Reference check fraud represents a measurable procedural risk in hiring, where candidates manipulate verification processes through schemes ranging from peer impersonation to commercial fraud services. Effective mitigation requires understanding fraud methodologies and implementing multi-layered verification frameworks rather than relying solely on traditional phone-based reference checks.
Key Takeaways
- Reference check fraud exists on a sophistication spectrum, from informal friend impersonation to organized commercial services offering scripted fake references.
- Coached legitimate references involve candidates briefing actual former supervisors to emphasize specific qualities or omit unfavorable information.
- Fake company creation schemes use registered business entities, virtual offices, and functional phone systems to simulate legitimate employment history.
- VoIP-based impersonation allows fraudsters to route verification calls through spoofed numbers that appear connected to real organizations.
- Detection requires procedural controls such as independent contact validation, cross-referencing public records, and structured behavioral questioning.
- Most reference fraud succeeds not through sophisticated technology, but by exploiting predictable verification processes and time-constrained hiring workflows.
- Legal consequences for candidates typically involve offer rescission or termination rather than criminal prosecution, though negligent hiring liability affects employers.
- Risk-based verification approaches allow organizations to allocate enhanced scrutiny to roles with fiduciary responsibilities, safety-sensitive duties, or access to confidential information.
Understanding the Reference Fraud Landscape
Reference verification remains a standard component of employment screening, yet many organizations underestimate how frequently candidates attempt to manipulate this process. Research on resume and reference accuracy indicates that a meaningful percentage of candidates provide embellished or incomplete information during hiring processes, with reference manipulation representing one category of such misrepresentation. The actual prevalence varies significantly by industry, role level, and competitive pressure in specific talent markets. Unlike credential fraud or resume fabrication, reference check fraud often succeeds because verification procedures rely on candidate-provided contact information and follow predictable patterns that create exploitable vulnerabilities.
How Remote Work Changed Reference Verification
The rise of remote work since 2020 has complicated reference verification in two ways. First, the normalization of distributed teams means hiring professionals can no longer rely on informal network validation, where mutual professional connections might organically surface concerns about a candidate's background. Second, the proliferation of virtual business infrastructure has lowered the barrier to creating convincing fake employment history. These developments require organizations to reassess reference verification procedures that were designed for an era when employment relationships left more durable, independently verifiable traces.
Why Process Gaps Enable Most Fraud
Addressing reference fraud effectively begins with understanding that most schemes succeed through process gaps rather than technological sophistication. The majority of fraudulent references exploit predictable verification routines. Recognizing fraud as a procedural challenge rather than an intractable deception problem allows organizations to implement proportional countermeasures.
“Trust is part of hiring, but it should never replace verification.” Reading this statement made me think about how easy it is to make the hiring process routine instead of making it more meaningful. When the hiring process focuses more on the speed of the process than the actual content of the process, small gaps can quietly turn into real risks . It is a reminder that even simple steps like validating contacts or asking better questions can make a meaningful difference in how we assess people fairly and accurately.
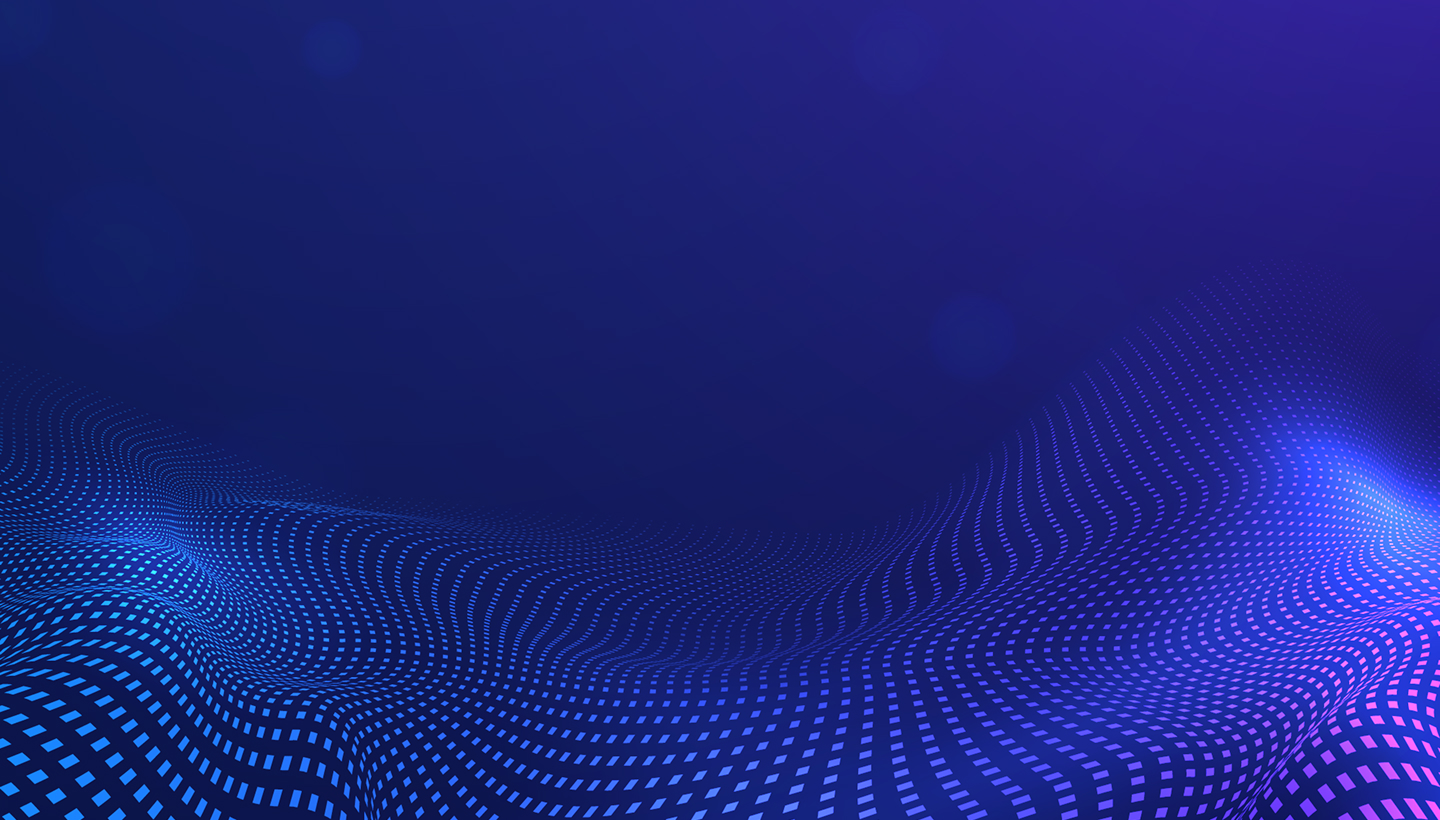
The Fraud Sophistication Spectrum
Reference check fraud operates along a continuum of complexity and resource investment. Understanding this spectrum matters because detection strategies and procedural controls must align with the sophistication level an organization is likely to encounter.
Fraud complexity levels include:
- Low sophistication: Friends or family members impersonate former supervisors with minimal preparation and no financial outlay
- Medium sophistication: Candidates create fake companies with registered business infrastructure or coach legitimate references to misrepresent employment details
- High sophistication: Commercial services provide comprehensive fraud infrastructure including staffed phone lines, fabricated documentation, and coached impersonators
- Hybrid sophistication: Multiple fraud methods combine to create layered deception resistant to standard detection approaches
Partial Truth Schemes
The middle range of this spectrum includes schemes where candidates leverage partial truths. A candidate might provide contact information for a legitimate former colleague who agrees to inflate the candidate's role and responsibilities, or coach an actual former supervisor to omit performance issues while emphasizing strengths. These hybrid approaches prove particularly difficult to detect because they combine verifiable elements with deliberate misrepresentation of the employment relationship's substance.
Risk-Based Resource Allocation
Organizations benefit from recognizing that fraud sophistication often correlates with the stakes involved. Candidates pursuing roles with significant compensation, autonomy, or access to sensitive systems face stronger incentives to invest in convincing deception. This risk-based perspective helps organizations allocate verification resources proportionally rather than applying uniform procedures across all hiring scenarios.
Seven Common Reference Fraud Schemes
Peer and Friend Impersonation
The most basic fraud scheme involves candidates providing contact information for friends, family members, or peers who agree to pose as former supervisors. This method requires no financial investment and minimal coordination. The impersonator answers calls from a personal phone number that the candidate has represented as belonging to a legitimate workplace contact.
Detection relies on identifying inconsistencies between the reference's claimed role and their demonstrated knowledge. Impersonators often struggle with detailed questions about organizational structure, industry-specific terminology, or the candidate's interaction with other departments. Verification calls that probe beyond scripted talking points frequently reveal gaps. Additionally, reverse phone number lookups may show the number belongs to a residential line or has no connection to the stated employer.
Coached Legitimate References
More sophisticated candidates maintain actual relationships with former colleagues or supervisors and explicitly coach these individuals on what to emphasize or omit during reference conversations. Unlike complete impersonation, the reference contact does have a legitimate connection to the candidate's employment history, making this scheme particularly difficult to detect through basic validation steps.
| Coaching Tactic | Purpose | Detection Challenge |
| Scripted talking points | Steer conversation toward specific competencies | Reference has authentic employment connection |
| Agreed narrative on termination | Characterize involuntary departure as resignation | Basic employment dates verify correctly |
| Role inflation | Exaggerate seniority or project contributions | Title may partially align with actual duties |
| Selective omission | Avoid discussing performance issues | Absence of negative information seems positive |
Detection requires structured questioning that explores multiple dimensions of the employment relationship. Behavioral questions that ask for specific examples prove more revealing than general assessments. References who consistently redirect toward prepared talking points or offer vague responses to concrete questions warrant additional scrutiny.
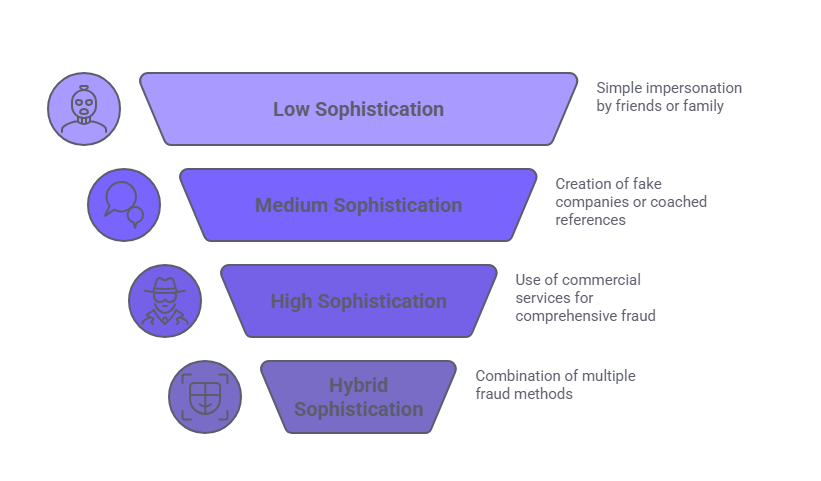
Fake Company Infrastructure
This scheme involves creating the appearance of a legitimate business entity to serve as a fabricated former employer. Candidates register LLCs or DBAs through state business filing systems, establish virtual office addresses, set up business phone lines, and sometimes create basic websites. When verification calls arrive, the candidate or an accomplice answers the business line and confirms the fabricated employment history.
The prevalence of legitimate virtual office services and the ease of business registration make this approach accessible to determined candidates. A few hundred dollars and several hours of administrative work can produce a fake employer with functional contact information, a professional-sounding voicemail system, and a minimal web presence.
Detection requires cross-referencing claimed employment against multiple sources:
- Business registration dates and formation documents
- Virtual office provider address databases
- Depth and age of online presence
- Evidence of actual business operations
- Employee profiles on professional networking platforms
- Industry directory listings and trade association memberships
Commercial Reference Services
Organized services sell fabricated references to candidates willing to pay fees typically ranging from modest amounts to several hundred dollars depending on service complexity. These operations employ staff who act as fake supervisors, maintain business phone lines and email addresses, and provide scripted responses to verification inquiries.
Commercial services operate with varying degrees of sophistication. Basic providers offer simple phone answering services where staff follow minimal scripts. Premium services conduct intake interviews with candidates to understand their claimed employment history in detail, enabling references to answer nuanced questions convincingly. Some maintain networks of fake companies across multiple industries and geographic regions, allowing candidates to select fabricated employers that align with their target roles.
VoIP and Digital Impersonation Infrastructure
Voice over IP technology enables sophisticated phone number spoofing that complicates verification efforts. Candidates can configure VoIP services to display caller ID information matching legitimate organizations, route incoming verification calls to personal devices while maintaining the appearance of calling from official business lines, and create complex call forwarding schemes that obscure the actual recipient's identity.
This technical capability allows candidates to provide phone numbers that appear to belong to legitimate employers when checked through standard reverse lookup services. When verification staff call these numbers, the candidate or an accomplice answers while the employer's name displays on caller ID, creating false confidence in the reference's legitimacy.
Detection requires verification approaches that do not rely exclusively on candidate-provided contact information. Independently locating employer phone numbers through corporate websites, business directories, or direct outreach to HR departments bypasses VoIP manipulation. Additionally, requests for video verification calls or documentation that must come from official company email domains introduce authentication layers that VoIP schemes cannot easily replicate.
Coordinated Multi-Reference Networks
Some candidates orchestrate networks of multiple individuals who provide corroborating fake references across different claimed employment periods. This scheme creates an appearance of consistency, as multiple references independently confirm overlapping details about the candidate's work history, competencies, and character. The coordination may involve friends, family members, or paid participants who have rehearsed their roles and align their stories.
The sophistication lies in creating a coherent narrative across references that withstands cross-checking. If one reference describes the candidate's role in a specific project, other references from the same claimed employer can corroborate that project's existence and the candidate's contributions.
Detection involves testing for excessive consistency that suggests rehearsal rather than authentic recollection. Legitimate references typically exhibit minor inconsistencies in details, recall events from different perspectives, and provide information colored by their specific working relationship with the candidate. References that align too precisely, use identical phrasing, or demonstrate improbable knowledge of aspects outside their claimed role may indicate coordination.
Hybrid Schemes Combining Multiple Methods
The most challenging fraud attempts combine elements from multiple schemes to create layered deception resistant to standard detection methods. A candidate might create a fake company with registered business infrastructure, employ a commercial service to staff the reference line, use VoIP technology to route calls appropriately, and coordinate with actual former colleagues who agree to confirm the fabricated employer's existence if contacted indirectly.
Hybrid approaches target the most common steps in the verification process. Business registration checks may reveal legitimate filings, creating the appearance of authenticity. Calls to the contact numbers provided often reach professional-sounding references prepared to validate the story. Even attempts at independent contact discovery can lead to coordinated parties who reinforce the same false narrative. Detecting hybrid fraud therefore requires multi-layered verification that evaluates several elements simultaneously and looks for patterns across data points rather than relying on any single validation method.
Detection Indicators and Red Flags
Effective fraud detection combines procedural controls with attention to behavioral and contextual anomalies. No single indicator proves fraud conclusively, but patterns of concerning signals warrant enhanced scrutiny.
| Red Flag Category | Specific Indicators | Verification Response |
| Availability patterns | Immediate answering regardless of time or day; no voicemail or call screening | Request callbacks to publicly listed numbers; note unusual accessibility |
| Response quality | Abstract assessments without specific examples; deflection from behavioral questions | Ask follow-up probes requiring concrete details; document vague responses |
| Information consistency | Discrepancies between reference statements and other data sources; title inflation inconsistent with org size | Cross-reference claims against LinkedIn, company records, industry norms |
| Digital footprint | Employer has minimal online presence; recently created website; no employee social profiles | Search business registries; check domain registration dates; verify operations |
| Contact verification | Phone traces to residential address; personal email domains; unverifiable business affiliation | Independently source employer contacts; request official email confirmation |
Unusual Availability Patterns
References who answer calls immediately regardless of time or day may indicate personal phones rather than business lines. Legitimate workplace contacts typically experience some call screening, voicemail, or delays reaching the appropriate person. References consistently available at unusual hours or who answer with generic greetings rather than company names merit additional validation.
Vague or Scripted Responses
Reluctance or inability to provide specific examples when asked behavioral questions suggests limited actual supervisory experience with the candidate. Authentic references typically recall concrete situations, even if details have faded. Responses that remain abstract, deflect toward general assessments, or rely heavily on prepared-sounding talking points may indicate coaching or impersonation.
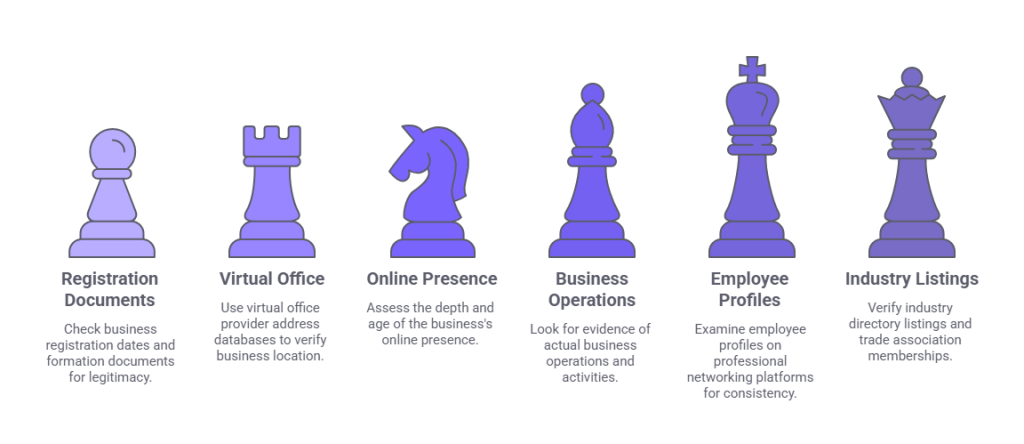
Procedural Vulnerabilities That Enable Fraud
Most reference fraud succeeds by exploiting common process shortcuts and time pressures in hiring workflows. Organizations that accept candidate-provided contact information without validation make fraud trivially easy. When verification consists solely of calling numbers the candidate supplied, any impersonation scheme can succeed as long as the fraudster answers the phone convincingly.
Common process vulnerabilities include:
- Accepting candidate-provided contact information without independent validation
- Relying exclusively on single communication channels such as phone or email
- Using templated questions that follow predictable patterns and allow scripted responses
- Conducting superficial verification under time pressure to fill positions quickly
- Failing to document verification processes or maintain audit trails
Single-Channel Verification Creates Risk
Single-channel verification creates vulnerability. Relying exclusively on phone calls or emails allows candidates to control the communication channel and prepare responses. Multi-channel approaches introduce friction that makes fraud more difficult and costly. Having more than one way of doing things allows an organization to verify information from different sources instead of relying on one source that could be altered. This eventually leads to more consistency and trust in verification.
Predictable Questions Enable Preparation
Templated questions that follow predictable patterns allow candidates to prepare references with scripted responses. When verification calls consistently ask the same questions in the same order, fraudulent references can rehearse answers that sound authentic. Varying question structure, asking open-ended behavioral questions that require detailed examples, and probing inconsistencies disrupt scripted responses and reveal gaps in legitimate knowledge.
Legal and Liability Considerations
Candidates who engage in reference fraud face potential consequences ranging from offer rescission to termination if discovered post-hire. In cases involving fabricated credentials for licensed positions, false statements on official documentation, or roles requiring specific legal qualifications, criminal charges under fraud or false statement statutes may apply in some jurisdictions, though prosecution for reference manipulation alone remains uncommon. When such discoveries result from consumer reports obtained through background screening services, employers must follow applicable Fair Credit Reporting Act adverse action notice requirements before rescinding offers or terminating employment.
Employer Liability Risks
Employers face legal exposure through negligent hiring claims when inadequate verification contributes to hiring individuals who later cause harm. If an employee with fabricated references commits theft, fraud, or causes injury to others, affected parties may argue the employer should have detected the fraudulent background through reasonable verification efforts.
| Legal Consideration | Employer Impact | Risk Mitigation Approach |
| Negligent hiring liability | Exposure when inadequate screening precedes employee misconduct causing harm | Document thorough verification procedures; calibrate rigor to role risk profile |
| Negligent retention | Liability when fraud discovered post-hire but not investigated or addressed | Establish clear policies for background discrepancies; document investigation decisions |
| Defamation concerns | Hesitation to provide or request substantive reference information | Understand qualified privilege protections for truthful, good-faith references |
| Privacy and employment law compliance | Violations when verification exceeds legal boundaries or lacks proper authorization | Consult legal counsel on jurisdiction-specific requirements and permissible inquiries |
Jurisdictional Compliance Requirements
Organizations should consult legal counsel when developing reference verification procedures to ensure compliance with relevant employment laws, privacy regulations, and industry-specific requirements. Reference check practices are subject to significant state, municipal, and industry-specific variation. Some jurisdictions limit permissible reference questions, impose specific disclosure or authorization requirements, restrict consideration of certain background information categories, or require individualized assessment before adverse decisions. Verification procedures must account for the specific legal requirements applicable to each hiring location and candidate jurisdiction.
Building a Multi-Layered Verification Framework
Effective reference fraud prevention requires defense in depth, combining multiple validation methods that create cumulative barriers to successful deception. No single approach proves foolproof, but layered controls significantly increase the effort, cost, and skill required to execute fraud successfully.
Independent Contact Validation
Independent contact validation forms the foundation. Rather than calling candidate-provided numbers, verification staff should independently locate employer contact information through corporate websites, business directories, or direct outreach to HR departments. This bypasses impersonation schemes that rely on controlling the communication channel.
Core Verification Layers
Essential verification components include:
- Independent contact sourcing: Locate employer information through corporate websites, business directories, and HR departments rather than candidate-provided contacts
- Multi-source cross-referencing: Verify employment claims using employment verification methods authorized by the candidate and permitted under applicable law, checking business registration databases, professional licenses, and networking platforms
- Structured behavioral interviewing: Ask references to describe specific situations requiring detailed responses difficult to fabricate
- Authentication documentation: Request written confirmation from official company email addresses or on corporate letterhead
- Professional verification services: Employ specialized investigators for high-stakes roles with fiduciary or safety-sensitive responsibilities
Cross-referencing employment claims against multiple data sources builds verification confidence. Verifying business registration and operational history for claimed employers, reviewing the candidate's professional network connections for alignment with stated work history, and examining industry-specific credentials or licenses all contribute validation layers. Discrepancies between these sources and candidate claims warrant investigation.
Behavioral Interview Techniques
Structured behavioral interviewing of references produces richer information than templated questions. Asking references to describe specific situations where the candidate demonstrated key competencies, handled challenges, or interacted with colleagues generates detailed responses that prove difficult for impersonators to fabricate convincingly.
Using Professional Services Compliantly
Professional employment verification services, including Consumer Reporting Agencies subject to the Fair Credit Reporting Act, offer specialized capabilities for high-stakes hiring scenarios. Organizations using such services must ensure compliance with applicable FCRA requirements including proper authorization, permissible purpose limitations, and adverse action notice procedures. When used appropriately for roles with significant fiduciary responsibilities or access to sensitive systems, and in compliance with applicable legal requirements such as the FCRA, professional services provide an additional verification layer.
Risk-Based Verification Approaches
Organizations benefit from calibrating verification rigor to role-specific risk profiles rather than applying uniform procedures across all positions. Entry-level roles with limited autonomy, minimal access to confidential information, and close supervision may warrant standard reference verification focused on basic employment confirmation and general performance assessment. Enhanced verification becomes appropriate as roles increase in responsibility, authority, and potential organizational impact.
| Role Risk Category | Risk Factors | Appropriate Verification Level |
| Fiduciary positions | Financial authority; asset access; control over organizational or client funds | Enhanced verification including credential validation, professional reference services, multi-source cross-referencing |
| Safety-sensitive roles | Patient care responsibilities; commercial vehicle operation; work with vulnerable populations | Thorough employment history validation; detailed behavioral reference interviews; license verification |
| Confidential access roles | Administrative system access; proprietary information handling; personal data responsibilities | Comprehensive verification with independent contact validation; document authentication; insider threat assessment |
| Executive leadership | Organizational impact of hiring errors; reputational consequences; strategic decision authority | Full due diligence including professional search firm involvement; extensive reference networks; public record review |
| Standard positions | Entry-level roles; close supervision; limited autonomous authority | Basic employment confirmation; standard reference verification with spot validation |
High-Stakes Role Categories
Fiduciary positions involving financial authority, access to organizational assets, or responsibility for others' funds justify enhanced verification. Roles such as financial controllers, accounts payable managers, or treasury staff require thorough validation of employment history, professional credentials, and reference authenticity.
Safety-sensitive positions where employee actions directly affect public safety or the well-being of vulnerable populations warrant enhanced scrutiny. Healthcare roles with patient care responsibilities, transportation positions involving operation of commercial vehicles, and positions working with children or elderly populations all carry elevated verification requirements.
When to Escalate Verification
Red flags emerging during the hiring process should trigger verification escalation. Inconsistencies between resume information and interview responses, gaps in employment history that lack convincing explanation, reluctance to provide references from specific employment periods, or behavioral indicators of dishonesty during interviews all warrant enhanced verification attention.
Common Misconceptions About Reference Fraud
Many hiring professionals assume reference fraud primarily involves overtly dishonest candidates with fabricated work histories. In reality, reference manipulation often involves candidates with legitimate employment experience who coach references to emphasize specific qualities, omit unfavorable information, or mischaracterize the circumstances of their departure. This gray area between outright fraud and strategic impression management proves particularly challenging to detect and assess.
Persistent misconceptions include:
- Only dishonest candidates commit fraud: Many otherwise qualified candidates make poor decisions under competitive hiring pressure or when facing employment gaps
- References serve as formality: Treating reference checks as pro forma exercises rather than substantive verification enables manipulation
- Technology fully automates detection: AI tools assist with data validation but cannot replace human judgment in behavioral assessment and contextual interpretation
- Only major misconduct motivates fraud: Career gaps, layoffs, or personality conflicts can drive reference manipulation even among capable candidates
The belief that references serve primarily as formality rather than substantive verification contributes to inadequate fraud detection. When organizations treat reference checks as pro forma exercises that rarely surface disqualifying information, verification becomes superficial and easily manipulated.
Some organizations assume technology solutions, particularly AI-powered verification tools, can fully automate fraud detection. While technology assists with certain validation tasks, human judgment remains essential for interpreting behavioral cues, assessing contextual factors, and conducting nuanced follow-up investigation.
Conclusion
Reference check fraud represents a procedural challenge with practical solutions rather than an insurmountable deception threat. Organizations that implement multi-layered verification frameworks, calibrate scrutiny to role-specific risk profiles, and address process vulnerabilities that enable manipulation can effectively detect and deter most fraud schemes. Success requires treating reference verification as a substantive risk management function rather than administrative formality.
Frequently Asked Questions
How common is reference check fraud in employment screening?
Research on resume and reference accuracy indicates that a meaningful percentage of candidates provide embellished or incomplete information during hiring processes, with reference manipulation representing one category of such misrepresentation. The actual prevalence varies significantly by industry, role level, and competitive pressure in specific talent markets. Organizations conducting thorough verification with multiple validation layers detect concerning discrepancies in a meaningful minority of reference checks.
Can employers face legal consequences for failing to detect reference fraud?
Employers may face negligent hiring liability when inadequate screening contributes to hiring individuals who subsequently cause foreseeable harm. While reference fraud alone does not create liability, failure to conduct reasonable verification combined with subsequent employee misconduct can expose organizations to claims. Legal risk increases in roles involving fiduciary responsibilities, safety-sensitive duties, or access to vulnerable populations where thorough background verification constitutes standard practice.
What are the most reliable methods for detecting coached references?
Structured behavioral questions requiring specific examples prove most effective at revealing coached references. Authentic references typically provide detailed situation descriptions, acknowledge both strengths and development areas, and demonstrate genuine familiarity with the candidate's work. Coached references often deflect toward general assessments, struggle with follow-up questions probing specifics, and exhibit excessive consistency suggesting rehearsal.
Do commercial reference fraud services operate legally?
Commercial services providing fabricated references exist in legal gray areas. While facilitating employment fraud violates laws in many jurisdictions, services often position their offerings as coaching or verification assistance without explicitly acknowledging fraudulent intent. Candidates using such services face offer rescission, termination, and potential fraud charges if discovered.
How can employers independently verify reference contact information?
Independent verification involves locating employer contact information through sources other than the candidate. Corporate websites, business directories, professional licensing boards, and direct outreach to organizational HR departments provide authentic contact channels. For smaller employers, professional networking platforms may help identify legitimate current employees who can facilitate proper reference connections.
Should employers conduct reference checks for all positions?
Risk-based approaches allocate verification resources proportionally. Entry-level positions with close supervision may warrant basic employment confirmation. Roles with fiduciary responsibilities, safety-sensitive duties, access to confidential information, or significant autonomy justify enhanced verification including thorough reference fraud detection.
What should employers do if they discover reference fraud after hiring?
Discovery of post-hire reference fraud requires documented investigation and consultation with legal counsel and HR leadership. Responses typically range from termination for material misrepresentation to allowing the employee opportunity to provide legitimate references, depending on the fraud's nature and the employee's subsequent performance. Organizations should follow consistent policies regarding background discrepancies and maintain thorough documentation of investigation processes.
Can technology fully automate reference fraud detection?
Technology assists with specific validation tasks such as cross-referencing data, identifying phone number anomalies, and flagging inconsistencies, but cannot fully replace human judgment. Behavioral assessment, contextual interpretation, and nuanced follow-up investigation require human expertise. Effective fraud detection combines technological tools with trained verification professionals who understand manipulation schemes and apply layered validation approaches.
Additional Resources
- EEOC Guidance on Background Checks and Employment Decisions
https://www.eeoc.gov/laws/guidance/background-checks-and-employment-decisions - Federal Trade Commission: Using Consumer Reports for Employment Purposes
https://www.ftc.gov/business-guidance/resources/using-consumer-reports-employment-purposes - Society for Human Resource Management: Reference Checking Best Practices
https://www.shrm.org/resourcesandtools/tools-and-samples/how-to-guides/pages/conductreferencechecks.aspx - U.S. Department of Labor: Background Checks and Credit Reports
https://www.dol.gov/general/topic/hiring/background

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications through the Professional Background Screening Association (PBSA) and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.