Biometric liveness detection verifies that a live person is physically present during digital identity checkpoints. It distinguishes real humans from photographs, videos, masks, or deepfakes. This fraud-prevention control addresses remote hiring impersonation risks. However, it requires careful implementation to balance security effectiveness with candidate experience, technical accuracy, and biometric privacy law compliance.
Key Takeaways
- Liveness detection confirms the physical presence of a live person but does not identify who that person is. Consequently, it functions as one component within broader identity verification workflows rather than a standalone authentication solution.
- Active liveness methods require user actions like blinking or head movements. These offer stronger security but create candidate friction. In contrast, passive methods analyze video streams automatically with less disruption but potentially lower spoof resistance.
- State biometric privacy laws in Illinois, Texas, Washington, California, Arkansas, and New York impose consent requirements, retention limits, and use restrictions. Therefore, HR teams must satisfy these before deploying any liveness detection technology in hiring processes.
- False rejection rates create operational challenges when legitimate candidates fail liveness checks due to lighting conditions or device limitations. Subsequently, these include candidate complaints, hiring delays, and potential discrimination concerns if performance varies across different groups.
- Liveness detection addresses specific attack scenarios including impersonation services, proxy test-takers for skills assessments, and organized credential fraud. However, it does not prevent resume fabrication or employment history lies.
- Proportionate implementation requires risk-based deployment focused on high-trust positions, regulated industries, or contractual identity assurance requirements. As a result, universal application across all hiring scenarios is unnecessary.
- Vendor evaluation should prioritize independent certification through presentation attack detection testing. Additionally, it should emphasize compliance automation for biometric consent workflows, published accuracy metrics, and accommodation processes for candidates unable to complete biometric checks.
- Integration within hiring workflows typically occurs at specific checkpoints such as skills assessment verification, final-round interview authentication, or remote onboarding. In contrast, initial application stages rarely require this level of scrutiny.
Understanding Liveness Detection in Identity Verification
This technology has emerged as a targeted control within remote hiring workflows. Specifically, it verifies that a live human being is physically present during digital interactions. As organizations expand distributed hiring and remote work arrangements, confirming candidate presence during assessments, interviews, and onboarding has become operationally significant. Unlike comprehensive identity verification systems that combine multiple data sources and validation methods, liveness detection serves a specific function. Essentially, it distinguishes between real, present individuals and presentation attacks using photographs, pre-recorded videos, masks, or synthetic media.
The technology addresses a particular vulnerability in remote processes where physical presence cannot be assumed. Traditional in-person hiring naturally included implicit liveness verification. For example, candidates appeared in offices, interacted with interviewers face-to-face, and completed assessments under direct observation. In contrast, remote workflows eliminate these inherent controls. Consequently, this creates opportunities for impersonation fraud where one individual completes hiring steps on behalf of another.
Distinguishing liveness detection from related biometric functions is essential for HR teams:
| Function | Purpose | What It Does |
| Liveness Detection | Confirms physical presence | Verifies a live person is present, not a photo/video/mask |
| Recognition | Identifies individuals | Compares biometric samples against enrolled templates |
| Verification | Authenticates claimed identity | Confirms biometric correspondence to specific enrolled identity |
This sequential relationship matters for HR teams evaluating vendor solutions. Technologies marketed as comprehensive biometric identity systems may or may not include robust liveness capabilities.
How Liveness Detection Technology Works
Challenge-Response and Passive Analysis Methods
Systems evaluate various signals that prove difficult for attackers to replicate convincingly. The specific mechanisms vary between implementation approaches. Nevertheless, most methods assess involuntary physiological responses, three-dimensional physical properties, or behavioral patterns that differentiate living subjects from reproductions.
- Challenge-response methods present users with random instructions requiring immediate physical response. For instance, these include blinking, smiling, turning the head in specific directions, or speaking prompted phrases. Subsequently, the system evaluates whether responses occur with timing, coordination, and naturalness consistent with live human behavior. Attackers using static photographs cannot produce these responses. Meanwhile, pre-recorded videos typically fail due to the randomized nature of challenges.
- Passive analysis methods evaluate video streams without requiring explicit user actions. Instead, they examine micro-movements, texture characteristics, and physiological patterns that occur naturally during normal behavior. For instance, these systems may analyze subtle facial muscle movements, eye micro-saccades, or blood flow patterns visible through skin texture changes. Furthermore, advanced implementations use depth sensing through structured light projection or time-of-flight sensors. These verify three-dimensional physical structure rather than flat image presentation.
Multimodal Approaches and Technical Performance
Combined detection signals increase overall effectiveness significantly. For example, a system might simultaneously evaluate passive texture analysis, challenge-response timing, and depth information. This requires attackers to defeat several independent detection mechanisms. Notably, this defense-in-depth strategy reflects recognition that no single detection method proves perfect. Sophisticated attacks may circumvent individual controls but face exponentially higher complexity defeating multiple simultaneous checks.
Attack Scenarios in Remote Hiring Contexts
Several specific fraud scenarios occur within remote hiring and assessment processes. Unlike generic security contexts such as device unlocking or facility access, hiring-related impersonation fraud involves distinct motivations. Moreover, it involves specific attacker capabilities and organizational consequences that shape appropriate countermeasures.
Common fraud scenarios include:
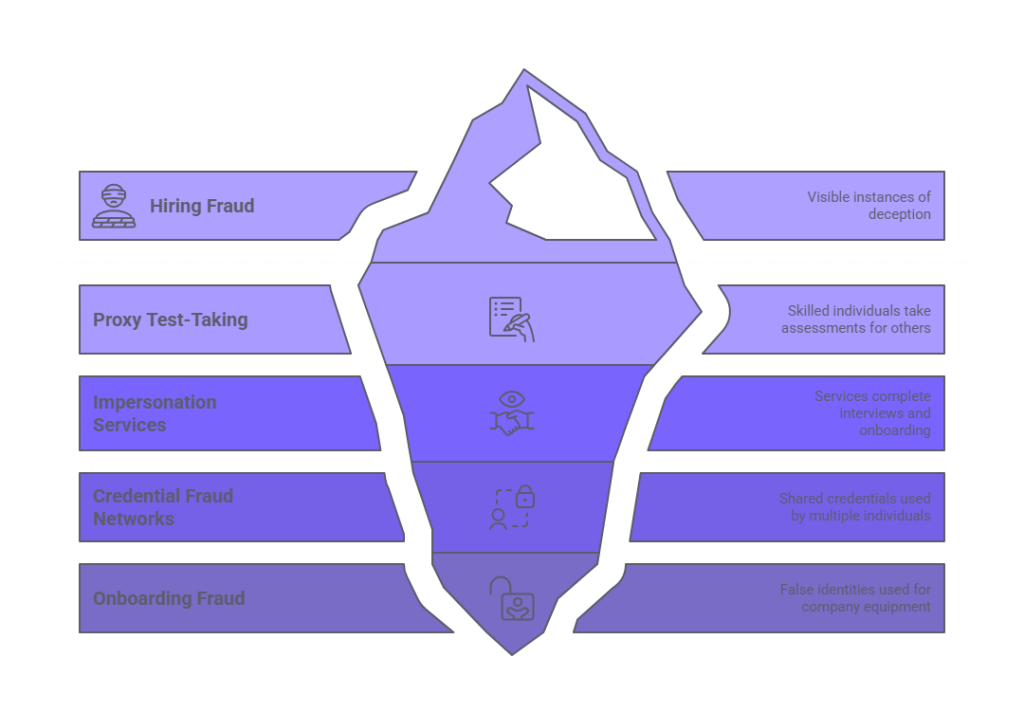
- Proxy test-taking: Candidates hire technically skilled individuals to complete online skills assessments or certification exams. This occurs particularly for specialized technical roles where assessment performance significantly influences hiring decisions.
- Professional impersonation services: These services may operate despite legal prohibitions against identity fraud. They offer to complete job interviews or onboarding processes on behalf of paying clients. While such services facilitate fraud potentially subject to criminal prosecution under identity theft, wire fraud, or conspiracy statutes, enforcement remains inconsistent. Nevertheless, candidates using these services face offer withdrawal, termination, and potential criminal liability if discovered.
- Organized credential fraud networks: Multiple individuals share single legitimate credentials in healthcare, finance, or regulated industries. Different persons complete various hiring checkpoints while claiming the same identity.
- Remote employee onboarding fraud: Individuals complete onboarding procedures using false identities. They obtain company equipment or access credentials, then disappear without performing actual work.
The sophistication required for successful attacks varies considerably. Simple photograph or video presentation may suffice against weak detection systems. However, defeating robust liveness controls requires specialized equipment, technical know-how, or physical proxies. Understanding the capability levels that specific implementations resist helps organizations match security controls to actual threat environments. As a result, this prevents over-engineering protections against theoretical attacks unlikely in hiring contexts.
Active Versus Passive Detection Approaches
| Detection Type | How It Works | Security Level | Candidate Friction | Best For |
| Active | Requires prompted actions (blink, turn head, speak phrase) | Higher—defeats pre-recorded attacks | Higher—requires privacy, compatible environment | High-stakes roles, regulated positions, final-stage verification |
| Passive | Analyzes video streams without user action | Moderate—may miss sophisticated attacks | Lower—seamless, transparent experience | Volume hiring, early-stage checks, candidate experience priority |
| Hybrid | Passive default with active escalation when anomalies detected | High—balances both approaches | Variable—friction only when needed | Balanced approach for diverse role types |
Active Detection Security and Experience Tradeoffs
Prompted actions in response to system requests form the basis of this approach. The security advantage lies in real-time verification that the subject can respond to unpredictable requests. This significantly increases attack complexity compared to static presentation. While this approach defeats simple pre-recorded videos, sophisticated real-time deepfake systems or physical proxies responding to prompts may still pose challenges. Therefore, organizations should evaluate vendor security testing methods and understand the specific attack types that challenge-response implementations reliably detect.
Candidate experience implications of active methods require careful consideration. Users must have sufficient privacy and environment control to perform requested actions without embarrassment or practical obstacles. Additionally, technical failure modes for active detection often involve lighting conditions, camera quality, or environmental factors. These prevent accurate assessment of whether responses occurred correctly.
Passive Detection Benefits and Limitations
Normal behavior analysis without requiring specific prompted actions characterizes this method. It typically evaluates video streams for characteristics indicating live presence. Users simply position themselves within camera view and proceed with their intended activity. The system operates transparently, analyzing micro-movements, texture properties, or depth information without interrupting user workflow. Consequently, the candidate experience benefits include reduced friction, faster completion, and elimination of potentially awkward prompted actions.
Security tradeoffs accompany the user experience benefits of passive detection. Without active challenge-response verification, sophisticated attacks using high-quality reproductions or real-time manipulation face fewer detection hurdles. Therefore, organizations must evaluate whether passive detection capabilities sufficiently resist attacks relevant to their threat environment.
Biometric Privacy Law Compliance Requirements
State-level privacy laws impose specific requirements for collection, use, storage, and disclosure of biometric identifiers and information. Non-compliance creates significant legal exposure including statutory penalties, class action litigation risk, and regulatory enforcement actions.
State-by-State Requirements
| State | Consent Required | Written Notice | Retention Policy | Private Right of Action | Key Distinctions |
| Illinois (BIPA) | Yes—written | Yes—purpose and duration | Yes—published schedule | Yes—individuals can sue | Most stringent; significant litigation exposure |
| Texas | Yes | Yes | Yes | No—AG enforcement only | Similar structure, limited enforcement mechanism |
| Washington | Yes | Yes | Yes | No—AG enforcement only | Similar to Texas model |
| California (CPRA) | Heightened disclosure | Yes | Yes | Limited—AG primary enforcement | Treats biometric info as sensitive personal information |
| Arkansas | Yes | Yes | Yes | No—AG enforcement only | Act 1933 (2023) follows Texas model |
| New York | Varies by locality | Yes | Yes | No—AG enforcement | NYC Local Law 144 regulates employment AI |
Illinois, Texas, Washington, California, Arkansas, and New York have enacted or are enforcing biometric privacy regulations affecting employment screening. Illinois BIPA, the most stringent framework, requires explicit written consent. It also provides private right of action and imposes strict retention and disclosure limits. In contrast, Texas and Washington require consent but limit enforcement to state attorneys general. California's CPRA treats biometric information as sensitive personal information requiring heightened disclosures. Organizations must assess requirements in all jurisdictions where candidates reside.
Critical Compliance Requirements

Consent timing and specificity: Authorization must occur before any biometric data collection. Liveness detection cannot proceed until candidates affirmatively opt in after receiving required notices. Generic privacy policies or broad consent forms typically fail to satisfy statutory requirements. Instead, consent language must clearly identify what biometric information will be collected, specific purposes, and retention duration.
Data retention and destruction: Written policies governing biometric data lifecycle must be established and published. Destruction is required when the initial purpose is satisfied or within a defined timeframe.
Third-party vendor management: Biometric data flows to and is processed by the vendor when organizations use vendor-provided liveness detection services. State biometric privacy laws distinguish between prohibited disclosure to third parties and permissible processing by service providers. Organizations must ensure vendor agreements specify the vendor's role as service provider. They must also prohibit independent use or disclosure of biometric data, establish data protection obligations, define retention and destruction responsibilities, and address regulatory compliance. Additionally, candidate consent documents should disclose vendor involvement in processing biometric information.
Data Security and Breach Notification
Appropriate security safeguards protecting biometric data against unauthorized access, disclosure, or breach must be implemented. Most states require notification to affected individuals and regulatory authorities when breaches involve biometric information. Vendor agreements should specify security standards, breach notification timing, and incident response responsibilities. Furthermore, organizations should incorporate biometric data into existing incident response plans and understand notification obligations under applicable state laws.
Additional states continue evaluating biometric privacy legislation, suggesting expanding compliance obligations. Organizations should monitor regulatory developments in jurisdictions where they recruit or hire candidates.
Accuracy, Failure Modes, and Operational Implications
False Rejection and Acceptance Rates
Technical performance characteristics directly affect operational outcomes in hiring workflows. Understanding failure modes, accuracy metrics, and demographic performance variations enables HR teams to anticipate challenges. It also helps plan appropriate accommodation processes and assess whether specific implementations meet reliability requirements.
- False rejection rates measure how frequently legitimate candidates fail liveness verification despite being real people genuinely attempting to complete checks. These false negatives create immediate operational friction. Candidates receive error messages, must retry verification, or escalate to alternative authentication methods. High false rejection rates generate candidate complaints. They also create perceptions of technical incompetence and potentially cause qualified candidates to abandon hiring processes.
- False acceptance rates measure how frequently presentation attacks successfully defeat liveness detection, allowing fraudulent attempts to pass verification. While false acceptances represent security failures rather than operational disruptions, they directly undermine the technology's core value proposition. Organizations must understand the sophistication of attacks that specific implementations reliably detect versus presentations that may evade detection.
Demographic Performance and Discrimination Concerns
Monitoring and mitigation become necessary when performance variation occurs. If liveness detection generates substantially different false rejection rates across demographic groups defined by protected characteristics, potential disparate impact concerns arise. These groups include race, sex, age, and disability. When these differences adversely affect employment opportunities, Title VII and similar laws may apply. Therefore, organizations should require vendors to provide disaggregated performance data. They should also establish monitoring processes detecting significant disparities in operational deployment. Finally, they should document that any observed performance differences do not create barriers to employment for protected groups.
Environmental Dependencies and Accommodation Requirements
Device and environment constraints limit where and how liveness detection can function reliably. Systems requiring high-quality cameras, specific lighting conditions, or stable high-bandwidth connections may prove impractical for candidates completing assessments in varied settings. Organizations must determine whether candidate populations have reliable access to compatible devices and suitable environments.
Advance planning for candidates unable to complete biometric verification satisfies Americans with Disabilities Act obligations. Disabilities affecting vision, motor control, or facial expressions may prevent completion of liveness checks, requiring alternative verification methods providing equivalent security. Technical failures or privacy objections also necessitate exception handling processes. Consequently, organizations should document accommodation procedures, train hiring staff on implementation, and ensure alternative verification methods do not impose undue burden on candidates requiring accommodation.
Integration Within Hiring and Onboarding Workflows
A single checkpoint within comprehensive hiring workflows characterizes liveness detection rather than a standalone identity solution. Determining appropriate integration points requires understanding how liveness verification complements other screening components. It also requires knowing where in the hiring sequence identity assurance becomes operationally necessary.
Recommended Integration Points
| Workflow Stage | Appropriateness | Rationale | Considerations |
| Pre-application / Initial screening | Low | Unnecessary friction; limited identity assurance value | May deter qualified applicants before mutual interest established |
| Skills assessment administration | High | Protects integrity of high-stakes evaluation | Prevents proxy test-taking; proportionate to assessment importance |
| Final-round interviews | Moderate | Appropriate for senior/sensitive roles | Balance security value against potential perception of distrust |
| Post-offer onboarding | High | Peak exposure to identity fraud targeting benefits | Occurs before granting system access or provisioning equipment |
Early hiring phases rarely justify liveness detection deployment. Pre-application or initial screening stages prioritize broad candidate attraction and initial qualification assessment where identity assurance provides limited value. Requiring biometric verification before candidates have invested significant effort or organizations have expressed genuine interest creates unnecessary friction.
In contrast, skills assessment administration represents a logical integration point when test results significantly influence hiring decisions. Organizations using technical assessments, cognitive ability testing, or certification exams as screening mechanisms face material risk from proxy test-taking fraud.
Coordination With Complementary Verification Methods
Sequential relationships between liveness detection and complementary verification methods require coordination. Physical presence confirmation occurs through liveness detection. However, it does not authenticate identity unless combined with identity document verification, biographical data validation, or comparison to enrolled biometric templates. Therefore, organizations must design workflows where liveness verification occurs in conjunction with identity-establishing processes.
Third-party vendor assessment becomes necessary for organizations using vendor-provided liveness detection services. Specifically, they should determine whether the service constitutes a consumer report under the Fair Credit Reporting Act. If the vendor collects information on candidates and furnishes reports to employers for employment purposes, FCRA requirements may apply. These include providing clear disclosure, obtaining written authorization before collection, and following adverse action procedures if liveness verification failure contributes to employment decisions. Consult legal counsel to determine FCRA applicability for specific vendor implementations.
Proportionate Deployment Based on Risk Profile
Cost, complexity, and candidate friction do not justify biometric liveness detection in all hiring scenarios. Organizations benefit from risk-based implementation strategies that deploy controls proportionally to actual threats, role sensitivity, and regulatory requirements. As a result, this avoids pursuing universal adoption across all hiring activities.
High-Priority Deployment Scenarios
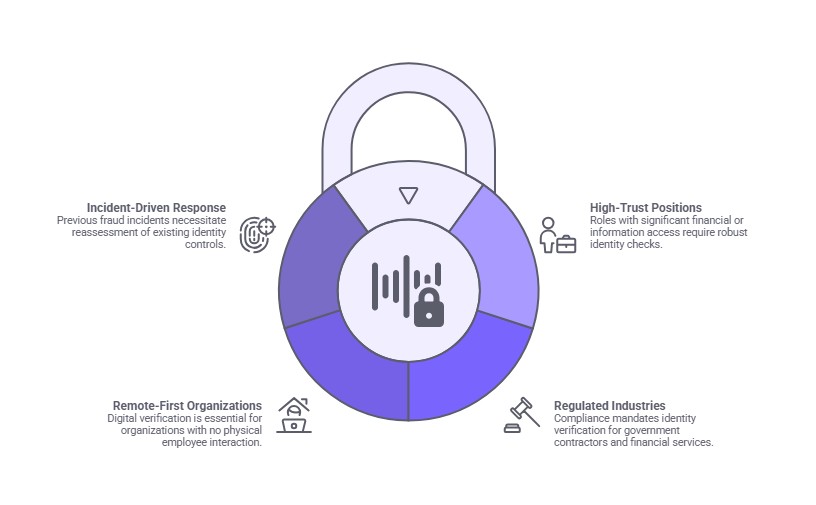
- High-trust positions: Financial authority, access to sensitive information, or fiduciary responsibilities characterize these roles. They carry elevated consequences from identity fraud.
- Regulated industries: Compliance requirements or contractual obligations may mandate identity verification standards for government contractors, healthcare organizations, or financial services firms.
- Remote-first organizations: Identity assurance relies entirely on digital verification methods when organizations never meet employees physically.
- Incident-driven response: Previous experience with hiring fraud or discovered post-hire identity discrepancies should prompt reassessment of existing controls. This determines whether they adequately address demonstrated vulnerabilities.
Lower-Priority Scenarios
- Volume hiring for entry-level positions: Close supervision, limited autonomy, and minimal sensitive access characterize these roles. Biometric liveness detection is rarely warranted.
- Office-based roles with in-person touchpoints: Physical presence during onboarding provides implicit identity verification.
- Low-risk jurisdictions: Strong identity infrastructure and limited fraud history may require less intensive verification in certain hiring contexts.
Decision Framework
Implementation costs versus potential consequences should be weighed carefully. Costs include vendor fees, technical integration effort, candidate experience impact affecting application completion rates, support resource requirements, and ongoing compliance management. On the other hand, consequences encompass direct fraud losses, regulatory penalties, reputational damage, and operational disruption from hiring imposters.
Evaluating Vendors and Implementation Options
Standalone biometric providers, applicant tracking system integrations, background check service add-ons, and identity verification platforms offering liveness as one component comprise the market. HR teams evaluating options require frameworks distinguishing marketing claims from substantive capabilities. They also need to identify implementations that satisfy operational, compliance, and technical requirements.
Independent Certification and Compliance Capabilities
Credible validation of security effectiveness against specific attack types comes through independent certification. Organizations such as iBeta Quality Assurance conduct standardized testing evaluating liveness detection performance at defined levels. Level 1 addresses basic attacks, while Level 2 addresses advanced attacks. Organizations should verify vendors hold current certifications at levels appropriate to their threat environment. Additionally, they should understand that testing occurs under controlled conditions. They should also recognize that PAD certification addresses security effectiveness but not legal compliance with biometric privacy laws or FCRA requirements.
Operational feasibility in regulated environments depends directly on compliance automation capabilities. Vendors should provide tools automating biometric privacy law consent workflows, systems maintaining required documentation, features facilitating data retention policy enforcement, and capabilities supporting data destruction obligations.
Accuracy Metrics and Accommodation Processes
Clear methodology in published accuracy metrics enables informed assessment. Vendors should disclose false acceptance rates, false rejection rates, and demographic performance data. Testing methods should specify conditions under which performance was measured. Independent third-party testing provides greater credibility than vendor self-assessment.
Operational resilience when standard verification fails depends on accommodation and exception handling. Vendors should document procedures for candidates unable to complete biometric checks due to technical limitations, accessibility needs, or legitimate privacy objections.
Integration Architecture and User Experience Testing
Deployment complexity varies based on integration architecture. Cloud-based API services offering simple integration minimize technical lift. In contrast, implementations requiring extensive custom development create higher barriers to adoption. On-premises infrastructure increases ongoing support costs.
Practical feasibility insights come from user experience testing with representative candidate populations. Before full deployment, organizations should pilot implementations with diverse candidate groups. They should gather feedback on clarity of instructions, technical difficulties encountered, and overall experience.
Conclusion
Targeted fraud prevention characterizes biometric liveness detection as it addresses specific impersonation risks in remote hiring workflows. Effective implementation requires understanding the technology's specific function within broader identity verification frameworks. It also requires navigating biometric privacy compliance requirements, balancing security effectiveness against candidate experience, and deploying controls proportionally to actual risk profiles. Organizations that approach liveness detection as one component of comprehensive identity assurance position themselves to make informed decisions aligned with operational needs and legal obligations.
Frequently Asked Questions
What is the difference between liveness detection and facial recognition in hiring contexts?
Physical presence verification during a biometric capture characterizes liveness detection. It prevents presentation attacks using photographs, videos, or masks. Facial recognition identifies individuals by comparing biometric samples to stored templates, determining whose face appears in an image. Hiring workflows may use both technologies sequentially with liveness detection confirming real presence before facial recognition authenticates identity. However, they serve distinct functions within identity verification processes.
Do all states require consent before collecting biometric data for hiring purposes?
Illinois, Texas, Washington, California, Arkansas, and New York have enacted or are enforcing biometric privacy regulations requiring consent, disclosures, and data protection measures. Illinois law provides private right of action enabling individuals to sue for violations. Meanwhile, Texas, Washington, and Arkansas limit enforcement to state attorneys general. California's CPRA treats biometric information as sensitive personal information. Organizations should assess requirements in all jurisdictions where candidates reside and provide appropriately tailored consent processes.
Can candidates refuse biometric liveness detection during hiring processes?
Various reasons may prompt candidates to decline biometric verification including privacy preferences, religious objections, or technical limitations. Organizations should establish accommodation procedures providing alternative identity verification methods that maintain equivalent security without requiring biometric data collection. Rigid refusal to hire candidates who decline biometric checks may create discrimination concerns, particularly when alternative verification approaches exist that satisfy identity assurance requirements through different means.
How accurate is biometric liveness detection at preventing deepfake attacks?
Specific implementation capabilities and attack sophistication determine liveness detection effectiveness against deepfakes. Advanced systems incorporating depth sensing, multi-modal analysis, and challenge-response verification can detect many synthetic media presentations. However, sophisticated deepfake technology continues evolving, creating ongoing adversarial dynamics. Organizations should prioritize vendors demonstrating continuous algorithm updates, independent security testing, and transparent disclosure of known limitations.
What happens when legitimate candidates fail liveness verification checks?
Lighting conditions, camera quality, environmental factors, or system limitations cause false rejections to occur. Organizations should implement escalation procedures allowing candidates to retry verification under improved conditions, access technical support, or complete alternative verification methods. High false rejection rates indicate system configuration issues, inadequate environmental accommodation, or technology limitations requiring vendor engagement or implementation adjustments.
Is biometric liveness detection required for remote hiring compliance?
No federal law mandates biometric liveness detection for general employment screening. Specific industries or contractual relationships may impose identity proofing requirements that liveness detection helps satisfy. Examples include government contractor obligations or financial services regulations. Organizations should assess whether their specific regulatory environment, risk profile, or contractual commitments create identity verification standards that liveness detection addresses rather than assuming universal legal requirements.
How should organizations handle biometric data retention after hiring decisions?
Destruction of biometric identifiers is typically required by state biometric privacy laws when the initial collection purpose has been satisfied or within specified timeframes. In hiring contexts, organizations should establish policies destroying biometric data after hiring decisions finalize, onboarding completes, or document retention periods expire. Vendor agreements should specify data retention responsibilities and provide technical capabilities for timely destruction. Organizations must document and implement actual destruction procedures rather than maintaining indefinite biometric data archives.
Can biometric liveness detection replace traditional background checks?
A distinct function from background checks characterizes liveness detection. It cannot substitute for criminal record searches, employment verification, credential validation, or other screening components. Physical presence during specific interactions is confirmed through liveness detection. However, it provides no information about criminal history, employment background, credentials, or qualifications. Comprehensive hiring verification requires multiple complementary controls addressing different risk dimensions rather than relying on any single technology as a universal solution.
Additional Resources
- Federal Trade Commission: Biometric Information and the FTC Act
https://www.ftc.gov/business-guidance/blog/2023/04/biometric-information-and-ftc-act - National Institute of Standards and Technology: Digital Identity Guidelines
https://pages.nist.gov/800-63-3/ - Illinois Attorney General: Biometric Information Privacy Act Overview
https://www.illinoisattorneygeneral.gov/rights/bipa.html - EEOC: The Americans with Disabilities Act and Technology
https://www.eeoc.gov/laws/guidance/americans-disabilities-act-and-use-software-algorithms-and-artificial-intelligence

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications through the Professional Background Screening Association (PBSA) and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.