By 2026, identity fraud in gig hiring has evolved from an edge-case risk to a structural vulnerability in decentralized onboarding systems. Organizations relying on contractor labor at scale must implement proportional identity verification frameworks that address synthetic identities, credential misuse, and platform-mediated fraud without over-indexing on compliance theater or friction-heavy processes.
Key Takeaways
- Identity fraud in gig hiring exploits the absence of in-person validation, physical document inspection, and traditional HR controls.
- Synthetic identities, stolen credentials, and impersonation tactics target remote onboarding workflows and self-service portals.
- Gig worker fraud differs from W-2 employee fraud due to shorter engagement timelines, platform intermediation, and weaker audit trails.
- Regulatory frameworks in 2026 include state contractor verification requirements, IRS reporting changes, and evolving platform liability standards.
- Identity verification methods range from document validation to biometric matching, each with distinct cost, friction, and accuracy trade-offs.
- Operational risk points include bulk contractor additions, automated approvals, and decentralized hiring authority.
- Red flags for potential fraud include mismatched identity documents, out-of-pattern addresses, and rapid re-application cycles.
- A proportional verification framework balances risk exposure, role sensitivity, and user experience without universal over-investment.
Identity Fraud in the Gig Economy: Definitions and Scope
Identity fraud in contractor hiring involves the intentional misrepresentation of personal identifiers to gain unauthorized employment, evade tax reporting, access platform incentives, or commit financial misconduct. Unlike traditional employment fraud, gig worker identity verification challenges operate in environments where onboarding occurs remotely, documents are submitted digitally, and validation processes rely on automated systems rather than human review.
Core Fraud Types
| Fraud Type | Definition | Common Use Case |
| Synthetic Identity Fraud | Combines real and fabricated information to create a persona that does not correspond to an actual individual | Passing database checks while evading detection through traditional verification methods |
| Stolen Identity Fraud | Unauthorized use of another person's legitimate credentials | Targeting individuals with clean records whose information has been compromised through data breaches or phishing |
| Impersonation Fraud | Misrepresenting oneself as another person | Bypassing eligibility requirements, background check disqualifications, or platform bans |
A synthetic identity may use a valid Social Security Number paired with a fictitious name and address. This enables the fraudster to pass basic database checks while evading detection through traditional verification methods.
Scale and Impact
The growth of platform-mediated labor has expanded the attack surface for identity fraud. Remote-first onboarding eliminates opportunities for document inspection, in-person interviews, and behavioral observation. Self-service portals allow bulk account creation with minimal human oversight. Gig platforms often prioritize onboarding speed over verification rigor, creating exploitable gaps in identity assurance.
Organizations hiring contractors at scale face operational, financial, and reputational exposure. Fraudulent workers may deliver substandard services, misappropriate client data, commit theft, or create liability through unauthorized actions. Tax fraud involving misreported earnings or fabricated identities can trigger IRS penalties and audit scrutiny. Some organizations may underestimate fraud prevalence if detection mechanisms are limited or if incidents do not result in immediate financial loss or compliance violations.
Why Gig Worker Fraud Differs from W-2 Employee Fraud
Traditional employment relationships include structural safeguards that do not translate to contractor engagements. Understanding these differences is essential for designing effective contractor identity fraud prevention strategies.
Onboarding Process Differences
W-2 employees typically undergo multi-stage onboarding that includes:
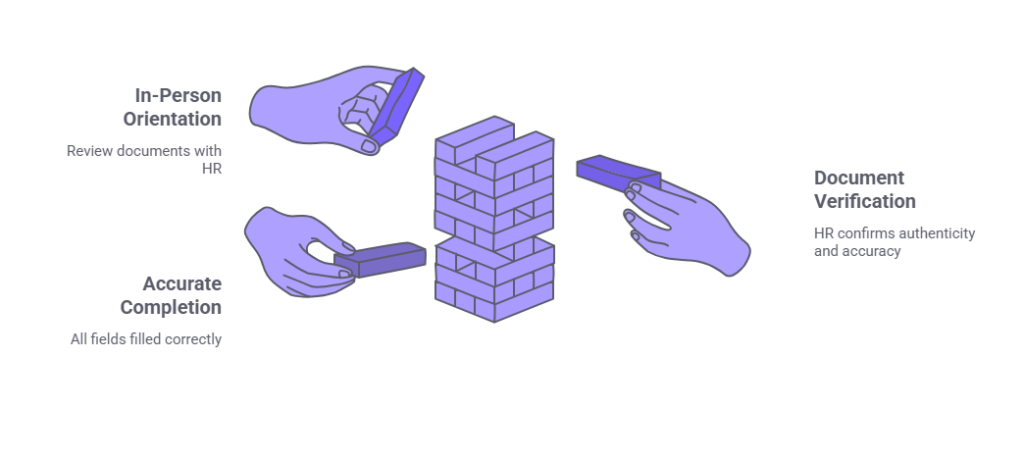
- In-person orientation
- Physical document review for Form I-9 compliance
- Direct interaction with HR personnel
These touchpoints create friction for fraudsters and increase detection likelihood. Gig workers, by contrast, often complete onboarding entirely online. Document uploads replace physical inspection. Automated systems approve applications based on algorithmic checks. Human review occurs only in exception cases, if at all.
Engagement Duration and Oversight
Full-time employees remain under continuous organizational oversight. Payroll systems, benefits administration, and performance management create ongoing audit trails. Anomalies in identity data surface through tax withholding discrepancies, benefits enrollment issues, or internal communications.
Gig engagements may last hours, days, or weeks. Contractors interact with clients through platform interfaces or limited email exchanges. Payment occurs via third-party systems that do not require the same identity validation as employer payroll. Short engagement timelines reduce the window for detecting fraud before the relationship ends.
Verification Incentives and Liability
Employers bear direct liability for employment eligibility verification under federal immigration law. Form I-9 compliance requires physical document inspection and retention. Failure to comply results in fines and potential criminal liability.
Platform-mediated gig work distributes verification responsibility across platforms, clients, and contractors. Liability frameworks remain unsettled in many jurisdictions. Platforms may impose identity verification as a condition of access but lack legal mandates equivalent to Form I-9. Clients hiring through platforms often assume verification has occurred, creating a verification gap.
Common Fraud Tactics Targeting Gig Platforms
Understanding how fraud manifests in gig hiring enables organizations to identify vulnerabilities and implement targeted controls. The following tactics represent observable patterns in contractor onboarding fraud.
Fake Social Security Numbers for Tax Avoidance
Some individuals use fabricated or borrowed Social Security Numbers to avoid tax reporting obligations. Gig platforms issue Form 1099 based on the SSN provided during onboarding. If the number does not match IRS records, the platform may face reporting penalties, and the worker evades income tax liability.
Credential Reuse After Platform Bans
Platforms frequently ban users for policy violations, safety incidents, or fraudulent activity. Banned individuals create new accounts using stolen or synthetic identities to regain platform access. Without robust gig worker identity verification, platforms struggle to prevent serial violators from re-entering their ecosystems.
Signing Bonus and Incentive Fraud
Platforms offer financial incentives to attract workers during high-demand periods. Fraudsters create multiple accounts using distinct identities to claim bonuses repeatedly. Synthetic identities allow individuals to pass basic verification while maintaining the appearance of unique users.
Document Forgery and Manipulation
Digital document submission enables large-scale forgery. Fraudsters alter driver's licenses, utility bills, and bank statements using widely available software. Automated verification systems that rely on visual inspection without cryptographic validation or database cross-checks often fail to detect manipulated documents.
Third-Party Impersonation
Some gig workers complete onboarding under their own identity, then transfer account access to a third party. The third party performs the work while the verified individual retains legal accountability. This tactic exploits platforms that verify identity at onboarding but lack ongoing authentication during work performance.
Regulatory and Compliance Context (2026)
The regulatory landscape for contractor identity verification continues to evolve. Organizations must navigate federal tax reporting requirements, state-level contractor verification laws, and industry-specific mandates.
IRS Information Reporting Changes
The IRS continues to scrutinize Form 1099 reporting accuracy. Platforms and businesses that issue 1099s are generally expected to confirm that the name and SSN combination corresponds to IRS records. Mismatches may result in B-notices, which typically require corrective action. In cases of persistent non-compliance, backup withholding requirements may apply. Organizations should consult tax advisors or IRS guidance for jurisdiction and situation-specific obligations. While IRS rules do not mandate upfront identity verification beyond name and SSN validation, organizations face operational risk if they onboard workers with invalid credentials.
State Contractor Verification Requirements
Some states have enacted laws requiring businesses to verify the work authorization status of independent contractors. These laws vary in scope, enforcement mechanisms, and applicability thresholds. Organizations operating in multiple states should assess jurisdiction-specific requirements. Some organizations adopt verification processes that satisfy the most stringent applicable standard as a risk-mitigation approach, though legal requirements vary.
Platform Liability Trends
Courts and regulators increasingly scrutinize whether platforms exercise sufficient control over workers to warrant employer-like responsibilities. While most gig platforms maintain that workers are independent contractors, platform liability for worker misconduct, fraud, or harm remains a contested legal issue. Platforms that implement identity verification may, depending on jurisdiction and circumstances, reduce exposure to claims alleging inadequate vetting. Legal standards for what constitutes reasonable care vary. Organizations should consult legal counsel when assessing platform liability risk.
Data Privacy and Verification Limits
Identity verification processes must comply with federal and state privacy laws. Collecting, storing, and processing identity documents, biometric data, and Social Security Numbers triggers obligations under laws such as the Gramm-Leach-Bliley Act, state data breach notification statutes, and emerging comprehensive privacy frameworks. Organizations must limit data collection to what is necessary, implement appropriate security controls, and provide transparency about verification practices.
Identity Verification Methods: Comparative Framework
Organizations hiring gig workers can deploy multiple verification methods, each with distinct operational characteristics. The following framework compares how to verify gig worker identity using common approaches.
| Method | Strengths | Limitations |
| Document Verification | Widely accepted; supports compliance with tax reporting and right-to-work requirements; scalable through automation | Vulnerable to high-quality forgeries; does not confirm the document bearer is the person submitting it; limited effectiveness against synthetic identities |
| Knowledge-Based Authentication | Low friction; does not require document upload; leverages existing data ecosystems | Susceptible to social engineering and data breaches; declining accuracy as personal information becomes more accessible online |
| Biometric Matching | High assurance that the person submitting documents is the individual depicted; effective against impersonation fraud | Requires user consent and compliance with biometric privacy laws; potential for algorithmic bias; technical barriers for some users |
| Database Cross-Checks | Validates identity authenticity; detects fabricated SSNs; integrates with existing background check workflows | Does not confirm the applicant is the person associated with the validated identity; limited utility against stolen identities |
| Multi-Factor Identity Proofing | Substantially higher fraud resistance; aligns with NIST identity assurance level guidelines | Increased cost; longer onboarding timelines; potential user abandonment in competitive labor markets |
Document Verification
Document verification involves validating government-issued identification, such as driver's licenses, passports, or state ID cards. Basic document verification for contractors checks for visual authenticity markers, such as holograms, fonts, and formatting. Advanced methods use optical character recognition to extract data and cross-reference it against issuing authority databases.
Knowledge-Based Authentication
Knowledge-based authentication (KBA) challenges applicants to answer questions derived from credit reports, public records, or financial histories. Questions typically reference past addresses, loan amounts, or account opening dates. Industry observers have noted concerns that KBA effectiveness may decline as personal information becomes more accessible online, though the extent of this impact varies by implementation and context.
Biometric Matching
Biometric verification compares a live selfie or video to a photo on a government-issued ID. Liveness detection prevents the use of static images or deepfakes. Advanced systems use facial recognition algorithms to confirm identity with high accuracy.
Database Cross-Checks
Database verification cross-references submitted identity information against authoritative sources, such as Social Security Administration records, credit bureaus, or state vital records. Matches confirm that the identity exists and that key attributes align.
Multi-Factor Identity Proofing
Multi-factor identity proofing combines two or more verification methods to achieve higher assurance. For example, an organization might require document verification for contractors, biometric matching, and database cross-checks. This layered approach reduces the likelihood that a fraudster can satisfy all verification criteria.
Operational Risk Points in Gig Onboarding Workflows
Fraud enters gig hiring through specific process weaknesses. Identifying these risk points enables targeted intervention through onboarding fraud prevention controls.
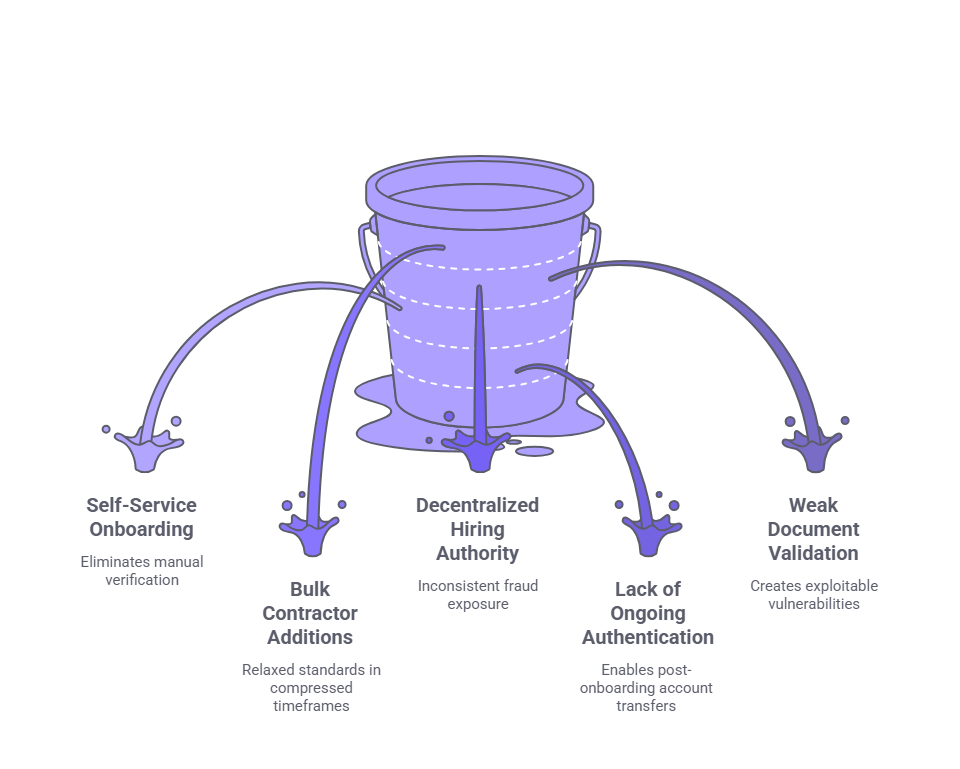
- Self-Service Onboarding Portals: Platforms and clients that enable workers to complete onboarding without human interaction reduce friction but eliminate manual verification checkpoints. Automated systems approve applications based on algorithmic rules, which fraudsters reverse-engineer to identify bypass strategies.
- Bulk Contractor Additions: Organizations that onboard large contractor cohorts in compressed timeframes often relax verification standards to meet operational deadlines. Fraudsters exploit these periods by submitting applications en masse, knowing that review rigor will be lower.
- Decentralized Hiring Authority: In organizations where individual managers or departments hire contractors without centralized oversight, verification standards vary. Some managers prioritize speed and relationship trust over formal validation, creating inconsistent fraud exposure.
- Lack of Ongoing Authentication: Many organizations verify identity at onboarding but lack mechanisms to confirm that the verified individual is the person performing work. This gap enables post-onboarding account transfers and credential sharing.
- Weak Document Validation Standards: Organizations that accept scanned or photographed documents without verifying authenticity, checking for tampering, or cross-referencing data against external sources create exploitable vulnerabilities.
Signals of Potential Identity Fraud
Operational teams can monitor for behavioral and data indicators that suggest identity fraud. Recognizing these signals supports early detection and risk mitigation.
Document and Data Anomalies
- Mismatched Name Formats: Discrepancies between the name on a driver's license, Social Security card, and platform profile may indicate document forgery or credential misuse. While some variation is legitimate, significant mismatches warrant further review.
- Conflicting Identity Documents: Submitted documents that contain inconsistent information, such as different dates of birth or SSNs, indicate potential fraud. Organizations should flag applications where document data does not reconcile.
Behavioral Red Flags
- Out-of-Pattern Addresses: Addresses that do not align with geographic norms for the role, such as a distant state for a local delivery gig, may signal fraud. Frequent address changes or addresses associated with mail-forwarding services raise additional concerns.
- Rapid Re-Application Cycles: Individuals who apply, are rejected, and reapply shortly thereafter using slightly altered information may be attempting to bypass verification controls. Monitoring for repeat email domains, phone numbers, or device identifiers can surface these patterns.
- Unusual Payment Method Preferences: Requests for payment via prepaid cards, cryptocurrency, or third-party accounts not in the worker's name may indicate efforts to obscure identity or evade financial reporting.
Digital Footprint Considerations
Low digital footprint alone is not conclusive. However, the absence of any online presence, social media accounts, or professional history for an individual claiming significant experience warrants additional scrutiny, particularly for roles requiring expertise or access to sensitive systems.
Building a Proportional Verification Framework
Effective gig worker identity verification balances fraud risk, operational efficiency, regulatory compliance, and user experience. A proportional framework tailors verification rigor to role-specific risk factors.
Assessing Role-Specific Risk
Not all gig roles carry equivalent fraud risk. Organizations should evaluate the following factors:

- Access to sensitive data or systems: Roles involving client information, proprietary data, or system access require higher assurance.
- Financial exposure: Positions with payment handling, inventory access, or expense authority increase fraud impact.
- Physical access: Contractors entering facilities, homes, or restricted areas present safety and security risks.
- Regulatory requirements: Certain roles may trigger industry-specific verification mandates.
Tiered Verification Approaches
Organizations can implement tiered verification based on risk assessment. The following table illustrates a sample framework.
| Tier | Risk Level | Role Examples | Verification Methods |
| Tier 1 | Low Risk | Short-term, low-access roles | Document upload, database SSN validation |
| Tier 2 | Moderate Risk | Limited data access, multi-week engagements | Document validation, biometric matching or KBA |
| Tier 3 | High Risk | System access, financial authority, physical entry | Document validation, biometric matching, database cross-checks, background screening |
Balancing Friction and Security
Excessive verification creates user abandonment, particularly in competitive gig markets. Organizations should communicate verification requirements transparently during application, minimize redundant data requests across onboarding steps, and optimize mobile experiences. Providing user support for verification issues reduces legitimate applicant drop-off.
Compliance Minimums vs. Risk Appetite
Regulatory compliance establishes baseline requirements but does not necessarily address all fraud risks. Organizations should determine whether their risk tolerance justifies verification beyond legal minimums. For example, a platform may not be legally required to implement biometric verification but may choose to do so to reduce fraud losses and protect brand reputation.
No verification framework eliminates all fraud risk. Organizations should view identity verification as one component of a broader risk-management strategy that includes monitoring, incident response, and continuous process improvement.
Continuous Improvement and Monitoring
Fraud tactics evolve. Organizations may choose to monitor verification failure rates, fraud incident trends, and emerging threat intelligence. Periodic audits of onboarding workflows, document authenticity, and identity match accuracy inform iterative improvements.
Common Misconceptions About Gig Worker Verification
Several widely held assumptions undermine effective fraud prevention. Correcting these misconceptions strengthens organizational risk posture.
- "The Platform Already Verified Them": Clients hiring through gig platforms often assume the platform has conducted comprehensive identity verification. In reality, platform verification standards vary widely. Some platforms perform minimal checks, while others implement multi-factor verification. Clients benefit from understanding platform verification practices and supplementing them when necessary.
- "A Social Security Number Equals a Verified Identity": Possession of an SSN does not confirm identity authenticity. SSNs are widely compromised through data breaches. Fraudsters use stolen or fabricated SSNs that may pass basic validation checks. Organizations typically treat SSN validation as one component of identity verification, not a standalone solution.
- "Document Upload Equals Document Verification": Accepting uploaded documents without validation does not constitute verification. Automated systems that store documents without checking authenticity, cross-referencing data, or detecting tampering provide minimal fraud protection.
- "Fraud Is Rare Enough to Ignore": Some organizations may underestimate fraud prevalence if detection mechanisms are limited. Identity fraud that does not result in immediate financial loss, safety incidents, or compliance violations may never surface. The absence of detected fraud does not indicate the absence of fraud risk.
Conclusion
Identity fraud in gig hiring represents a persistent and evolving operational challenge. By 2026, organizations relying on contractor labor must implement verification frameworks that address synthetic identities, credential theft, and platform-specific vulnerabilities. Proportional, risk-based approaches balance security, user experience, and compliance obligations without imposing universal over-investment or under-protection.
Frequently Asked Questions
What is the difference between identity proofing and identity verification?
Identity proofing establishes that an identity exists and belongs to a real person, typically through document validation and database cross-checks. Identity verification confirms that the individual presenting the identity is the legitimate owner, often using biometric matching or knowledge-based authentication. Both processes serve distinct but complementary roles in fraud prevention.
Can gig platforms legally require biometric verification?
Platforms may require biometric verification as a condition of participation if they comply with applicable biometric privacy laws. States such as Illinois, Texas, and Washington impose consent, disclosure, and data handling requirements for biometric data collection. Platforms operating in multiple jurisdictions often adopt processes that satisfy the most stringent applicable standard, though compliance approaches vary. Legal counsel should be consulted.
How do synthetic identities pass background checks?
Synthetic identities combine real and fabricated information to create a persona that appears legitimate in databases. A synthetic identity may use a valid SSN, fabricated name, and fictitious address. Background checks query databases using the submitted information and return results for the SSN's actual owner or no results if the identity has no history. Without cross-referencing multiple data points or verifying document authenticity, background checks may not detect synthetic identities.
Are Social Security Number validation services legally required for gig workers?
Federal law does not mandate SSN validation for independent contractors beyond ensuring the name and SSN combination matches for Form 1099 reporting. However, validating SSNs against Social Security Administration or IRS databases reduces reporting errors, prevents tax fraud, and minimizes administrative burden from IRS B-notices.
What are the risks of accepting government IDs without verification?
Accepting uploaded IDs without verification exposes organizations to document forgery, stolen identity fraud, and impersonation. High-quality fake IDs are widely available, and digital document submission eliminates physical inspection opportunities. Verification should include authenticity checks, data extraction, and cross-referencing against authoritative sources.
How can organizations detect if a contractor transferred account access to another person?
Detecting post-onboarding account transfers requires ongoing authentication. Methods include periodic biometric re-verification, behavioral analytics such as login patterns or device fingerprints, and random video check-ins for high-risk roles. Platforms can also monitor for anomalies in work patterns, geolocation, or communication styles.
Do state Ban-the-Box laws apply to gig worker verification?
Ban-the-Box laws typically restrict when employers may inquire about criminal history during the hiring process. These laws generally apply to employees, and applicability to independent contractors varies by jurisdiction. Some jurisdictions extend protections to contractors, while others do not. Organizations should consult jurisdiction-specific guidance and avoid conflating identity verification with criminal history screening. Identity verification confirms who someone is, while background checks assess suitability based on history.
What is the legal liability if a fraudulent gig worker causes harm?
Liability depends on the relationship structure, jurisdiction, and nature of the harm. In some circumstances, platforms or clients that fail to implement verification measures could face negligence or related claims if a fraudulent worker causes harm. Liability analysis is fact-specific and varies by jurisdiction. Organizations should consult legal counsel. Contracts often allocate risk, but contractual indemnification does not eliminate all exposure. Robust identity verification reduces both direct harm and potential liability for failure to exercise reasonable care.
Additional Resources
- NIST Digital Identity Guidelines (SP 800-63)
https://pages.nist.gov/800-63-3/ - IRS Information Returns (Form 1099) Overview
https://www.irs.gov/businesses/small-businesses-self-employed/forms-and-associated-taxes-for-independent-contractors - Federal Trade Commission: Identity Theft and Online Security
https://www.ftc.gov/identity-theft-and-online-security - Social Security Administration: Employer W-2 Filing Instructions and Information
https://www.ssa.gov/employer/ - Department of Homeland Security: Form I-9 Compliance
https://www.uscis.gov/i-9-central

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.