Conducting a background check for remote contractors working internationally requires a risk-based approach that accounts for jurisdictional limitations, data availability gaps, and worker classification rules. Traditional employment screening models often fail when applied to digital nomads and overseas independent contractors, requiring HR teams to implement verification frameworks aligned with role risk and regulatory exposure.
Key Takeaways
- A background check for remote contractors differs fundamentally from employee screening due to classification boundaries, jurisdiction, and data access constraints.
- Digital nomads, remote employees, and overseas contractors each trigger distinct legal obligations and verification capabilities.
- Traditional background checks often fail for international freelancers due to address instability, limited U.S. record availability, and multi-jurisdictional complexity.
- Verification capabilities vary significantly by country, with formal criminal, employment, and education records often inaccessible or unreliable.
- Risk-based frameworks align verification intensity with role access level, contract value, and data sensitivity rather than applying uniform standards.
- International freelancer verification methods include identity validation, credential checks, and structured reference protocols when formal records are unavailable.
- Data privacy laws including GDPR and international equivalents impose strict consent, storage, and cross-border transfer requirements on contractor screening.
- Worker misclassification and inadequate documentation create both legal and operational risk during the verification process.
Understanding Worker Classification and Screening Obligations
Effective screening begins with clarity about who you are hiring and what verification authority applies. The terms "digital nomad," "remote employee," and "overseas contractor" are often used interchangeably. However, each classification triggers different legal frameworks and screening capabilities.
Digital Nomads vs. Remote Employees vs. Overseas Contractors
A remote employee maintains an employment relationship governed by labor laws. These laws apply in the employer's jurisdiction, the worker's location, or both. Employers conducting a background check for remote contractors must distinguish this relationship from independent contractor arrangements. In contractor arrangements, the engagement is contractual rather than employment-based.
Digital nomads represent a subset of remote workers who move frequently across borders. They often work as contractors while residing temporarily in multiple countries. Classification determines permissible verification scope.
Employment relationships trigger obligations under the Fair Credit Reporting Act when an employer obtains a consumer report from a consumer reporting agency for employment purposes. The FCRA defines employment purposes as one of several permissible purposes for obtaining consumer reports. It imposes specific disclosure, authorization, and adverse action requirements. When FCRA applies to employee screening, employers must follow pre-adverse action and final adverse action notice requirements. These requirements apply before taking adverse employment actions based on consumer report information.
Contractor relationships generally fall outside FCRA requirements. However, they remain subject to contract law, data privacy regulations, and industry-specific due diligence standards.
Misclassification Risks in Screening
Misclassification creates both legal and operational risk. Factors indicating employment status include behavioral control, financial control, and the relationship type as understood by both parties. These factors are analyzed under IRS guidelines and relevant state law tests.
The nature and extent of screening requirements may themselves be considered in misclassification analysis. Extensive employment-style verification can suggest greater employer control. Treating a contractor as an employee for screening purposes may suggest employment status. This exposes the organization to tax withholding obligations, benefits claims, or labor law violations.
Conversely, under-screening based on contractor status may leave gaps in risk mitigation. This occurs when the individual has access equivalent to an employee. State and local ban-the-box laws that delay criminal history inquiries typically apply only to employees, not independent contractors. However, organizations should verify whether specific ordinances in their jurisdiction or the candidate's location define coverage more broadly.
Why Worker Location and Mobility Matter
Digital nomads present unique verification challenges due to location instability and multi-jurisdictional exposure. A contractor may reside in Thailand, hold citizenship in Canada, and work for a U.S.-based company while traveling through Europe. Each jurisdiction may apply different data protection rules, limit access to background records, or impose specific consent requirements.
| Verification Challenge | Impact on Screening Process |
| Frequent location changes | Address history becomes difficult to verify |
| Virtual business addresses | Traditional residence verification methods fail |
| Multi-jurisdictional exposure | Multiple privacy law frameworks apply simultaneously |
| Cross-border tax implications | Permanent establishment and nexus risks increase |
Employment and education verification may require outreach to institutions across multiple countries. These countries have varying response protocols, language barriers, and authentication standards. Tax nexus and compliance risk also increase with worker mobility. Employers may inadvertently create permanent establishment exposure in jurisdictions where contractors perform work. This risk is particularly high if the individual represents the company to local clients or maintains a prolonged presence.
Why Traditional Background Checks Fail for International Contractors
Conventional employment screening models rely on centralized record systems, stable residential history, and jurisdiction-specific legal frameworks. These elements often do not exist or apply when conducting a background check for remote contractors working internationally.
Data Availability and Access Barriers
Criminal record databases vary widely by country. The United States maintains decentralized court records accessible at county, state, and federal levels. However, many countries restrict access to criminal history data, limit inquiries to government entities, or prohibit disclosure entirely.
Some jurisdictions provide records only to the individual subject. This requires the contractor to obtain and submit their own documentation. Employment and education verification face similar obstacles. Institutions in some countries do not respond to third-party inquiries, require notarized authorization, or charge fees that make verification cost-prohibitive relative to contract value.
Credit history data maintained by U.S. consumer reporting agencies is generally unavailable for individuals without U.S. credit activity. While some consumer reporting agencies operate internationally, cross-border access to credit files for screening purposes is typically restricted.
Jurisdictional and Legal Limitations
Data privacy laws impose strict requirements on cross-border data transfers. The General Data Protection Regulation in the European Union restricts transfers of personal data to countries without adequate protection frameworks unless specific safeguards are implemented.
Similar laws in the United Kingdom, Canada, Brazil, and other jurisdictions require explicit consent, purpose limitation, and data minimization when processing contractor information. Under GDPR and similar frameworks, consent may not be considered freely given when there is a significant imbalance between the parties.
Organizations should evaluate whether data processing is necessary for contract performance or justified by legitimate interests that do not override the contractor's rights. This approach is preferable to relying solely on consent.
Operational Challenges with Mobile Workforces
Digital nomads often lack the documentation traditional verification processes require. Without stable address history, long-term landlord references, or continuous employment with verifiable employers, standard identity confirmation and background checks yield incomplete results.
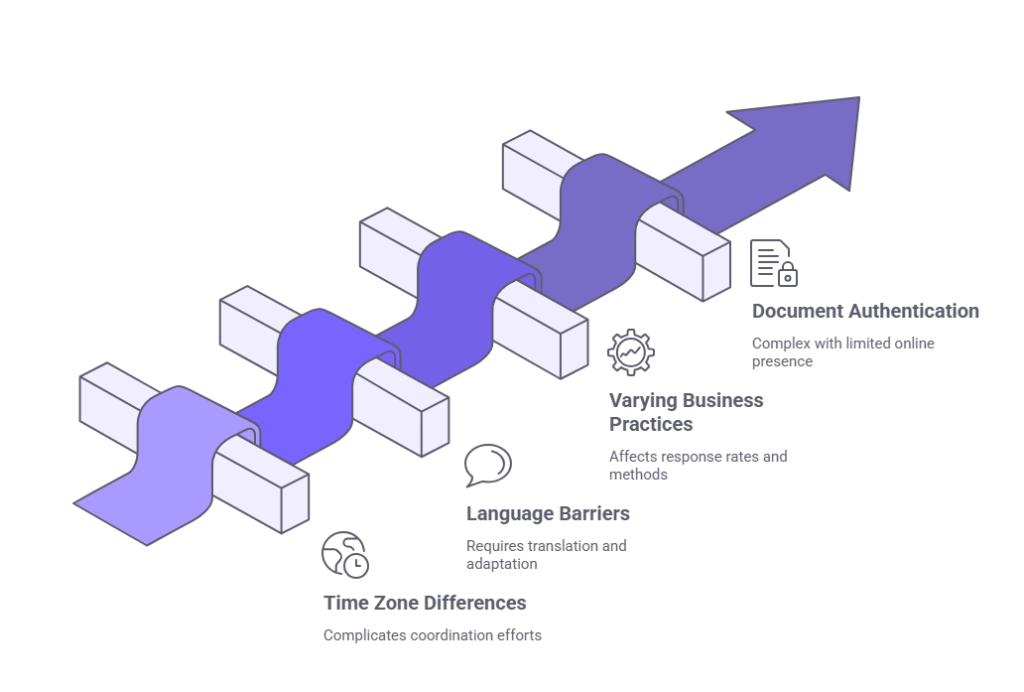
- Time zone differences complicate coordination with references and institutions
- Language barriers require translation services and cultural adaptation
- Varying business practices across countries affect response rates and verification methods
- Document authentication becomes complex with limited institutional online presence
These operational hurdles necessitate alternative verification approaches aligned with realistic data availability.
What You Can and Cannot Verify Across Borders
Understanding realistic verification capabilities prevents over-reliance on unavailable data. It also supports accurate risk assessment when conducting a background check for remote contractors in international contexts.
Identity and Credential Validation
Identity verification for international freelancers typically relies on government-issued identification documents. These include passports, national identity cards, or driver's licenses. Document verification services can authenticate security features, match biometric data, and detect common forgery indicators. However, they cannot confirm that the individual presenting the document is its rightful holder without additional steps.
Liveness detection and biometric matching technologies compare live video or photos to identification documents. This reduces impersonation risk. Biometric data is classified as sensitive under GDPR and similar frameworks. It requires explicit consent or specific legal authorization.
Organizations using biometric verification should ensure compliance with applicable regulations. This includes state biometric privacy laws such as the Illinois Biometric Information Privacy Act where relevant. Right-to-work verification presents jurisdictional complexity. U.S. employers must complete Form I-9 for employees but generally have no obligation to verify contractor work authorization. International contractors working remotely from their home countries typically do not require work authorization in the employer's jurisdiction. However, tax and immigration rules vary.
Criminal and Court Records
Access to criminal history depends entirely on the jurisdiction where records originated. Some countries provide centralized national criminal record checks to authorized requesters. Others restrict access to law enforcement or judicial authorities.
Many countries restrict or prohibit private-sector access to criminal records. Additionally, some U.S. state and local jurisdictions impose limitations on when and how criminal history information may be requested or considered. These limitations apply regardless of how the information is obtained.
Employers cannot assume that absence of U.S. criminal records indicates a clean background. This assumption fails for contractors who have never resided in or been subject to U.S. jurisdiction.
| Record Type | Typical International Availability |
| Criminal convictions | Restricted or prohibited in most countries |
| Arrest records | Generally inaccessible outside the United States |
| Court judgments | Varies widely, often requires direct institutional contact |
| Spent convictions | Subject to rehabilitation periods and automatic expungement |
Arrest records are generally inaccessible or prohibited for use in jurisdictions outside the United States. Lookback periods and spent conviction rules vary significantly by jurisdiction. Some countries limit disclosure timeframes or automatically expunge certain convictions after rehabilitation periods. Within the United States, state laws such as California's Civil Code Section 1786.18 and various local ordinances also impose lookback limitations and use restrictions that must be observed.
Employment and Education History
Employment verification for overseas independent contractors often depends on the contractor providing contact information and authorization for former clients or employers. Reference checks replace formal employment verification in many cases. Non-U.S. companies may not respond to third-party inquiries or maintain centralized HR verification systems.
Education credential verification requires outreach to issuing institutions. These institutions may not respond to international inquiries, charge prohibitive fees, or lack verification infrastructure. Professional licenses and certifications can often be verified through issuing bodies or public registries. However, requirements and accessibility vary widely.
Legal and Compliance Considerations by Worker Classification
Legal obligations when conducting a background check for remote contractors depend on the nature of the relationship, jurisdictions involved, and applicable regulatory frameworks.
Independent Contractor vs. Employee Distinctions
Misclassification risk increases when screening processes mirror employee background checks. Contractors generally have greater autonomy in determining what information they provide. Contract terms can specify verification requirements with demonstrated legitimate business need and proportionality.
The determination of whether a worker is an employee or contractor for FCRA purposes depends on the actual nature of the relationship. It does not depend on labels used by the parties. Treating contractors as employees for FCRA compliance purposes may create unintended obligations and risks. Failing to comply with FCRA when the relationship is actually employment creates liability exposure. Legal guidance should be sought when uncertainty exists.
Data Privacy and Cross-Border Data Transfers
GDPR and equivalent international privacy laws impose strict requirements on processing contractor personal data. Lawful bases for processing include contractual necessity, legitimate interest, or explicit consent.
Data minimization requires limiting collection to information directly relevant to the contract relationship. Cross-border data transfers from the European Union, United Kingdom, and other jurisdictions with comprehensive privacy laws require specific safeguards. These include standard contractual clauses, binding corporate rules, or adequacy determinations.
Organizations transferring data from the EU to the United States may also rely on the EU-U.S. Data Privacy Framework if they complete certification requirements. Retention limits apply to screening data under most privacy frameworks. Organizations should establish documented retention periods based on legal requirements, legitimate business needs such as contract duration and dispute resolution timeframes, and applicable statutes of limitations. Data deletion procedures should be implemented when retention periods expire.
Industry-Specific and Contractual Due Diligence Standards
Certain industries impose baseline verification requirements regardless of worker classification:
- Financial services organizations often mandate sanctions screening and background verification
- Healthcare entities require credential validation and licensing verification
- Government contractors must meet specific eligibility and clearance requirements
- Regulated industries face audit and compliance documentation obligations
Client contracts frequently specify due diligence standards for subcontractors. These requirements may flow down to independent contractors performing covered work.
Risk-Based Screening Framework for Remote Contractors
Effective verification aligns intensity and scope with actual exposure. It avoids applying uniform standards regardless of role requirements or risk factors.
Assessing Role Risk and Access Level
Role-based risk assessment evaluates what the contractor may access, control, or influence. High-risk roles involve financial authority, access to sensitive personal or proprietary data, system administration privileges, or representation of the organization to clients or regulators. Low-risk roles involve discrete deliverables with limited organizational access and minimal data exposure.
| Risk Level | Access Characteristics | Recommended Verification |
| High | Financial systems, sensitive data, client representation | Identity verification, credential validation, reference checks, jurisdiction-appropriate records |
| Moderate | Limited data access, internal collaboration, standard deliverables | Identity verification, credential validation, reference checks |
| Low | Public-facing work, no system access, discrete projects | Identity confirmation, basic credential validation |
A background check for remote contractors in high-risk categories should include identity verification, relevant credential validation, reference checks, and jurisdiction-appropriate records searches. Low-risk engagements may require only identity confirmation and basic credential validation. Additional checks may be triggered by red flags or contract expansion.
Client representation should be risk-assessed based on the nature of interaction, authority level, and potential organizational liability. Not all client-facing roles warrant high-risk classification.
Building Tiered Verification Protocols
Tiered frameworks establish baseline, standard, and enhanced verification levels based on role risk classification. Baseline verification applies to all contractors. It typically includes identity confirmation, sanctions screening, and contractual right-to-audit provisions.
Standard verification adds credential validation and reference checks for moderate-risk roles. Enhanced verification incorporates all available jurisdiction-appropriate background searches for high-risk positions. Clear documentation of tier criteria and required checks supports consistent application and defensibility.
Escalation triggers such as credential discrepancies, reference concerns, or unusual gaps in work history warrant additional investigation. These triggers apply regardless of initial tier assignment.
Balancing Cost and Risk Exposure
Verification costs must be proportional to contract value and risk exposure. Incremental verification allows phased due diligence as the relationship develops. Initial engagements involve baseline verification. Enhanced checks are triggered by contract extension, scope expansion, or access increases.
This approach manages upfront costs while maintaining risk alignment. Organizations should evaluate the total cost of verification against potential exposure from contractor-related incidents.
Practical Verification Methods When Formal Records Are Unavailable
When traditional screening data is inaccessible, alternative methods support risk mitigation. These methods respect legal and practical constraints on conducting a background check for remote contractors.
Structured Reference and Portfolio Validation
Reference checks provide valuable insight when formal employment or criminal records are unavailable:
- Use structured protocols with consistent questions across all contractors
- Document all responses and verification attempts
- Contact multiple reference sources to corroborate information
- Independently verify reference legitimacy through institutional channels
Portfolio and work sample validation confirms claimed experience and capabilities. Reviewing completed projects, client testimonials, and publicly available work product corroborates contractor representations. For technical roles, skills assessments or test projects provide direct evaluation of competency.
Identity Validation and Document Authentication
Government-issued identification verification forms the foundation of international freelancer verification. Document authentication services evaluate security features, detect tampering, and confirm document validity.
Multi-step verification requiring both document submission and live biometric comparison reduces impersonation risk. Video interviews and live interaction provide behavioral assessment opportunities and identity confirmation. While not a substitute for formal verification, real-time conversation allows evaluation of communication skills, professionalism, and consistency with written representations.
Ongoing Monitoring and Audit Rights
Contractual audit rights reserve authority to conduct additional verification if circumstances change or concerns arise. Right-to-audit clauses should specify scope, notice requirements, and contractor cooperation obligations.
Periodic re-verification for long-term contracts ensures continued alignment with qualification requirements. Adverse media and watchlist monitoring services provide ongoing alerts for criminal charges, regulatory actions, or sanctions designations. The frequency of re-verification should align with contract duration and role risk level.
Common Pitfalls in Digital Nomad and International Contractor Screening
Awareness of frequent mistakes supports more effective risk management when conducting a background check for remote contractors across borders.
Over-Reliance on Self-Reported Information
Accepting contractor representations without independent verification creates fraud exposure. Credential misrepresentation, fabricated work history, and false identity claims occur with sufficient frequency to warrant basic validation even for low-risk roles.
Unverified references provided by contractors may be friends or family rather than legitimate professional contacts. Best practices include independently locating reference contact information through institutional channels or publicly available sources.
Relying on unverified self-disclosure questionnaires about criminal history, education, or employment creates accuracy and legal risk. Self-reported information should be independently validated through appropriate verification methods aligned with role requirements.
Ignoring Data Protection and Privacy Requirements
Collecting screening data without proper legal basis violates privacy laws in many jurisdictions:

- Document contractual necessity or legitimate interest before collecting data
- Ensure data collection scope is proportional to specific role risks
- Provide clear privacy notices before beginning data collection
- Implement appropriate security measures for personal data storage
- Establish and follow documented retention and deletion procedures
Contractors must be informed what data will be collected, how it will be used, where it will be stored, and how long it will be retained. This information must be provided before data collection begins.
Inadequate data security for screening records creates breach liability and regulatory risk. Personal data collected during verification must be protected with appropriate technical and organizational measures, access controls, and encryption.
Applying Employee Screening Standards to Contractor Relationships
Treating contractors as employees for screening purposes creates misclassification risk. It may also exceed legitimate verification authority. The scope and nature of verification should reflect the contractual relationship, level of control, and actual risk exposure. It should not mirror employee protocols by default.
Using consumer reports from U.S. consumer reporting agencies for contractor screening may violate FCRA if the report is obtained for employment purposes. Organizations should evaluate the actual nature of the relationship and seek legal guidance when classification uncertainty exists.
Internal Policy Considerations for Scalable Contractor Verification
Sustainable screening programs require clear policies, consistent processes, and adequate documentation. These elements support growth and maintain defensibility.
Documented Risk Tiers and Verification Standards
Written policies specifying verification requirements by role category provide consistency and reduce discrimination risk. Criteria should be objective, job-related, and consistently applied regardless of contractor nationality, location, or other protected characteristics.
| Policy Element | Purpose | Implementation Requirement |
| Risk tier definitions | Classify roles by access and exposure | Objective criteria documented in writing |
| Verification standards | Specify checks required for each tier | Clear procedures with step-by-step guidance |
| Approval authorities | Designate decision-making responsibility | Defined authority levels and escalation paths |
| Exception processes | Handle non-standard situations | Documented justification and compensating controls |
Approval authorities and exception processes should be clearly defined. Exception documentation should include business justification and compensating controls.
Audit Trail and Records Management
Comprehensive documentation of verification activities, findings, and decisions supports audit readiness. It also provides defensibility in disputes. Records should include verification requests sent, responses received, dates of contact, individuals consulted, and basis for conclusions.
Centralized records management ensures consistent retention, security, and accessibility. It also prevents scattered records across multiple systems. Designated systems or repositories with appropriate access controls support compliance and facilitate periodic internal audits of contractor verification practices.
Consistency and Anti-Discrimination Safeguards
Objective criteria applied consistently across all contractors reduce discrimination liability. Verification requirements based on role risk rather than contractor characteristics avoid disparate treatment.
Documentation of business necessity and job-relatedness for all verification requirements supports legal defensibility. Each element of the screening process should have a documented connection to specific risks associated with the role. Regular review of verification outcomes by contractor demographics identifies potential disparate impact requiring remediation.
When to Escalate to Specialized Providers vs. In-House Due Diligence
Determining when to leverage external verification expertise versus internal capabilities depends on complexity, risk level, volume, and available resources.
Internal Capability Assessment
In-house verification is most effective for routine, high-volume checks with established processes:
- Reference checks with structured protocols and documentation
- Basic credential validation through institutional contact
- Sanctions screening using publicly available government databases
- Social media and professional presence reviews
Organizations conducting frequent international freelancer verification benefit from internal expertise development. However, this requires investment in training, technology, and quality assurance. Legal and compliance expertise availability affects in-house feasibility. Organizations with employment counsel or data privacy expertise can navigate complex multi-jurisdictional requirements more effectively than those lacking specialized support.
When External Providers Add Value
Complex international searches requiring local language capabilities, in-country contacts, or specialized record access typically warrant external provider involvement. High-risk engagements with significant liability exposure justify specialized verification services.
Volume thresholds make outsourcing economical when internal staff time and overhead exceed provider costs. Technology capabilities offered by specialized providers may exceed internal systems. These include advanced identity verification, continuous monitoring, international database access, and workflow management platforms.
Hybrid Approaches and Vendor Management
Tiered verification frameworks often combine internal baseline checks with provider-assisted enhanced screening. Routine identity verification, reference checks, and sanctions screening performed internally escalate to external providers when needed. This escalation occurs for international record searches, complex credential validation, or adverse information investigation.
Vendor management protocols ensure provider quality, compliance, and appropriate use. Contracts should specify data handling requirements, accuracy standards, and dispute resolution mechanisms. Regular provider performance review identifies quality issues, accuracy problems, or compliance gaps. This review monitors turnaround times, error rates, and audit findings.
Conclusion
Conducting a background check for remote contractors requires a risk-based approach that accounts for jurisdictional limitations, worker classification boundaries, and data privacy requirements. Verification frameworks should align with role risk, contract exposure, and realistic data availability rather than applying uniform standards across diverse contractor relationships.
Frequently Asked Questions
What is the difference between a background check for remote contractors and employee screening?
Background check requirements for contractors differ from employee screening due to the nature of the relationship and applicable legal frameworks. Contractors maintain greater autonomy and may not be subject to requirements under employment-related laws such as the Fair Credit Reporting Act. Verification scope should align with contractual risk exposure rather than employment standards.
Can I require criminal background checks for international freelancers?
Criminal background check availability for international freelancers depends entirely on the contractor's location and relevant jurisdictions. Many countries restrict or prohibit private-sector access to criminal records. Some require contractors to request records directly from government agencies. Requiring criminal checks may violate local law or exceed appropriate verification scope depending on role risk.
How do I verify identity for a remote worker abroad I have never met?
Identity verification for remote workers abroad typically combines government-issued identification document review with liveness detection technology. Document authentication services evaluate security features and detect common forgeries. Video verification or biometric matching confirms the individual presenting the document is its rightful holder. Additional steps may include video interviews and verification of professional online presence.
Are digital nomads subject to FCRA when I conduct screening?
The Fair Credit Reporting Act applies when an employer uses a consumer reporting agency to obtain a consumer report for employment purposes. Whether FCRA applies to digital nomad screening depends on the nature of the relationship. It also depends on whether the individual is properly classified as an employee or independent contractor. Contractor relationships generally fall outside FCRA scope, but misclassification creates compliance risk.
What privacy laws apply when screening overseas independent contractors?
Privacy law applicability when screening overseas independent contractors depends on the contractor's location, the organization's location, and where data is processed. GDPR applies when processing personal data of individuals in the European Union regardless of where the requesting organization is located. Similar comprehensive privacy laws in California, Canada, Brazil, the United Kingdom, and other jurisdictions impose consent, purpose limitation, data minimization, and security requirements.
How do I verify education credentials from foreign universities?
Education credential verification from foreign universities requires direct outreach to issuing institutions when possible. Response rates and processes vary significantly by country and institution. Credential evaluation services maintain databases of accredited institutions and known diploma mills. They provide legitimacy assessments when direct verification is not feasible. For specialized or high-risk roles, requiring contractors to obtain official transcripts provides additional validation.
What are lookback periods for international criminal records?
Lookback periods for international criminal records vary by jurisdiction and are determined by local law rather than the requesting party's preferences. Some countries automatically expunge certain convictions after rehabilitation periods, limit disclosure timeframes, or prohibit use of older records. Organizations conducting international freelancer verification must respect local lookback limitations.
Should I use the same screening process for all remote contractors regardless of location?
Uniform screening processes for all remote contractors regardless of location create inefficiency and legal risk. Verification capabilities, data availability, privacy requirements, and cost vary significantly by jurisdiction. This makes standardized approaches impractical. Risk-based frameworks that align verification intensity with role requirements, access level, and contract value provide more effective and compliant screening.
Additional Resources
- Fair Credit Reporting Act Full Text and Compliance Guide
https://www.ftc.gov/legal-library/browse/statutes/fair-credit-reporting-act - EEOC Guidance on Arrest and Conviction Records in Employment
https://www.eeoc.gov/laws/guidance/enforcement-guidance-consideration-arrest-and-conviction-records-employment - General Data Protection Regulation (GDPR) Official Text
https://gdpr-info.eu/ - IRS Independent Contractor vs. Employee Classification Guidance
https://www.irs.gov/businesses/small-businesses-self-employed/independent-contractor-self-employed-or-employee - Office of Foreign Assets Control Sanctions Programs and Information
https://ofac.treasury.gov/sanctions-programs-and-country-information - Department of Labor Misclassification Guidance
https://www.dol.gov/agencies/whd/flsa/misclassification

Charm Paz, CHRP
Recruiter & Editor
Charm Paz is an HR and compliance professional at GCheck, working at the intersection of background screening, fair hiring, and regulatory compliance. She holds both FCRA Core and FCRA Advanced certifications through the Professional Background Screening Association (PBSA) and supports organizations in navigating complex employment regulations with clarity and confidence.
With a background in Industrial and Organizational Psychology and hands-on experience translating policy into practice, Charm focuses on building ethical, compliant, and human-centered hiring systems that strengthen decision-making and support long-term organizational health.