosure and authorization for each consumer report ordered through a CRA. The original onboarding authorization does not extend to later checks.
Documentation
The program must retain records of what was checked, when the check ran, what the results were, and what access or engagement decision followed. Documentation serves three independent functions. First, it demonstrates due diligence to a court if a negligent hiring claim arises. Second, it shows program integrity to a client requiring background check certification under a contract. Third, it supports FCRA compliance by preserving the record of disclosure, authorization, adverse action notices, and waiting period compliance that a contractor may request or that regulators may review. Retain adverse action documentation, including delivery confirmation and waiting period records, as part of the engagement file for each contractor screened through a CRA.
Conclusion
The gap between verification conducted at hire and access granted over time is where home services contractor liability exposure lives. A tiered framework organized around physical access level, rather than job title or trade category, produces a more accurate risk assessment and a more defensible program. Continuous monitoring, point-of-service identity confirmation, and documented adverse action workflows close the structural gaps that single-check, onboarding-only programs leave open. FCRA compliance obligations apply to contractor screening conducted through a consumer reporting agency regardless of worker classification. Organizations building or auditing a contractor screening program should confirm their specific obligations, including state-specific supplements, with qualified legal counsel.
Frequently Asked Questions
Can I be held liable if a contractor I hired causes harm in a client's home?
In many jurisdictions, yes. The negligent hiring doctrine holds that an engaging party may bear liability if harm results from a contractor's conduct and the engaging party knew or reasonably should have known the contractor posed a foreseeable risk. Application of this doctrine to independent contractors varies by jurisdiction. Consult qualified legal counsel for any specific liability assessment.
Do FCRA requirements apply to background checks on independent contractors?
Yes, if the check is ordered through a consumer reporting agency. FCRA's disclosure, authorization, and adverse action obligations apply regardless of whether the screened individual is classified as an employee or an independent contractor. The triggering condition is CRA use, not worker classification. Confirm your specific obligations with qualified legal counsel.
How often should home services contractors be re-screened?
Contractors with unsupervised interior access or vulnerable population contact should be enrolled in continuous criminal monitoring for the duration of their engagement. Organizations not using continuous monitoring should re-screen active contractors at least annually. Each re-screen conducted through a CRA requires a fresh disclosure and authorization from the contractor.
What is the minimum background check for a contractor entering a home?
At minimum, any contractor entering a residence should clear an identity verification with SSN trace, a national criminal database check, and a sex offender registry check. For interior access with the client present, add county-level criminal records and document authentication. For unsupervised interior access, add biometric identity matching, federal criminal search, continuous monitoring, and point-of-service confirmation.
What is negligent hiring for independent contractors?
Negligent hiring is a legal doctrine holding that an engaging party may bear liability for harm caused by a contractor when the engaging party failed to conduct verification proportionate to the foreseeable risk. Its application to independent contractors varies by jurisdiction. Worker classification does not automatically eliminate this exposure. The standard of care scales with access level and the vulnerability of those the contractor contacts.
Additional Resources
- FTC: Using Consumer Reports for Employment Purposes
https://www.ftc.gov/business-guidance/resources/using-consumer-reports-employment-purposes - CFPB: A Summary of Your Rights Under the Fair Credit Reporting Act
https://www.consumerfinance.gov/consumer-tools/credit-reports-and-scores/consumer-reporting-companies/fcra-summary-of-rights/ - EEOC: Background Checks: What Employers Need to Know
https://www.eeoc.gov/laws/guidance/background-checks-what-employers-need-know - 15 U.S.C. Section 1681: Fair Credit Reporting Act Full Text
https://www.govinfo.gov/content/pkg/USCODE-2022-title15/pdf/USCODE-2022-title15-chap41-subchapIII.pdf - EEOC: Employment Practices Guidance and Resources
https://www.eeoc.gov/laws/guidance - U.S. Department of Labor: Independent Contractor Classification
https://www.dol.gov/agencies/whd/flsa/misclassification

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR professional at GCheck, specializing in background screening, fair hiring, and regulatory compliance. She holds from the Professional Background Screening Association (PBSA) and helps organizations navigate employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology, she translates policy into practice to build ethical, compliant, human-centered hiring systems that strengthen decision-making over time.