Identity theft in job applications occurs when individuals use stolen, synthetic, or fraudulent credentials to bypass employment screening and gain positions under false pretenses. For employers, this represents operational, legal, and financial risk requiring proportionate verification protocols aligned with role sensitivity and regulatory obligations.
Key Takeaways
- Identity theft job application fraud includes stolen Social Security Numbers, synthetic identities, and impersonation schemes designed to evade background checks.
- Motivations range from concealing criminal history or immigration status to enabling theft, espionage, or organized fraud operations.
- Standard visual ID checks and self-reported information often fail to detect sophisticated identity fraud during hiring.
- Employers face FCRA liability, I-9 penalties, negligent hiring claims, payroll complications, and reputational harm when fraud succeeds.
- Red flags include SSN issuance inconsistencies, address history gaps, document anomalies, and behavioral cues during onboarding.
- Verification mechanisms such as SSN traces, address validation, document authentication, and E-Verify each have specific detection capabilities and limitations.
- Legal compliance requires balancing fraud prevention with FCRA permissible purpose rules, I-9 requirements, and state privacy protections.
- Proportionate identity verification protocols tier verification intensity by role risk, integrate detection into hiring workflows, and avoid common practitioner mistakes.
Scope and Mechanics of Identity Theft in Employment
Identity theft in hiring contexts differs fundamentally from resume embellishment or credential misrepresentation. It involves the deliberate use of another person's identifying information, fabricated composite identities, or impersonation to circumvent employment screening and establish a fraudulent work relationship. The following table outlines the three primary types of identity theft job application fraud:
| Fraud Type | Technique | Detection Challenge |
| Stolen Identity Use | Applicants use legitimate SSNs, names, and DOBs belonging to real individuals obtained through breaches or dark web markets | Background checks return clean results tied to the victim's actual history |
| Synthetic Identity Fraud | Combines real SSNs (often minors or deceased) with fictitious names and DOBs | Credit bureaus and employment databases lack sufficient data to flag fabricated personas immediately |
| Impersonation Schemes | Applicants use their own names but present false documents or hire proxies for interviews | Remote hiring reduces visual and behavioral verification opportunities |
Unlike inflated job titles or unverified degrees, identity fraud targets the foundational question of who the applicant actually is. Detection requires validation of identity documents, cross-referencing data sources, and scrutinizing inconsistencies that typical reference checks do not reveal.
In the new generation hiring, there is a need to take the time at the right moments to dig a little deeper in screening the candidates. It’s not about making the hiring process more difficult; it’s about being intentional and consistent when it comes to risk assessment. In today's environment, effective recruiting means going beyond the profile and ensuring the person behind it aligns with it.
Motivations and Actor Profiles
Understanding why individuals commit identity theft job application fraud helps employers assess risk by role type and industry. Motivations typically fall into five categories, each presenting distinct risk profiles for employers.
Concealing Disqualifying Criminal History
Applicants with felony convictions, particularly for theft, fraud, or violent offenses, may use stolen identities to evade criminal background checks. This is especially common when applying for positions in healthcare, education, finance, or government contracting where certain criminal convictions may create statutory or regulatory disqualifications, or where employers conduct enhanced screening due to access to vulnerable populations or sensitive information.
Circumventing Immigration or Work Authorization Issues
Individuals lacking legal work authorization may use fraudulent identities to satisfy I-9 requirements. Stolen or counterfeit documents, combined with SSNs belonging to U.S. citizens, allow applicants to present facially compliant documentation while evading E-Verify detection in some cases.
Enabling Internal Theft or Fraud
Organized fraud rings or individuals planning theft, embezzlement, or data exfiltration may use false identities to obscure their involvement and complicate post-incident investigation. Roles with access to financial systems, customer data, or proprietary information are particularly vulnerable.
Evading Creditor Obligations or Judgment Liens
Some applicants use false identities to avoid wage garnishment, child support enforcement, or employment-based asset discovery. While not inherently dangerous, these individuals introduce payroll compliance complications and potential legal entanglements.
Organized Fraud Networks
Sophisticated groups may place operatives in targeted organizations to facilitate larger schemes such as identity theft rings, benefits fraud, or corporate espionage. These actors often possess high-quality counterfeit documents and rehearsed backstories.
How the Fraud Succeeds: Weaknesses in Standard Hiring Processes
Most employers rely on visual ID inspection, self-reported information, and background checks that assume accurate identity data. These practices contain exploitable gaps that allow identity theft job application fraud to succeed. The following vulnerabilities create opportunities for fraudulent applicants:
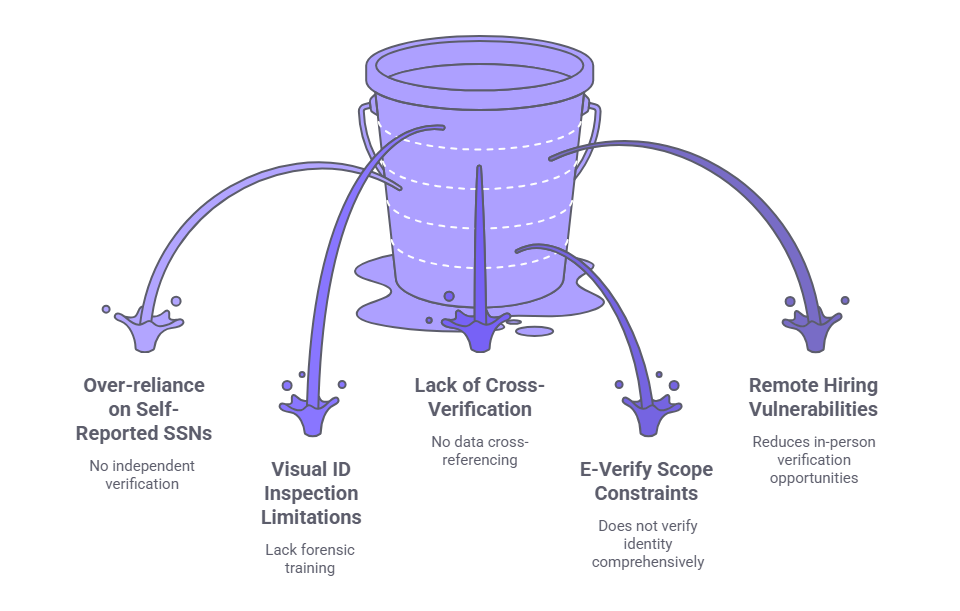
- Over-reliance on self-reported SSNs: Applicants typically provide SSNs on forms without independent verification, allowing fraudulent numbers to misdirect background checks entirely.
- Visual ID inspection limitations: HR personnel lack forensic training to detect high-quality counterfeits, confirming document appearance but not legitimate issuance.
- Lack of cross-verification: Standard workflows rarely cross-reference SSN issuance dates, address histories, or employment timelines against applicant-provided data.
- E-Verify scope constraints: The system confirms work authorization but does not verify identity comprehensively, potentially passing stolen SSNs belonging to work-authorized individuals.
- Remote hiring vulnerabilities: Virtual interviews and digital document submission reduce opportunities for in-person identity verification, enabling manipulation and proxy use.
Employers who understand these weaknesses can design verification protocols that address each gap proportionately based on role risk.
Consequences to Employers: Legal, Financial, and Reputational
When identity fraud succeeds, employers face cascading liabilities across multiple domains. The following table summarizes the primary consequence categories and their typical manifestations:
| Consequence Category | Specific Risks | Typical Impact |
| FCRA Compliance | Adverse action based on fraudulent identity data, improper authorization or notice procedures | Private lawsuits, regulatory enforcement, statutory damages |
| I-9 Penalties | Accepting fraudulent documents, failing verification protocols | ICE fines ranging from hundreds to thousands per violation |
| Payroll and Tax | SSN mismatches triggering no-match letters, W-2 reporting failures | Penalties, garnishment complications, unemployment claim issues |
| Negligent Hiring | Failure to conduct reasonable screening when employee under false identity causes harm | Civil liability for theft, violence, or tortious acts by fraudulent employee |
| Internal Theft | Employees operating under false identities steal cash, data, or IP | Investigation hindered by false trails, recovery unlikely |
| Reputation | Public disclosure of fraud cases, especially in regulated industries | Customer distrust, regulatory scrutiny, investor concern |
These consequences justify resource allocation for proportionate verification protocols aligned with role sensitivity and organizational risk tolerance.
FCRA Compliance Risks
If an employer takes adverse action based in whole or in part on information contained in a consumer report, FCRA requires pre-adverse action notice, a copy of the report, a summary of rights, reasonable opportunity to dispute, and final adverse action notice. When identity fraud is suspected, employers should consult legal counsel to determine whether adverse action procedures apply, as the analysis depends on whether the decision relies on consumer report data or independent identity verification findings.
Negligent Hiring Claims
If an employee hired under a false identity commits theft, violence, or other tortious acts, victims may allege negligent hiring if the employer failed to exercise reasonable care in screening and the employee's background (concealed by the false identity) indicated dangerous propensities relevant to the harm. Liability depends on whether reasonable verification would have revealed disqualifying information and whether the failure to discover that information proximately caused the injury.
Red Flags and Detection Indicators During Hiring
HR teams can monitor specific indicators without deploying specialized fraud detection tools. Recognizing these red flags enables timely escalation and additional verification before onboarding.
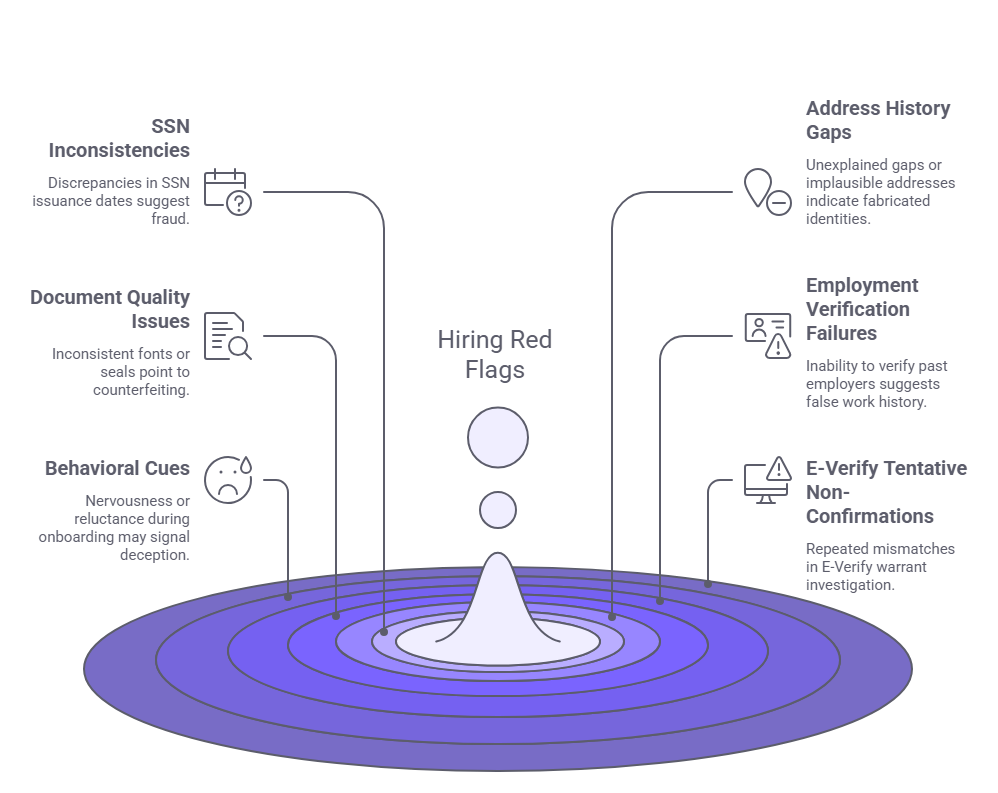
SSN Issuance Date Inconsistencies
Social Security Numbers are issued sequentially by geographic area and time period. If an applicant's stated age or claimed work history predates the SSN issuance range, fraud is likely. SSN validation tools can flag this without requiring credit checks.
Address History Gaps or Implausibilities
Applicants with no address history, extremely short tenures at multiple addresses, or addresses tied to mail drops or commercial entities may be using fabricated identities. Legitimate individuals typically have traceable residential histories that align with employment and education timelines.
Document Quality Issues
Inconsistent fonts, misaligned text, incorrect state seal formats, or low-resolution printing on identity documents suggest counterfeiting. While HR staff should not be expected to conduct forensic analysis, obvious anomalies warrant further verification.
Employment History Verification Failures
Inability to reach past employers, vague or evasive responses from listed references, or discrepancies between stated job titles and actual records may indicate fabricated work history built around a false identity.
Behavioral Cues During Onboarding
Nervousness when presenting identity documents, reluctance to provide additional verification, or inconsistencies in biographical details during casual conversation can signal deception. While not dispositive, these cues should prompt additional scrutiny rather than immediate disqualification. Employers should apply behavioral indicators consistently and recognize that nervousness or communication difficulties may result from language barriers, cultural differences, or legitimate interview anxiety rather than fraud. Subjective behavioral assessments should never be the sole basis for adverse action and must be corroborated by objective verification findings.
E-Verify Tentative Non-Confirmations
When E-Verify returns a mismatch between provided information and government records, applicants may claim clerical errors. While legitimate mismatches occur, patterns of TNCs across multiple hires or delayed resolution efforts warrant investigation.
Verification Mechanisms and Procedural Controls
Employers have access to several identity verification methods, each with specific capabilities and limitations. The following overview describes available mechanisms without endorsing specific vendors or technologies.
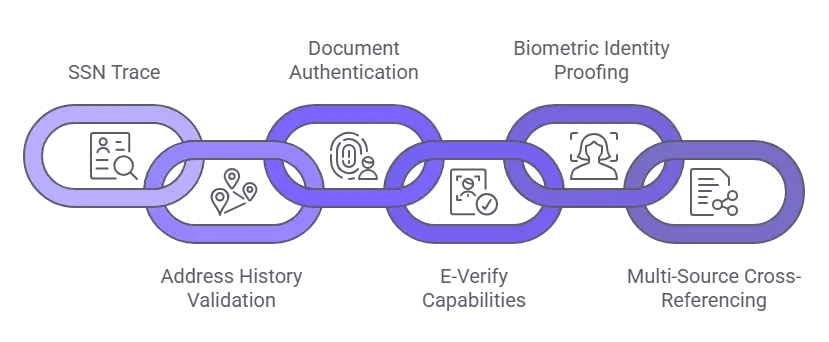
Social Security Number Trace
SSN traces query databases to retrieve names, addresses, and aliases associated with a given SSN. They reveal whether multiple names have been used with the same SSN, whether the number was issued before the applicant's stated birth year, or whether it falls within invalid ranges. However, SSN traces do not verify that the applicant is the legitimate SSN holder. They surface inconsistencies requiring further investigation rather than providing definitive identity confirmation. Because SSN trace data is drawn from credit headers and other databases that may contain errors or incomplete information, employers should corroborate trace findings with additional verification methods before taking adverse action.
Address History Validation
Credit header data and utility connection records provide address timelines that should align with applicant-provided information. Significant gaps, rapid relocation patterns, or addresses associated with fraud indicators such as mail drops or correctional facilities suggest potential issues. This method works best when combined with employment history verification.
Document Authentication Techniques
Advanced identity verification services use database queries, biometric analysis, or forensic document review to assess whether identity documents were legitimately issued. These services compare document features against known templates and may cross-reference presented information with aggregated databases or, in limited cases, issuing authority records where access is authorized. Employers should confirm the specific data sources and verification methods used by any third-party service.
E-Verify Capabilities and Limitations
E-Verify confirms work authorization by comparing Form I-9 data to SSA and DHS databases and may include photo matching for certain immigration documents. However, it does not comprehensively verify that the person presenting documents is the legitimate holder. A stolen SSN belonging to a work-authorized individual may pass E-Verify without triggering alerts. Employers should treat E-Verify as one component of identity verification rather than a comprehensive solution.
Biometric Identity Proofing
Some verification platforms use facial recognition, liveness detection, or document-to-selfie matching to confirm that the person submitting an application matches the photo on their identity document. These methods are most effective in remote hiring contexts where in-person verification is impractical. State biometric privacy laws may impose consent and data handling requirements.
Multi-Source Cross-Referencing
Comparing data from multiple independent sources such as credit headers, public records, employment databases, and professional licenses increases the likelihood of detecting fabricated identities. Synthetic identities often lack sufficient data depth to withstand multi-source validation, making this approach particularly effective against composite fraud schemes.
Legal and Compliance Framework Considerations
Fraud prevention measures must comply with employment screening regulations. The following framework highlights key legal requirements and constraints:
- FCRA permissible purpose and authorization: Identity verification tools that access consumer report data require FCRA-compliant authorization and adverse action procedures, including pre-adverse action notices if discrepancies lead to disqualification.
- I-9 document examination standards: Immigration and Nationality Act regulations require employers to accept documents that reasonably appear genuine and relate to the person presenting them. Employers may not demand additional or different documents based on citizenship status or national origin. However, employers also may not knowingly accept fraudulent documents. When fraud is suspected based on objective indicators, employers should consult legal counsel to determine whether additional verification is permissible and how to document concerns without violating anti-discrimination provisions.
- State privacy and biometric laws: States including Illinois, Texas, and Washington have enacted biometric privacy laws with differing requirements. For example, Illinois BIPA requires written consent, written data retention policies, and provides employees with a private right of action. Texas and Washington have different consent, notice, and enforcement mechanisms. Employers using facial recognition or fingerprint-based identity verification should review applicable state laws and consult legal counsel to ensure compliance with jurisdiction-specific requirements.
- Discrimination and disparate impact: Verification protocols must apply consistently based on objective role risk tiers rather than subjective assessments or demographic factors to avoid Title VII violations.
- State-specific identity verification requirements: Industries such as healthcare, childcare, and financial services may face additional state-mandated identity verification obligations beyond federal minimums.
Legal counsel should review verification protocols before implementation to ensure compliance with applicable federal, state, and local requirements.
Building a Proportionate Identity Verification Protocol
Employers should design verification processes that balance fraud risk against cost, efficiency, and legal compliance. Proportionality in this context means tailoring verification intensity to legitimate business needs (such as access to sensitive data or vulnerable populations), applicable regulatory requirements, and the principle that screening measures should be job-related and consistent with business necessity. The following table provides a framework for role-based risk tiering:
| Risk Tier | Role Characteristics | Recommended Verification |
| High Risk | Access to financial systems, customer PII, vulnerable populations, proprietary data, or regulatory requirements | SSN trace + address validation + document authentication + E-Verify + biometric proofing where appropriate |
| Moderate Risk | Limited system access, supervised work, indirect customer contact | SSN trace + E-Verify + address validation |
| Low Risk | No system access, direct supervision, minimal customer interaction, no regulated requirements | Standard I-9 procedures + basic background check |
Employers should document the rationale for each tier to demonstrate defensible, non-discriminatory decision-making.
Integrating Verification into Hiring Workflow
Conduct identity verification early in the hiring process, after conditional offer but before onboarding. This timing allows employers to address discrepancies without prematurely rejecting candidates while preserving FCRA adverse action rights. Verification should occur before issuing system access credentials or sharing sensitive information.
Training Hiring Managers on Red Flags
Equip interviewers and HR staff to recognize behavioral and documentary red flags without requiring forensic expertise. Training should emphasize escalation procedures rather than on-the-spot adjudication. Managers should understand that suspicion alone does not justify adverse action without documented verification findings and legal review.
Periodic Protocol Review
Fraud tactics evolve, as do legal requirements. Employers should review identity verification protocols annually or when regulatory changes, industry incidents, or audit findings indicate gaps. Continuous improvement ensures protocols remain effective and compliant.
Common Misconceptions and Practitioner Mistakes
Even diligent HR teams fall prey to assumptions that undermine fraud detection. Addressing these misconceptions improves protocol effectiveness.
Assuming Background Checks Verify Identity
Criminal background checks, employment verification, and education checks assume that the SSN and name provided are accurate. They do not independently confirm that the applicant is the person associated with those credentials. Identity verification must occur before or alongside background screening to detect fraud.
Over-Relying on Visual ID Inspection
HR personnel cannot reliably detect sophisticated counterfeits through visual inspection alone. Accepting a professional-looking driver's license without database cross-referencing provides minimal fraud protection, particularly against high-quality forgeries available through organized fraud networks.
Believing E-Verify Is Comprehensive Identity Verification
E-Verify confirms that SSN and immigration documents are valid for employment but does not verify that the applicant is the legitimate document holder. Stolen SSNs belonging to work-authorized individuals will pass E-Verify without triggering alerts, requiring supplemental verification for high-risk roles.
Failing to Update Protocols as Fraud Evolves
Techniques such as synthetic identity fraud and remote work impersonation have proliferated in recent years. Protocols designed for in-person, document-centric environments may not address digital and synthetic threats adequately. Regular protocol review prevents obsolescence.
Inconsistent Application of Verification Measures
Applying heightened scrutiny selectively based on interviewer intuition or applicant demographics invites discrimination claims. Role-based risk tiers provide objective, legally defensible justification for verification intensity. Consistent application protects both the organization and applicants.
Neglecting to Document Verification Steps
When identity fraud is discovered post-hire, employers must demonstrate that they followed reasonable, compliant verification procedures. Lack of documentation undermines defense against negligent hiring or I-9 violation claims. Proper recordkeeping supports both compliance and risk management objectives.
Conclusion
Identity theft in job applications represents a documented, evolving risk requiring proportionate verification measures aligned with role sensitivity and legal obligations. Employers who integrate SSN validation, address history analysis, and document authentication into risk-tiered hiring workflows reduce exposure to fraud-related liability, operational disruption, and reputational harm without incurring disproportionate costs or legal risk.
Frequently Asked Questions
What is identity theft in the context of job applications?
Identity theft job application fraud occurs when individuals use stolen Social Security Numbers, synthetic identities, or impersonation schemes to bypass employment screening. Unlike resume embellishment, it targets the foundational question of applicant identity, requiring verification methods that cross-reference data sources and validate documents against issuing authority records.
How do criminals obtain stolen identities for employment fraud?
Criminals acquire stolen identities through data breaches, phishing attacks, dark web marketplaces, or theft of physical documents. They may also create synthetic identities by combining real SSNs with fictitious names and birthdates, exploiting gaps in credit bureau and employment database coverage.
Can standard background checks detect identity theft in hiring?
Standard background checks assume the SSN and name provided are accurate. They do not independently verify identity. Detection requires SSN traces, address history validation, document authentication, or biometric verification conducted before or alongside criminal and employment history checks.
What are the legal consequences for employers who hire someone using a stolen identity?
Employers may face I-9 penalties from Immigration and Customs Enforcement, FCRA liability if adverse action procedures are mishandled, negligent hiring claims if the fraudulent employee causes harm, and payroll tax complications from SSN mismatches. Consequences vary based on whether the employer exercised reasonable verification procedures.
Does E-Verify prevent identity theft in employment?
E-Verify confirms work authorization by comparing Form I-9 data to SSA and DHS databases and may include photo matching for certain immigration documents. However, it does not comprehensively verify that the person presenting documents is the legitimate holder. A stolen SSN belonging to a work-authorized individual may pass E-Verify without triggering alerts. Employers should use E-Verify as one component of identity verification, supplemented by SSN traces and document authentication for higher-risk roles.
What red flags indicate possible identity fraud during hiring?
Red flags include SSN issuance dates inconsistent with applicant age, address history gaps or implausible patterns, document quality anomalies, employment verification failures, nervous or evasive behavior when presenting identity documents, and E-Verify tentative non-confirmations that remain unresolved.
How should employers balance fraud prevention with discrimination risk?
Employers should apply verification protocols consistently based on role risk tiers rather than subjective assessments or demographic factors. Objective criteria such as access to financial systems, customer data, or vulnerable populations justify heightened verification without creating disparate impact. Legal counsel should review protocols for compliance.
What is synthetic identity fraud in employment contexts?
Synthetic identity fraud involves creating fictitious personas by combining real and fabricated data, such as pairing a legitimate SSN with a false name and birthdate. These identities may lack sufficient credit or employment history to trigger immediate flags, requiring multi-source cross-referencing for detection.
Additional Resources
- Social Security Number Verification Service (SSNVS)
https://www.ssa.gov/employer/ssnv.htm - E-Verify Program Overview
https://www.e-verify.gov/ - Federal Trade Commission: Identity Theft
https://www.ftc.gov/news-events/topics/identity-theft - U.S. Citizenship and Immigration Services: Form I-9 Guidance
https://www.uscis.gov/i-9-central - Fair Credit Reporting Act Summary (FTC)
https://www.ftc.gov/legal-library/browse/statutes/fair-credit-reporting-act

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR professional at GCheck, specializing in background screening, fair hiring, and regulatory compliance. She holds from the Professional Background Screening Association (PBSA) and helps organizations navigate employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology, she translates policy into practice to build ethical, compliant, human-centered hiring systems that strengthen decision-making over time.