Synthetic identity fraud in hiring exploits a structural gap in employment verification: standard background checks validate records against an identity, but rarely verify the identity itself exists as a real person. As manufactured identities mature within credit and data systems, they generate authentic-looking histories that pass conventional screening, creating exposure for organizations across financial, reputational, and compliance dimensions.
Key Takeaways
- Synthetic identities combine real and fabricated data elements to create personas that exist in official records but do not correspond to actual people.
- Employment background checks verify criminal, employment, and credit records tied to a name and Social Security number, not whether that person genuinely owns that identity.
- Fraudsters often age manufactured identities for months or years within financial systems before use, generating transaction histories that mimic legitimate behavior.
- High-risk roles involving financial authority, access to sensitive data, or operational autonomy present the greatest organizational exposure to synthetic identity fraud hiring.
- Multi-layer identity proofing methods compare data from independent sources to help identify inconsistencies that single-verification systems may not surface.
- Organizations can assess vulnerability by evaluating industry exposure, hiring velocity, workforce composition, and access profiles within their existing processes.
- No single technology or screening method eliminates synthetic identity risk; detection requires layered verification appropriate to role-specific risk levels.
- Post-hire monitoring and response protocols address the reality that organizations may discover fraud after employment begins, requiring investigation and legal frameworks.
Understanding Synthetic Identity Construction and Maturation
Synthetic identity fraud in hiring differs fundamentally from stolen identity schemes. Rather than assuming a real person's credentials, perpetrators fabricate new identities by combining legitimate data elements with false information. The most common method pairs a valid Social Security number, often belonging to a minor or someone not actively using credit, with a fabricated name, date of birth, and address.
These manufactured personas do not exist as people, but they establish presence within institutional record systems. The perpetrator applies for credit, utility services, or other accounts under the synthetic identity, gradually building a transactional footprint. Initial applications often face denial, but the inquiries and denials themselves create a credit file.
Over time, synthetic identities may develop credit histories through secured cards, authorized user arrangements, or credit-builder products. Fraud prevention researchers have observed aging periods ranging from several months to multiple years, though timeframes vary based on the sophistication of the scheme and the systems being manipulated. By the time someone uses it for employment purposes, the identity has built up records that background checks verify. It may show rental history, credit accounts in good standing, and even employment records if the fraudster has worked under the identity previously. Because fraudsters construct rather than steal the identity, it may not trigger the specific red flags that traditional verification systems primarily target, such as SSN mismatches with known stolen numbers or identity theft alerts from credit bureaus.
Synthetic identity fraud is forcing HR to think differently about what verification really means. The current system of background checks proves existing records associated with an individual, but does not verify if the individual is even a real person, thus opening up a huge gap in the hiring process. In the current scenario, defensible hiring practices require a move beyond the current system of verification and into a system of layered identity verification.
Why Employment Verification Processes Are Structurally Vulnerable
Standard employment screening methods assume one critical thing: the person presenting an identity genuinely owns it. Background checks verify whether records tied to that identity contain disqualifying information. What they typically skip is verifying whether the applicant legitimately owns the identity they present.
| Verification Method | What It Confirms | What It Does Not Confirm |
| County Criminal Search | No criminal record exists under that name/DOB | The applicant owns that identity |
| SSN Verification | SSA issued the SSN and it shows employment history | The applicant rightfully holds the SSN |
| Document Authentication | The ID is genuine and not forged | The person presenting it lawfully holds it |
| Credit Check | Financial behavior and payment patterns | The applicant opened those accounts |
County criminal record searches query court databases using name, date of birth, and sometimes SSN. If the synthetic identity has no criminal history because someone recently built it or only used it for financial activity, the search returns clean results. The check works exactly as designed but answers the wrong question for synthetic identity detection.
SSN verification traces employment history and confirms the Social Security Administration issued the SSN. However, if the fraudster has selected an SSN and birthdate combination that aligns plausibly, or if the SSN belongs to a minor whose age matches recent issuance, the trace reveals nothing suspicious. The SSN is real, properly formatted, and shows employment history if someone previously used the synthetic identity for work.
Operational Risk Scenarios in Employment Contexts
Synthetic identity fraud in hiring creates exposure across multiple risk categories. The manufactured identity is not simply a credentialing inconvenience but a deliberate concealment tool that enables harmful behavior while complicating accountability.
Internal Fraud and Embezzlement Amplification
An employee with financial system access, payroll authority, or procurement control can divert funds, manipulate records, or approve false transactions. When someone discovers the fraud, the identity trail leads to a fabrication. The person may disappear entirely, and investigators spend resources tracing a phantom. Asset recovery becomes nearly impossible, while civil and criminal proceedings face foundational challenges because no one can verify the defendant's legal identity.
Compliance Failures and Regulatory Exposure
In industries subject to oversight such as healthcare, finance, or government contracting, employing individuals who lack proper vetting can trigger sanctions, fines, or loss of licensure. The organization may show it conducted background checks, but if those checks screened a fictitious person, the compliance framework has failed at a structural level. Regulatory audits or legal actions reveal that someone hired an employee involved in a violation under a false identity.
Security Clearances and Access Compromise
Roles requiring access to protected health information, financial records, intellectual property, or government facilities assume the individual granted access has undergone verification. A synthetic identity allows someone with undisclosed history, foreign connections, or malicious intent to gain access they would have lost under their true identity. The resulting exposure extends beyond the individual's direct actions and includes the broader compromise of systems, data, or operations they were trusted to handle.
Reputational Harm and Stakeholder Confidence
Media coverage of fraud that an employee operating under a manufactured identity perpetrated damages stakeholder confidence. Clients, investors, regulators, and the public view the incident as a systemic failure of due diligence. Even if the organization followed standard screening practices, the narrative centers on employing a fabricated person. Trust and market position recovery can take years and require significant communication and process reform investments.
Detection Limitations in Conventional Screening Methods
County criminal record searches identify convictions, pending charges, and sometimes arrest records tied to a name, date of birth, and jurisdiction. They function within the scope of court system databases. If someone has never used the synthetic identity in criminal activity, or if any criminal history belongs to the legitimate owner of the misappropriated SSN rather than the applicant, the search will not surface disqualifying information.
National criminal database searches gather records from multiple jurisdictions but inherit the same limitation. They compile data from courts, correctional facilities, and law enforcement agencies tied to names and identifiers those agencies report. A synthetic identity with no criminal history, or one someone built carefully to avoid overlap with existing criminal records, will return a clean result.
Key limitations of standard screening include:

- SSN trace reports show employment and address history but may not flag well-built synthetic identities using valid, inactive SSNs from minors
- Document verification confirms identity documents are genuine but does not confirm the person presenting the document lawfully holds it
- Employment verification contacts previous employers to confirm job titles and dates, which supports the resume if someone used the synthetic identity at a prior employer
- Credit checks validate financial behavior but do not verify person-to-SSN binding, and well-aged synthetic identities may have better credit than legitimate applicants
The absence of extensive history does not automatically disqualify someone. It can reflect legitimate circumstances such as recent immigration, previous self-employment, or minimal credit use. The verification process works, but it validates the document or record, not the person-to-identity binding.
Identity Proofing Methodology for Hiring Processes
Effective detection of synthetic identity fraud hiring requires identity proofing that verifies the person, not just the records. Multi-layer verification introduces backup checks and cross-validation from independent data sources. The goal is to help identify inconsistencies that single-point checks may miss.
Multi-Source Data Triangulation
This approach compares information from systems that do not share underlying data. Employers can verify an applicant's claimed address history not only through SSN trace but also through utility records, voter registration, property records, or prior employer locations. If an applicant claims to have lived at an address for three years, but utility databases show no account history and property records indicate a different occupant, the gap warrants further investigation.
Document-to-Person Binding
This method links identity documents to the physical or biometric traits of the applicant. It goes beyond examining a driver's license photo and includes live biometric capture, such as facial recognition or fingerprint verification, compared against government databases or document-embedded biometric data where available. If an applicant presents a driver's license with a photo that does not match their appearance, or if biometric comparison fails, the document may be genuine but in the wrong hands.
Timeline Consistency Analysis
Manufactured identity detection methods include reviewing how long accounts have been open, when the first credit inquiry occurred, and whether the pattern of activity reflects normal life progression. A 35-year-old applicant whose entire financial and address history began three years ago presents a red flag. Legitimate explanations exist, such as recent immigration or recovery from identity theft, but the anomaly justifies additional verification rather than automatic acceptance.
Out-of-Wallet Authentication
This technique uses knowledge-based verification questions drawn from the applicant's claimed history. These questions reference information not easily obtained through document theft, such as previous loan amounts, former employers, or addresses from years past. If the applicant cannot answer questions about their own claimed history, the identity may not belong to them. This method works best when questions come from data sources the applicant has not directly provided.
Risk-Based Verification Frameworks for Resource Allocation
Not all roles present equal exposure to synthetic identity fraud hiring. Organizations must allocate verification resources based on risk profiles to balance security and efficiency. A risk-based framework sorts positions and applies appropriate verification intensity.
| Role Category | Risk Level | Verification Approach |
| Financial authority roles | High | Enhanced identity proofing, multi-source comparison, biometric verification |
| Sensitive data access | High | Document-to-person binding, timeline consistency analysis |
| Executive/leadership | High | Full verification including out-of-wallet authentication |
| Remote/distributed workforce | Medium-High | Adapted verification for distributed workflows, video interview protocols |
| Standard operational roles | Medium | Baseline screening with SSN validation and document review |
| Entry-level, high-supervision | Low-Medium | Conventional background checks with manager oversight |
High-risk roles include those with financial authority, such as accounting personnel, procurement officers, or treasury staff. Employees who can approve transactions, access bank accounts, or manipulate financial records create direct pathways for embezzlement if they operate under fraudulent identities. Enhanced identity proofing for these positions offers cost-effective protection relative to potential loss.
Roles with access to sensitive data, including personally identifiable information, protected health information, intellectual property, or trade secrets, also warrant heightened verification. A synthetic identity in a database administrator, HR analyst, or research scientist role enables data theft or spying.
Industry-specific regulatory requirements often set minimum verification standards. Financial institutions subject to Federal Deposit Insurance Corporation or Office of the Comptroller of the Currency oversight face explicit identity verification mandates. However, these regulatory floors establish verification baselines that do not always account for synthetic identity fraud hiring risks that emerged after regulators wrote the rules.
Organizational Vulnerability Assessment for Synthetic Identity Exposure
Assessing organizational vulnerability to synthetic identity fraud in hiring begins with evaluating industry exposure. Financial services, healthcare, insurance, and government sectors may face heightened exposure due to employee access to funds, sensitive data, and benefits systems, though synthetic identity fraud in hiring can affect organizations across industries. Any organization with remote work, high-volume hiring, or roles involving financial or data access faces material risk.
Critical vulnerability factors include:
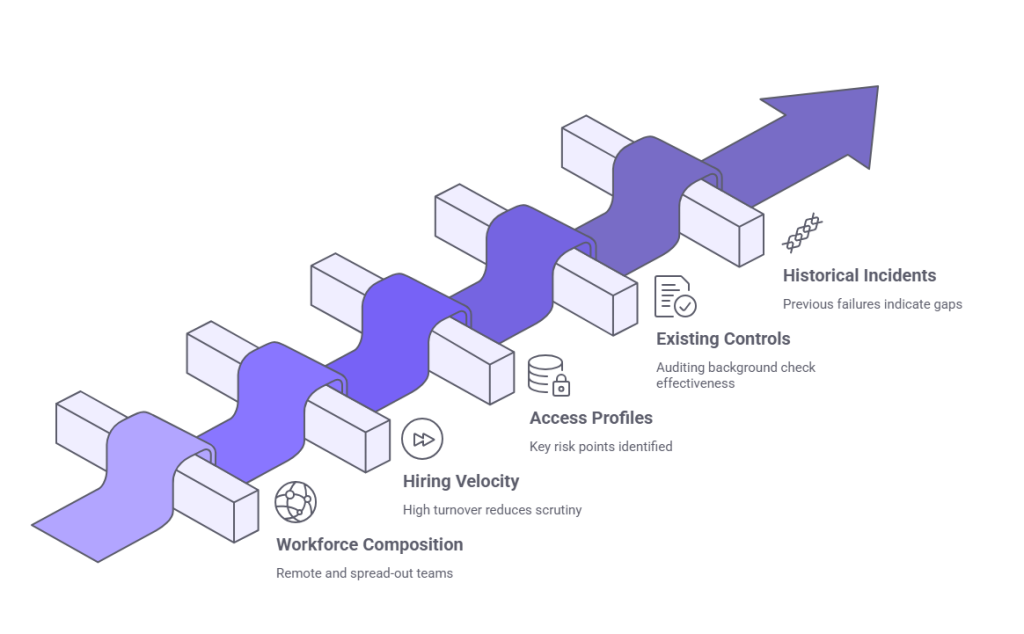
- Workforce composition: Organizations with significant percentages of remote employees, contract workers, or spread-out teams face greater challenges in verifying identity authenticity
- Hiring velocity and volume: High-turnover industries such as logistics, retail, or hospitality may speed up background checks to avoid bottlenecks, reducing per-candidate scrutiny
- Access profiles: Mapping which roles have financial system access, payroll authority, procurement approval, database administration, or customer data access identifies key risk points
- Existing verification controls: Auditing whether background checks include SSN validation, how employers verify document authenticity, and if enhanced verification applies to high-risk roles
- Historical incidents: Previous embezzlement, data breaches, or fraud involving employee identity gaps indicate existing screening failed
Access profiles within the organization reveal where synthetic identity fraud hiring would cause the greatest harm. If twenty employees can start wire transfers, those twenty positions represent high-value targets for synthetic identity schemes. If administrative assistants have access to executive calendars, emails, and confidential files, their roles carry risk larger than their titles suggest.
Hiring velocity does not eliminate risk; it focuses it in process design. Organizations hiring hundreds or thousands of employees annually may approve candidates who pass threshold checks through automated systems, with manual review occurring only for flagged cases. Synthetic identities built to pass automated screening proceed without human verification.
Common Misconceptions About Synthetic Identity Detection
One persistent misconception holds that thorough background checks catch all identity fraud. Standard screening verifies records, not identity ownership. A clean criminal record, verified employment history, and acceptable credit report confirm the identity being screened has no disqualifying history. They do not confirm the applicant owns that identity.
Another misunderstanding suggests synthetic identity fraud hiring primarily affects financial institutions. While banks and lenders face frequent targeting for synthetic identity credit fraud, employment fraud has distinct motivations. Perpetrators seek income, access to systems, or positioning for embezzlement. Any organization with payroll, data, or operational access presents an opportunity.
The assumption that synthetic identity fraud is rare because reports are infrequent reflects a detection problem, not a prevalence reality. Fraudsters design synthetic identities to evade detection. When fraud occurs, organizations often attribute it to employee misconduct without recognizing the employee's identity was fabricated.
Some organizations believe artificial intelligence or automated screening tools solve synthetic identity detection without human help. Automated systems excel at flagging anomalies, but they operate within the constraints of their training data and rules. Multi-layer identity authentication requires human judgment, cross-source verification, and investigative processes that technology supports but does not replace.
Finally, a misconception exists that synthetic identity fraud is easily distinguishable from stolen identity fraud. In practice, distinguishing between the two requires investigation. A flag for SSN mismatch could indicate either a stolen SSN or a synthetic identity. The detection process is the same: verify the person-to-identity binding through independent means.
Monitoring and Response Protocols for Post-Hire Discovery
Organizations may not detect synthetic identity fraud hiring until after employment begins. Post-hire discovery occurs when employers conduct reverification, employees update documents, or fraud triggers investigation. Organizations need protocols to address discovery without assuming all gaps indicate fraud.
Continuous monitoring systems track changes in employee records, such as address updates, name changes, or SSN corrections. Frequent changes or inconsistencies between employee-provided data and payroll or benefits records can signal synthetic identity use. Monitoring flags these anomalies for manual review.
Reverification during employment, particularly for roles with escalating access or responsibility, provides a checkpoint. Employers can subject employees promoted to financial or data-access roles to enhanced background checks or identity proofing as a condition of the new position. This creates an opportunity to detect synthetic identities that passed initial screening but cannot withstand deeper verification.
Post-hire response protocol steps:
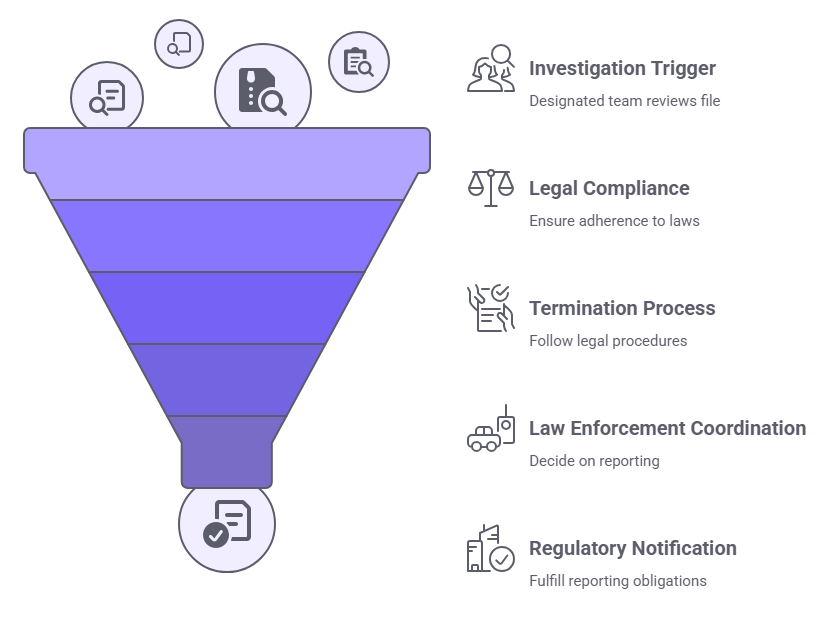
- Investigation trigger: When a gap appears, a designated team reviews the employee's file, contacts prior employers independently, and verifies identity documents through issuing authorities
- Legal compliance: Balance fraud detection with privacy and employment law rules; accusations without evidence create wrongful termination or defamation exposure
- Termination process: If someone confirms synthetic identity, follow employment law in the relevant jurisdiction; employment contracts were entered under false pretenses
- Law enforcement coordination: Determine whether to report fraud based on industry obligations and jurisdiction requirements
- Regulatory notification: Financial institutions, healthcare providers, and government contractors may have mandatory reporting obligations for identity fraud
Legal considerations in termination and reporting are complex. Reporting creates a record and may aid prosecution, but it also exposes the organization to scrutiny regarding its hiring practices. Coordination with law enforcement and regulators depends on industry and jurisdiction.
Conclusion
Synthetic identity fraud in hiring exploits the structural gap between record verification and identity authentication. Organizations must recognize that conventional background checks validate histories, not people. Multi-layer identity proofing, risk-based verification frameworks, and post-hire monitoring create defensible hiring processes suited to current fraud complexity.
Frequently Asked Questions
What is the primary difference between synthetic identity fraud and stolen identity fraud in hiring?
Stolen identity fraud uses a real person's complete identity without permission, while synthetic identity fraud creates a new, fictitious identity by combining real and fabricated data elements. Synthetic identities exist in records systems but do not correspond to actual people. Detection methods differ because synthetic identities have no legitimate owner to report the fraud, and they generate authentic records that pass standard verification.
How long does it typically take for a fraudster to build a synthetic identity before using it for employment?
Fraudsters commonly age manufactured identities for six months to two years before deployment. This period allows the identity to establish credit history, build up address records, and generate transaction data that mimic legitimate behavior. Longer aging periods create more convincing identities with deeper histories, making detection harder.
Can standard SSN verification detect synthetic identities effectively?
SSN verification confirms a Social Security number is valid and checks for mismatches between issuance date and claimed birthdate. However, if a synthetic identity uses a valid SSN from a minor or inactive individual with an age-consistent issuance date, standard verification will not detect the fraud. Enhanced verification requires cross-checking SSN data with independent sources such as utility records or biometric validation.
Which industries face the highest risk from synthetic identity fraud in hiring?
Financial services, healthcare, insurance, and government contracting face elevated risk due to access to funds, sensitive data, and regulatory systems. However, any organization with roles involving financial authority, data access, or remote work is vulnerable. Risk relates to access and opportunity rather than industry alone.
What role does biometric verification play in detecting synthetic identities during hiring?
Biometric verification links identity documents to the physical person presenting them by comparing facial recognition, fingerprints, or other biometric data. This helps prevent someone from using a genuine document issued to a synthetic identity if their biometrics do not match, though effectiveness depends on system accuracy, anti-spoofing capabilities, and database integration.
Are there legal restrictions on the types of identity proofing employers can conduct?
Employers must comply with federal and state laws governing background checks, data privacy, and discrimination. The Fair Credit Reporting Act regulates use of consumer reports, requiring disclosure and consent. State laws may impose additional restrictions on biometric data collection, use of criminal records, or inquiry timing.
What are early warning signs during the hiring process that an applicant may be using a synthetic identity?
Warning signs include gaps between documents and claimed history, shallow identity history for the applicant's age, reluctance to provide verifiable references, and knowledge-based authentication failures. SSN traces showing recent activity origins, mismatched issuance locations, or minimal address history also warrant scrutiny. Multiple anomalies justify enhanced verification before proceeding.
How should organizations respond if they discover an employee was hired under a synthetic identity?
Response protocols should include stopping the employee's access to systems and data, conducting an internal investigation to determine whether fraud occurred, consulting legal counsel regarding termination procedures, and evaluating whether law enforcement or regulatory reporting is required. Documentation of the discovery process and decision rationale is critical for defending against potential claims and showing due diligence to regulators.
Additional Resources
- Synthetic Identity Fraud in the U.S. Payment System
https://www.federalreserve.gov/econres/notes/feds-notes/synthetic-identity-fraud-in-the-us-payment-system-20180802.htm - Federal Trade Commission: Identity Theft and Online Security
https://consumer.ftc.gov/identity-theft-and-online-security - Using Consumer Reports for Employment Purposes (FCRA Section 604)
https://www.ftc.gov/business-guidance/resources/using-consumer-reports-employment-purposes - Social Security Administration: Protecting Your Social Security Number
https://www.ssa.gov/pubs/EN-05-10064.pdf - Department of Homeland Security: E-Verify Program Overview
https://www.e-verify.gov/about-e-verify/e-verify-overview

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications through the Professional Background Screening Association (PBSA) and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.